Seven days, two critical CVEs, and a dozen high-severity findings across plugins collectively installed on millions of sites. Most of them are patched already, which is the good news. The bad news is that a popular caching plugin with 900,000 active installs is carrying its 29th known CVE, and a contact form plugin has an unpatched medium-severity bug sitting alongside its shiny new critical patch. Let's get into it.
Critical Severity (CVSS 9.8)
Everest Forms Pro — Unauthenticated Remote Code Execution
CVE-2026-3300 | CVSS 9.8 | Patched in 1.9.13
This is the worst kind of vulnerability: unauthenticated, remote code execution, maximum CVSS score. The flaw lives in Everest Forms Pro's calculation field and allows anyone, no login required, to execute arbitrary code on the server. It affects all versions up to and including 1.9.12.
Everest Forms Pro is a premium plugin so it doesn't appear in our database with an install count, but it has a substantial user base in the WordPress form builder market. If you're running it, you needed to be on 1.9.13 yesterday. There's no viable workaround here short of deactivating the plugin entirely until you can update.
Contact Form by Supsystic — Unauthenticated Server-Side Template Injection

CVE-2026-4257 | CVSS 9.8 | Patched in 1.8.0
Contact Form by Supsystic (7,000 active installs) has a server-side template injection (SSTI) flaw in its prefill functionality. SSTI vulnerabilities are effectively code execution by another name: an attacker can inject template syntax and get the server to evaluate it. No authentication needed.
The fix landed in 1.8.0, and the developer patched within a day of disclosure. The problem is that this plugin has a security score of 52/100 in our database and 10 total CVEs, including one that's still unpatched (a reflected XSS from August 2025 that has no fix yet). The install count is small, but the security track record here is genuinely rough. Average patch time for the developer sits at 597 days historically. This week's quick turnaround is good, but the overall picture warrants caution.
High Severity — The Ones That Matter Most by Scale
W3 Total Cache — Unauthenticated Security Token Exposure

CVE-2026-5032 | CVSS 7.5 | Patched in 2.9.4
W3 Total Cache is installed on roughly 900,000 sites, making it the highest-reach plugin in this week's roundup. The vulnerability allows any unauthenticated visitor to extract a security token by manipulating the User-Agent header. Depending on how that token is used downstream, this can open the door to further attacks.
This is CVE number 29 for W3 Total Cache. That's not a typo. The plugin was also hit with a critical RCE (CVSS 9.8) back in February 2026, and an unauthenticated command injection in October 2025. At some point the frequency of severe findings in a single codebase stops being bad luck and starts being a structural problem. The patch is available in 2.9.4 and you should update immediately.
MW WP Form — Unauthenticated Arbitrary File Move

CVE-2026-4347 | CVSS 8.1 | Patched in 5.1.1
MW WP Form has 200,000 active installs and a path traversal vulnerability in its move_temp_file_to_upload_dir function. An unauthenticated attacker can move arbitrary files into the upload directory. Depending on server configuration, this could be a stepping stone to webshell placement.
This plugin has a recurring problem with file handling: it's now on its third path traversal CVE, following an arbitrary file deletion bug in December 2023 and an arbitrary file upload (CVSS 9.8) the same month. The current version is patched, but the pattern here is worth paying attention to if you're making long-term plugin choices. Update to 5.1.1.
ProfilePress — Missing Authorization to Payment Bypass
![]()
CVE-2026-3445 | CVSS 7.1 | Patched in 4.16.12
ProfilePress runs on 100,000 sites as a full membership and ecommerce platform. A missing authorization check lets any authenticated user (subscriber-level) bypass payment for memberships. For any site selling access-controlled content or subscriptions, that's a direct revenue and access-control problem.
The same update (4.16.12) also patches an unauthenticated shortcode execution bug (CVE-2026-3309, CVSS 6.5). ProfilePress has 41 total CVEs in our database, including 4 critical and 5 high severity. It patches consistently (usually within a day), but the volume of findings is high enough that staying current is non-negotiable. Get to 4.16.12.
wpForo Forum — Authenticated Arbitrary File Deletion

CVE-2026-3666 | CVSS 8.8 | Patched in 2.4.17
wpForo Forum (20,000 installs) lets any subscriber-level user delete arbitrary files through the post body via a path traversal flaw. On a forum plugin where user registration is the whole point, "subscriber+" means basically anyone with an account.
wpForo's track record over the past six months has been brutal: unauthenticated SQL injection, PHP object injection, more SQL injection, and now file deletion. That's 35 total CVEs, 4 of them critical. The developer does patch quickly, but the pattern of findings suggests the codebase needs a more thorough audit rather than just reactive patching. Updated to 2.4.17.
WCFM WooCommerce Frontend Manager — Authorization Bypass in Vendor Role

