User Menu Customizer for HivePress Security & Risk Analysis
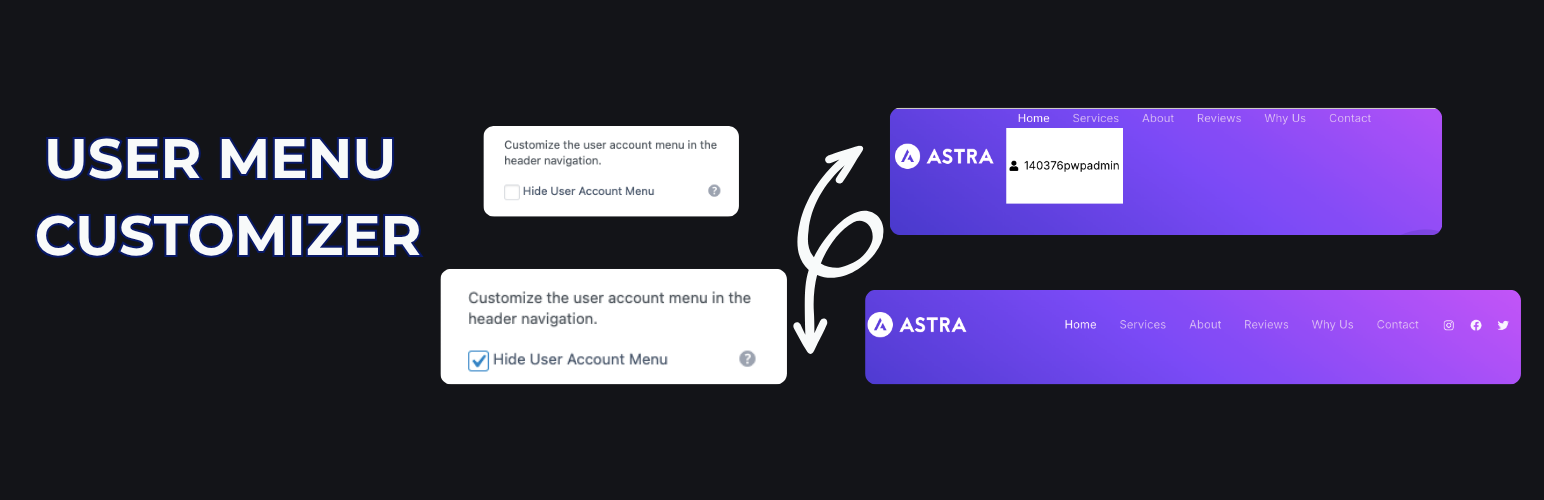
wordpress.org/plugins/user-menu-customizer-for-hivepressEasily customize or hide the user menu for HivePress in the header navigation using the WordPress Customizer.
Is User Menu Customizer for HivePress Safe to Use in 2026?
Generally Safe
Score 100/100User Menu Customizer for HivePress has no known CVEs and is actively maintained. It's a solid choice for most WordPress installations.
The user-menu-customizer-for-hivepress plugin exhibits a strong security posture based on the provided static analysis. There are no identified AJAX handlers, REST API routes, shortcodes, or cron events, which significantly limits the potential attack surface. The code demonstrates excellent practices regarding SQL queries, all of which utilize prepared statements, and all output is properly escaped, mitigating risks of SQL injection and cross-site scripting. The absence of file operations, external HTTP requests, and bundled libraries further reduces the plugin's vulnerability footprint.
While the static analysis indicates a clean bill of health with no dangerous functions, taint flows, or known vulnerabilities in its history, the complete lack of nonce checks and capability checks is a notable concern. This absence means that even if the plugin had any entry points, they would not be protected by WordPress's standard security mechanisms, leaving them potentially open to unauthorized access or manipulation if an attack vector were to be discovered or introduced in future versions. The vulnerability history being entirely empty is a positive sign, suggesting a history of secure development, but it doesn't negate the current lack of authentication checks.
In conclusion, the plugin is well-coded with respect to preventing common web vulnerabilities like SQL injection and XSS. However, the complete absence of nonce and capability checks is a significant weakness that could be exploited if an attacker finds a way to interact with the plugin's components. While its current attack surface is zero, this lack of fundamental security checks represents a risk that should be addressed to ensure robust security for any future enhancements or potential discoveries.
Key Concerns
- No nonce checks implemented
- No capability checks implemented
User Menu Customizer for HivePress Security Vulnerabilities
User Menu Customizer for HivePress Release Timeline
User Menu Customizer for HivePress Code Analysis
Output Escaping
User Menu Customizer for HivePress Attack Surface
WordPress Hooks 2
Maintenance & Trust
User Menu Customizer for HivePress Maintenance & Trust
Maintenance Signals
Community Trust
User Menu Customizer for HivePress Alternatives
Customizer Hide Menu
so-customizer-hide-menu
Removes the Navigation Menu paqnel from the Customizer.
DanhThong Print Design Upload
danhthong-print-design-upload
Let customers upload an image, position it on a product canvas, and save the final design with the cart/order.
EPD Product Designer
epd-product-designer
Lightweight, accessible product designer for WordPress. Customize products with text and images on a drag-and-drop canvas. No WooCommerce required.
Menu Ghost
menu-ghost
Target menu items by role, device, schedule, and campaign rules using a fast, native conditions interface inside the menu editor.
Pixobe Product Designer – WooCommerce Product Customizer
pixobe-product-designer
A WooCommerce product designer and product customizer that lets customers personalize products with text, images, optional AI-generated designs, and r …
User Menu Customizer for HivePress Developer Profile
2 plugins · 110 total installs
How We Detect User Menu Customizer for HivePress
Patterns used to identify this plugin on WordPress sites during automated security audits and web crawling.
Asset Fingerprints
/wp-content/plugins/user-menu-customizer-for-hivepress/style.cssuser-menu-customizer-for-hivepress/style.css?ver=1.0.1HTML / DOM Fingerprints
menu-item--user-accountmenu-item--user-loginhp-menu__item--user-accounthp-menu__item--user-loginhp-menu--user-account