Guest Support Security & Risk Analysis
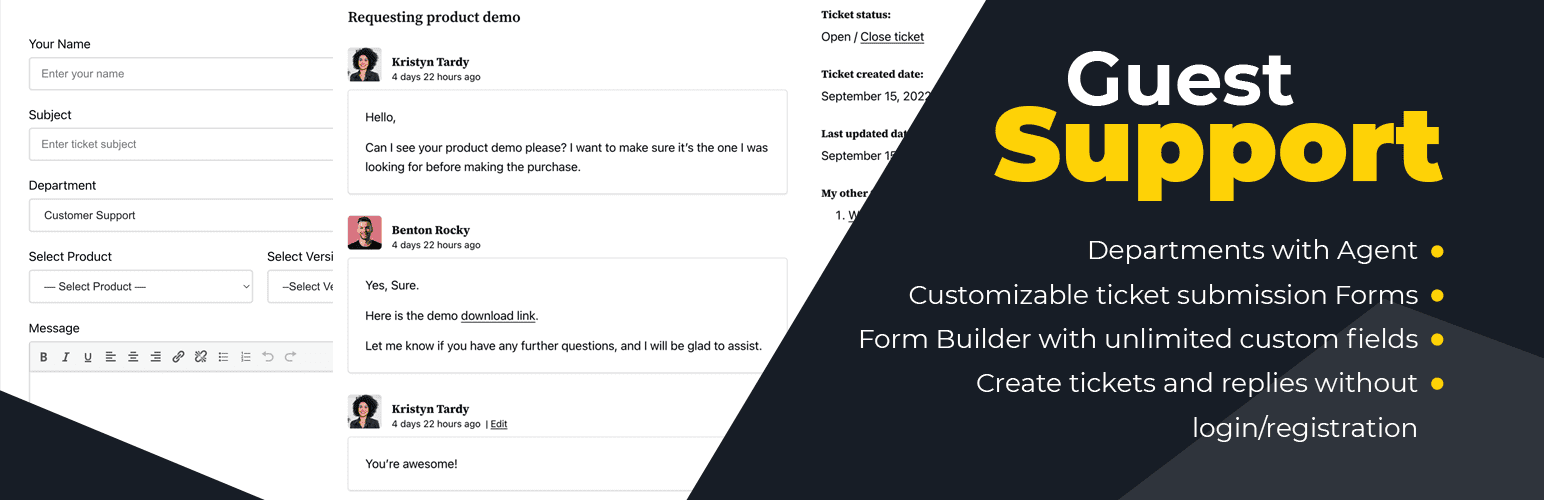
wordpress.org/plugins/guest-supportComplete WordPress support ticket system. No login needed for users or agents. Includes spam protection, file uploads, and secure replies.
Is Guest Support Safe to Use in 2026?
Generally Safe
Score 98/100Guest Support has a strong security track record. Known vulnerabilities have been patched promptly. It's a solid choice for most WordPress installations.
The "guest-support" plugin v1.3.0 presents a mixed security posture. On the positive side, the plugin exhibits strong adherence to secure coding practices, with a high percentage of SQL queries using prepared statements and a vast majority of output being properly escaped. It also demonstrates robust use of nonces and capability checks, and importantly, has no unpatched known vulnerabilities despite a history of CVEs.
However, there are significant concerns. The presence of 11 dangerous function calls, specifically `unserialize`, is a critical red flag. This function is notoriously risky when handling user-supplied data, as it can lead to Remote Code Execution vulnerabilities if not strictly controlled. Furthermore, the taint analysis revealed 4 flows with unsanitized paths, all flagged as High severity, indicating potential for these dangerous functions to be exploited with malicious input.
The plugin's vulnerability history, while currently clear of unpatched issues, shows past occurrences of 'Exposure of Sensitive Information' and 'Missing Authorization'. This pattern suggests that while the developers have addressed past issues, the underlying coding practices might still be prone to introducing such vulnerabilities, especially concerning how data is handled and access is controlled.
Key Concerns
- Dangerous function calls (unserialize)
- High severity unsanitized taint flows
- Past vulnerabilities: Exposure of Sensitive Info
- Past vulnerabilities: Missing Authorization
Guest Support Security Vulnerabilities
CVEs by Year
Severity Breakdown
2 total CVEs
Guest Support <= 1.2.3 - Unauthenticated User Email Disclosure in guest_support_handler AJAX Endpoint
Guest Support – Complete customer support ticket system for WordPress <= 1.2.2 - Missing Authorization to Unauthenticated Ticket Deletion
Guest Support Release Timeline
Guest Support Code Analysis
Dangerous Functions Found
SQL Query Safety
Output Escaping
Data Flow Analysis
Guest Support Attack Surface
Shortcodes 1
WordPress Hooks 10
Maintenance & Trust
Guest Support Maintenance & Trust
Maintenance Signals
Community Trust
Guest Support Alternatives
Customer Support Ticket System & Helpdesk Plugin for WordPress
wp-ticket
Create a support ticket system in WordPress. Manage customer inquiries, agents, priorities, and more with this flexible helpdesk plugin.
Order Sync with Zendesk for WooCommerce
mwb-zendesk-woo-order-sync
Manage Customer Support Tickets and Orders with Zendesk Woo Order Sync
CodeBard Help Desk
codebard-help-desk
Multi Language Professional Support Ticket System with Unlimited Users, Unlimited Tickets, Unlimited Departments, Agents and many features
Fluent Support – Helpdesk & Customer Support Ticket System
fluent-support
Feature Rich and Super Fast Support and Customer Ticketing System for WordPress.
Live Chat with Messenger Customer Chat
fb-messenger-live-chat
Support your customers via Facebook Messenger Live Chat conveniently from your own website.
Guest Support Developer Profile
1 plugin · 40 total installs
How We Detect Guest Support
Patterns used to identify this plugin on WordPress sites during automated security audits and web crawling.
Asset Fingerprints
/wp-content/plugins/guest-support/assets/admin.css/wp-content/plugins/guest-support/assets/admin.js/wp-content/plugins/guest-support/assets/dragndrop.js/wp-content/plugins/guest-support/assets/styles.min.css/wp-content/plugins/guest-support/assets/scripts.min.js/wp-content/plugins/guest-support/assets/admin.js/wp-content/plugins/guest-support/assets/dragndrop.js/wp-content/plugins/guest-support/assets/scripts.min.jsguest-support/assets/admin.css?ver=guest-support/assets/admin.js?ver=guest-support/assets/dragndrop.js?ver=guest-support/assets/styles.min.css?ver=guest-support/assets/scripts.min.js?ver=HTML / DOM Fingerprints
GuestSupportApp[guest-support]