CVE-2026-4896 | CVSS 8.1 | Patched in 6.7.26
WCFM Frontend Manager (20,000 installs) has an IDOR vulnerability that lets authenticated vendor-level users manipulate posts and products they don't own. On a multi-vendor WooCommerce marketplace, vendors are unprivileged third parties, so this is a real business logic problem: a vendor could modify or delete a competitor's listings.
Patch is in 6.7.26. The developer turned it around in one day.
Query Monitor — Reflected XSS via Request URI
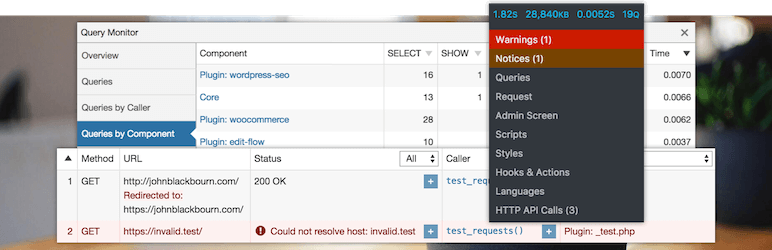
CVE-2026-4267 | CVSS 7.2 | Patched in 3.20.4
Query Monitor is a developer tool sitting on 200,000 sites, often used in staging and production environments alike. A reflected XSS in the request URI handling means a crafted URL could execute JavaScript in an admin's browser, which is the typical vector for cookie theft or admin-level account takeover.
This is actually the plugin's first ever CVE, and the developer patched it in a single day. Query Monitor has a security score of 97/100 in our database, so this looks like an isolated miss rather than a systemic problem. Still, if you use it on production, update to 3.20.4.
Download Monitor — Unauthenticated Order Completion Bypass

CVE-2026-3124 | CVSS 7.5 | Patched in 5.1.8
Download Monitor (90,000 installs) has an IDOR that lets unauthenticated users complete arbitrary orders by guessing or enumerating a token and order_id combination. If you're selling digital downloads through this plugin, an attacker could mark purchases as complete without paying.
Fixed in 5.1.8, patched within one day of disclosure.
Visitor Traffic Real Time Statistics — Unauthenticated Stored XSS

CVE-2026-2936 | CVSS 7.2 | Patched in 8.5
Visitor Traffic Real Time Statistics has 40,000 active installs and a stored XSS that requires zero authentication. An attacker can inject a malicious payload via a page visit, and the plugin stores it for display in the admin dashboard. When an admin views their traffic stats, the script runs in their browser.
This is a classic attack chain: no-auth write access to an admin-visible data store. Update to version 8.5.
What to Do Right Now
Prioritize these updates by install count and CVSS score:
- W3 Total Cache (900,000 installs) → update to 2.9.4 (token exposure, CVSS 7.5)
- MW WP Form (200,000 installs) → update to 5.1.1 (unauthenticated file move, CVSS 8.1)
- Query Monitor (200,000 installs) → update to 3.20.4 (reflected XSS, CVSS 7.2)
- ProfilePress (100,000 installs) → update to 4.16.12 (payment bypass, CVSS 7.1)
- Download Monitor (90,000 installs) → update to 5.1.8 (order bypass, CVSS 7.5)
- Visitor Traffic Real Time Statistics (40,000 installs) → update to 8.5 (stored XSS, CVSS 7.2)
- wpForo Forum (20,000 installs) → update to 2.4.17 (file deletion, CVSS 8.8)
- WCFM Frontend Manager (20,000 installs) → update to 6.7.26 (IDOR, CVSS 8.1)
- Contact Form by Supsystic (7,000 installs) → update to 1.8.0 (SSTI, CVSS 9.8) and note the still-unpatched reflected XSS from 2025
If you're running Everest Forms Pro, update to 1.9.13 immediately. There's an unauthenticated RCE at CVSS 9.8 sitting in anything older.
For sites running W3 Total Cache specifically: this is its third high-or-critical CVE in the past six months. It's worth auditing whether your caching strategy depends on features unique to this plugin, or whether an alternative with a cleaner track record fits your stack.
