Yabe Kokoro Security & Risk Analysis
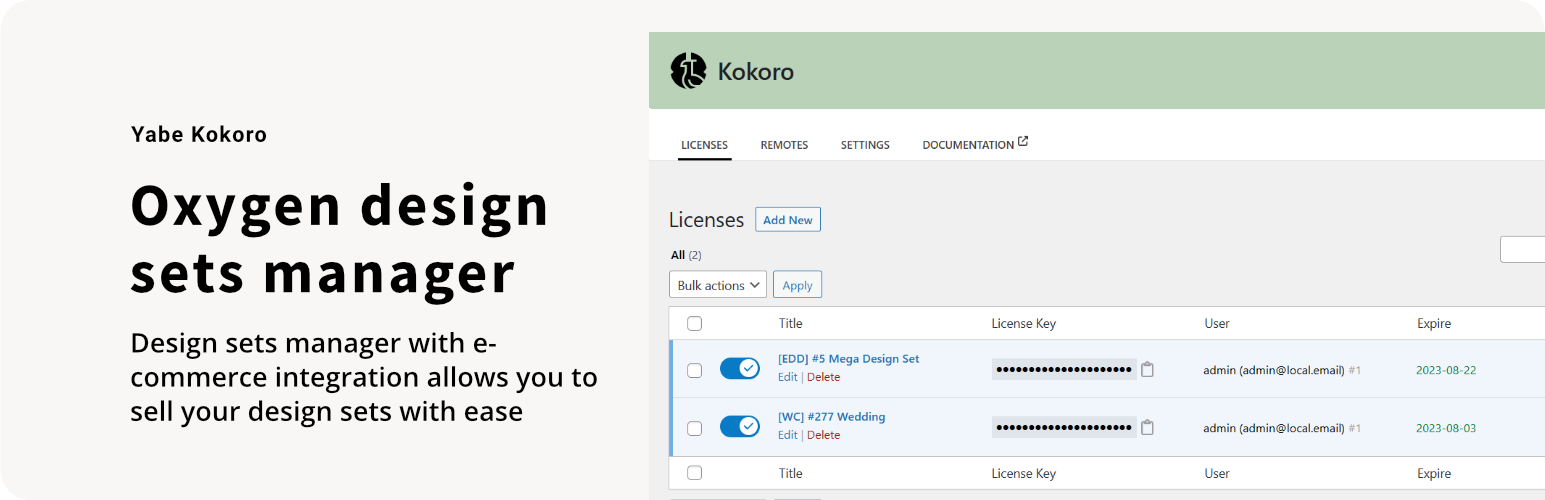
wordpress.org/plugins/yabe-kokoroOxygen design sets manager.
Is Yabe Kokoro Safe to Use in 2026?
Generally Safe
Score 85/100Yabe Kokoro has no known CVEs and is actively maintained. It's a solid choice for most WordPress installations.
The "yabe-kokoro" plugin version 1.0.7 exhibits a generally good security posture based on the provided static analysis and vulnerability history. The absence of any known CVEs, critical taint flows, dangerous functions, file operations, or external HTTP requests suggests a well-developed and secure codebase. The high percentage of SQL queries using prepared statements is also a positive indicator, mitigating risks of SQL injection. The plugin also lacks a significant attack surface, with no exposed AJAX handlers, REST API routes, shortcodes, or cron events, further enhancing its security.
However, there are significant concerns regarding output escaping. With 100% of outputs not properly escaped, this presents a considerable risk of Cross-Site Scripting (XSS) vulnerabilities. This is a critical oversight that could allow attackers to inject malicious scripts into the website, impacting users and potentially compromising data. Furthermore, the complete absence of nonce checks and capability checks on potential entry points, though currently zero, means that if any were to be introduced in the future, they would be unprotected, leaving them vulnerable. The lack of any recorded vulnerability history is reassuring but doesn't entirely absolve the plugin from potential future issues, especially given the output escaping deficiency.
Key Concerns
- Outputs are not properly escaped
- No nonce checks on potential entry points
- No capability checks on potential entry points
Yabe Kokoro Security Vulnerabilities
Yabe Kokoro Release Timeline
Yabe Kokoro Code Analysis
SQL Query Safety
Output Escaping
Yabe Kokoro Attack Surface
Maintenance & Trust
Yabe Kokoro Maintenance & Trust
Maintenance Signals
Community Trust
Yabe Kokoro Alternatives
Starter Templates – AI-Powered Templates for Elementor & Gutenberg
astra-sites
The growing library of 300+ ready-to-use templates that work with all WordPress themes including Astra, Hello, OceanWP, GeneratePress and more
Essential Addons for Elementor – Popular Elementor Templates & Widgets
essential-addons-for-elementor-lite
Elementor addon offering 110+ widgets and templates — Elementor Gallery, Slider, Form, Post Grid, Menu, Accordion, WooCommerce & more.
Ultimate Addons for Elementor
header-footer-elementor
Powerful Elementor addon with advanced Elementor widgets, templates, WooCommerce widgets & Header-Footer builder to build professional websites fa …
Premium Addons for Elementor – Powerful Elementor Templates & Widgets
premium-addons-for-elementor
Elementor Carousel, Mega Menu, Posts List/Slider, Media Gallery, WooCommerce Widgets, Display Conditions, Premade Templates & more.
Royal Addons for Elementor – Addons and Templates Kit for Elementor
royal-elementor-addons
Elementor templates, Header footer builder, Elementor Post Grid, Woocommerce Grid builder, Slider, Forms, Gallery, Nav menu addons, Elementor widgets.
Yabe Kokoro Developer Profile
4 plugins · 130 total installs
How We Detect Yabe Kokoro
Patterns used to identify this plugin on WordPress sites during automated security audits and web crawling.
Asset Fingerprints
/wp-content/plugins/yabe-kokoro/build/index.css/wp-content/plugins/yabe-kokoro/build/index.js/wp-content/plugins/yabe-kokoro/build/index.jsyabe-kokoro/build/index.css?ver=yabe-kokoro/build/index.js?ver=HTML / DOM Fingerprints
yabe-kokorodata-yabe-kokoro/wp-json/yabe-kokoro/admin/licenses/index/wp-json/yabe-kokoro/admin/licenses/store/wp-json/yabe-kokoro/admin/licenses/update-status/(?P<id>\d+)/wp-json/yabe-kokoro/admin/licenses/delete/(?P<id>\d+)/wp-json/yabe-kokoro/admin/licenses/detail/(?P<id>\d+)/wp-json/yabe-kokoro/admin/licenses/update/(?P<id>\d+)/wp-json/yabe-kokoro/admin/licenses/search_user/wp-json/yabe-kokoro/admin/licenses/sites/(?P<id>\d+)