WPDevs Classic Editor & Widgets Security & Risk Analysis
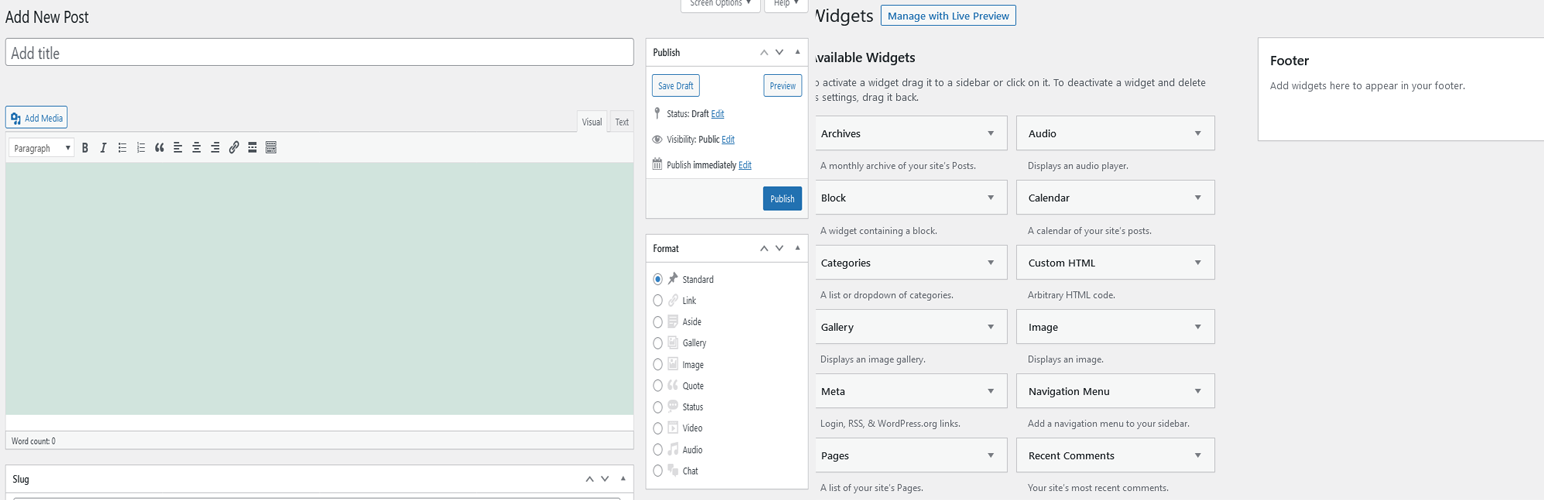
wordpress.org/plugins/wpdevs-classic-editor-widgetsWPDevs Classic Editor & Widgets enables the traditional WordPress classic editor, classic widgets, and the previous version of the Edit Post scree …
Is WPDevs Classic Editor & Widgets Safe to Use in 2026?
Generally Safe
Score 100/100WPDevs Classic Editor & Widgets has no known CVEs and is actively maintained. It's a solid choice for most WordPress installations.
The static analysis of wpdevs-classic-editor-widgets v1.0 reveals an exceptionally clean code base with no identified dangerous functions, SQL injection vulnerabilities, file operations, or external HTTP requests. The plugin also demonstrates excellent security practices by using prepared statements for all its SQL queries and properly escaping all outputs. Crucially, there are no identified taint flows, indicating that user-supplied data is not being processed in a way that could lead to vulnerabilities.
However, the complete absence of any security checks, including capability checks and nonce checks, across all potential entry points is a significant concern. While the current version has a zero attack surface in terms of AJAX handlers, REST API routes, and shortcodes, this could change with future updates. The lack of these fundamental security mechanisms means that if any entry points were to be introduced in the future, they would be entirely unprotected.
The plugin's vulnerability history is also spotless, with no known CVEs. This, combined with the clean code analysis, suggests a plugin that has been developed with care. However, the lack of any security checks remains a critical weakness that could be exploited if the plugin's functionality evolves to include user-interactive elements or administrative features.
Key Concerns
- Missing capability checks on all entry points
- Missing nonce checks on all entry points
WPDevs Classic Editor & Widgets Security Vulnerabilities
WPDevs Classic Editor & Widgets Release Timeline
WPDevs Classic Editor & Widgets Code Analysis
WPDevs Classic Editor & Widgets Attack Surface
WordPress Hooks 5
Maintenance & Trust
WPDevs Classic Editor & Widgets Maintenance & Trust
Maintenance Signals
Community Trust
WPDevs Classic Editor & Widgets Alternatives
Classic Editor and Classic Widgets
classic-editor-and-classic-widgets
Disables Gutenberg editor totally everywhere and enables Classic Editor and Classic Widgets.
Disable Block
disable-block-completely
Disable Block disables Gutenberg editor and Gutenberg Block Library CSS totally everywhere and enables Classic Editor & Classic Widgets.
Classic Widgets
classic-widgets
Enables the previous "classic" widgets settings screens in Appearance - Widgets and the Customizer. Disables the block editor from managing widgets.
Classic Editor +
classic-editor-addon
The "Classic Editor +" plugin disables the block editor, removes enqueued scripts/styles and brings back classic Widgets.
Enable Classic Editor & Widgets
enable-classic-editor
A simple & lightweight plugin to enable the classic editor on WordPress with advanced configuration options.
WPDevs Classic Editor & Widgets Developer Profile
1 plugin · 10 total installs
How We Detect WPDevs Classic Editor & Widgets
Patterns used to identify this plugin on WordPress sites during automated security audits and web crawling.
Asset Fingerprints
HTML / DOM Fingerprints
name="wpdevs_classic_editor_settings[disable_gutenberg]"name="wpdevs_classic_editor_settings[disable_gutenberg_widgets]"