WoWpi Security & Risk Analysis
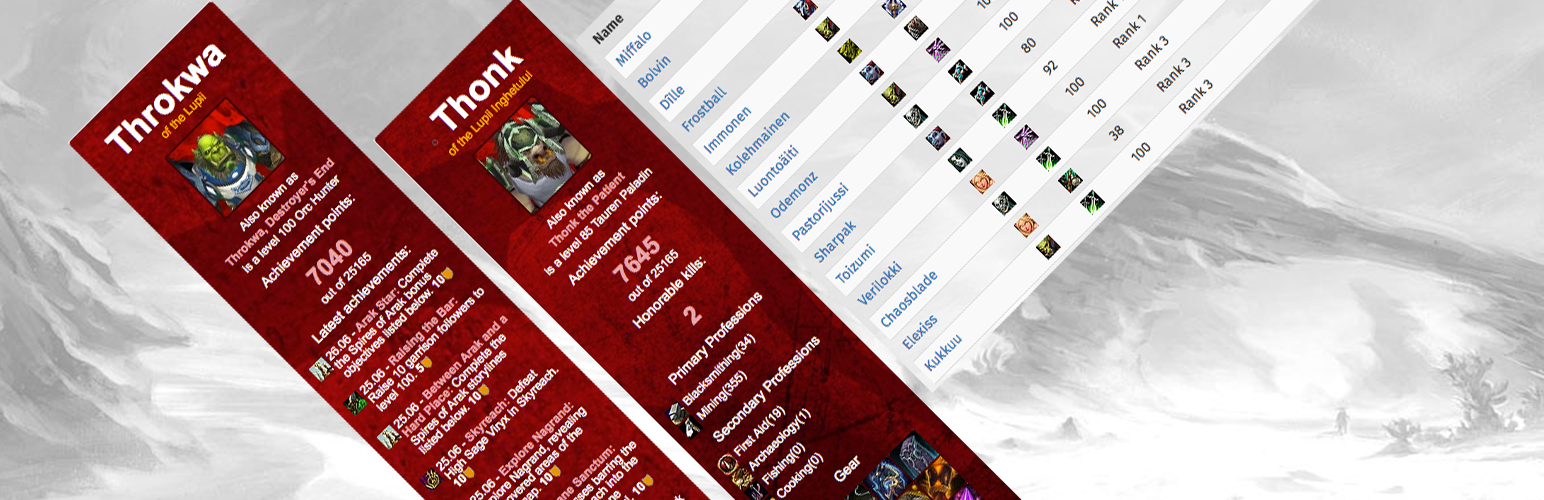
wordpress.org/plugins/wowpiThe WoWpi plugin allows you to retrieve data from Battle.net API regarding your World of Warcraft character and/or guild.
Is WoWpi Safe to Use in 2026?
Generally Safe
Score 85/100WoWpi has no known CVEs and is actively maintained. It's a solid choice for most WordPress installations.
The "wowpi" plugin v2.5.2 exhibits a generally good security posture based on the provided static analysis and vulnerability history. The absence of known CVEs and critical taint flows is a significant positive indicator. The plugin demonstrates good practices in SQL query handling, with 100% of queries utilizing prepared statements, and a healthy number of output operations are properly escaped. However, several areas raise concerns that temper this positive outlook. The lack of nonce checks and capability checks across all entry points is a significant weakness, potentially exposing the plugin to various attack vectors if any of its entry points were to be manipulated. Additionally, the moderate output escaping rate suggests a risk of Cross-Site Scripting (XSS) vulnerabilities if user-supplied data is not handled carefully in the 47% of outputs that are not properly escaped. The file operations and external HTTP requests, while not explicitly flagged as problematic in the static analysis, warrant careful review in the context of the overall security.
While the plugin has no recorded vulnerability history, this does not guarantee future security. The absence of known vulnerabilities could be due to a lack of thorough historical analysis of the plugin itself, or simply that no exploitable vulnerabilities have been discovered and reported. The total entry points are manageable, and all appear to be protected by some form of authentication or authorization, which is a positive sign. However, the absence of specific nonce and capability checks on these entry points is a critical oversight that significantly increases the risk profile. The plugin's strengths lie in its secure SQL handling and the absence of critical taint flows and CVEs. Its weaknesses are primarily in the lack of granular access control mechanisms like nonce and capability checks, and the moderate output escaping rate.
Key Concerns
- No nonce checks found
- No capability checks found
- Moderate output escaping (53%)
WoWpi Security Vulnerabilities
WoWpi Release Timeline
WoWpi Code Analysis
Output Escaping
WoWpi Attack Surface
Shortcodes 6
WordPress Hooks 6
Maintenance & Trust
WoWpi Maintenance & Trust
Maintenance Signals
Community Trust
WoWpi Alternatives
WoW Armory
wow-armory
Easily displays your character's stats from the Armory.
WoW Guild
wow-guild
Easily displays your Guild's Roster from the armory
WoWpi Guild
wowpi-guild
You want a proper World of Warcraft's guild website but you don't know how? Look no further. This is the plugin for your guild's needs.
WoW Progress
wow-progress
A widget that helps to display guild raid progress.
WOW Recruitment Widget
wow-recruit-widget
A widget that helps to display recruitment message of a World of Warcraft guild, also can be used for other games that have different classes.
WoWpi Developer Profile
2 plugins · 30 total installs
How We Detect WoWpi
Patterns used to identify this plugin on WordPress sites during automated security audits and web crawling.
Asset Fingerprints
/wp-content/plugins/wowpi/assets/css/wowpi_faction.css/wp-content/plugins/wowpi/assets/css/wowpi_light.css/wp-content/plugins/wowpi/assets/css/wowpi_dark.css/wp-content/plugins/wowpi/assets/js/wowpi.js//wow.zamimg.com/widgets/power.js//static-azeroth.cursecdn.com/current/js/syndication/tt.js//cdn.datatables.net/1.10.12/js/jquery.dataTables.min.jswowpi/assets/js/wowpi.js?ver=