WebDigit LLMs Index Suite Security & Risk Analysis
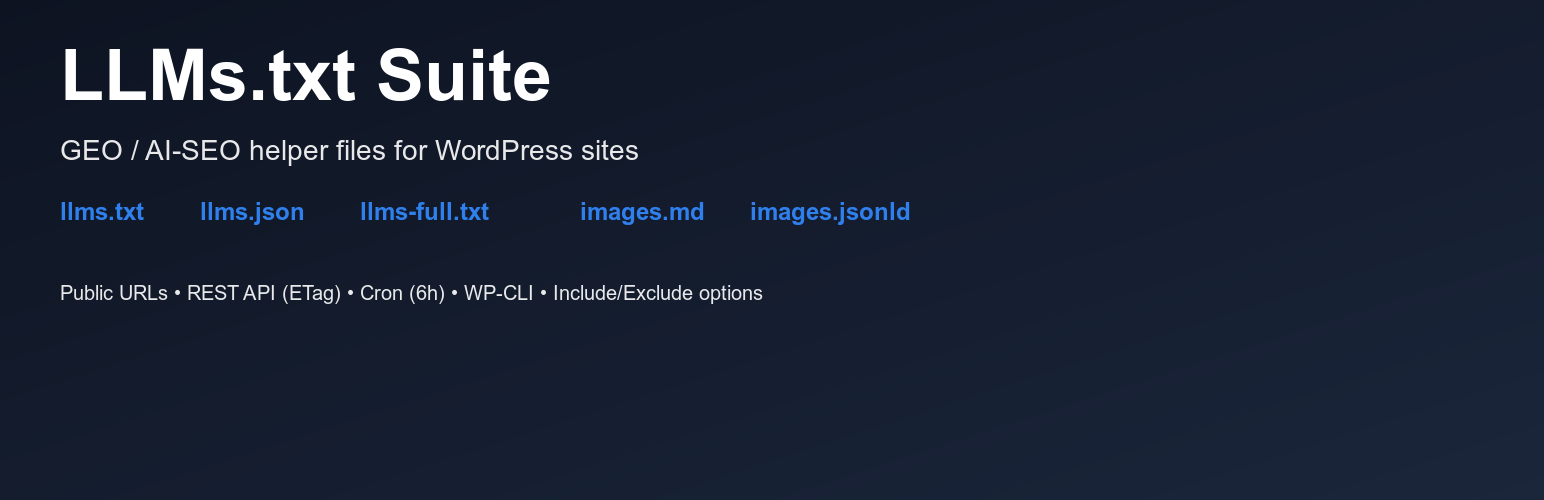
wordpress.org/plugins/webdigit-llms-index-suiteGenerate llms.txt, llms-full.txt, llms.json and AI-ready image indexes (Markdown + JSON-LD). Public URLs, REST API (ETag), cron and WP-CLI included.
Is WebDigit LLMs Index Suite Safe to Use in 2026?
Generally Safe
Score 100/100WebDigit LLMs Index Suite has no known CVEs and is actively maintained. It's a solid choice for most WordPress installations.
The webdigit-llms-index-suite plugin, in version 0.2.29, exhibits a mixed security posture. On the positive side, it demonstrates good practices by not containing dangerous functions, not executing raw SQL queries, and properly escaping a high percentage of its outputs. The absence of file operations and external HTTP requests is also a strong point. Furthermore, the plugin has no recorded vulnerabilities or CVEs, suggesting a history of security diligence or a lack of prior significant issues.
However, there are notable concerns regarding its attack surface. A significant portion of its entry points, specifically 4 out of 5, are unprotected by authentication or permission checks. This includes all 4 REST API routes, which could potentially be exploited by unauthenticated users to access or manipulate data. While taint analysis shows no critical or high severity unsanitized paths, the large number of unprotected entry points, especially REST API endpoints, presents a substantial risk of unauthorized access or denial-of-service attacks if not properly secured at the application level or via WordPress's built-in access controls.
In conclusion, while the plugin's code quality in terms of SQL handling, output escaping, and avoidance of dangerous functions is commendable, the significant unauthenticated attack surface is a critical weakness. The lack of past vulnerabilities is a positive indicator, but it doesn't negate the immediate risk posed by the unprotected REST API routes. Mitigation strategies should focus on ensuring proper authorization for these endpoints.
Key Concerns
- REST API routes without permission callbacks
- AJAX handlers without auth checks
- High percentage of unprotected entry points
WebDigit LLMs Index Suite Security Vulnerabilities
WebDigit LLMs Index Suite Release Timeline
WebDigit LLMs Index Suite Code Analysis
Output Escaping
Data Flow Analysis
WebDigit LLMs Index Suite Attack Surface
AJAX Handlers 1
REST API Routes 4
WordPress Hooks 13
Maintenance & Trust
WebDigit LLMs Index Suite Maintenance & Trust
Maintenance Signals
Community Trust
WebDigit LLMs Index Suite Alternatives
CLOUDCUSP LLMS.txt Generator
cloudcusp-llms-txt-generator
Generate AI-friendly LLMS.txt files for your WordPress site with modern UI/UX and comprehensive bot analytics.
Markdown Mirror – llms.txt and .md always up to date
markdown-mirror
Generate an llms.txt map and dynamic Markdown (.md) versions of every page of your site to improve your AI SEO and facilitate LLMs indexing.
GEO Pilot – AI Search Optimization & llms.txt
geo-pilot
Prepare your WordPress site for the AI Search era. Auto-generate a dynamic llms.txt file, optimize content for tokens, and rank in AI Overviews.
Prime SEO
prime-seo
SEO for the AI Era. LLMs.txt, AI Bots Manager, Schema, Sitemap — optimize for Google, ChatGPT, Perplexity & Claude. AI meta generation (Pro).
IA SEO Generator
ia-seo-generator
Make your site visible to AI: serve an AI-ready /llms.txt (no root). Appear in answers on ChatGPT, Perplexity, Claude, Gemini, Copilot, Comet.
WebDigit LLMs Index Suite Developer Profile
4 plugins · 100 total installs
How We Detect WebDigit LLMs Index Suite
Patterns used to identify this plugin on WordPress sites during automated security audits and web crawling.
Asset Fingerprints
/wp-content/plugins/webdigit-llms-index-suite/admin/css/settings.css/wp-content/plugins/webdigit-llms-index-suite/admin/js/settings.jswebdigit-llms-index-suite/admin/css/settings.css?ver=webdigit-llms-index-suite/admin/js/settings.js?ver=HTML / DOM Fingerprints
data-wp-nonceWDLIS/wp-json/wdlis/v1/settings