Upload Add-on for Woocommerce Security & Risk Analysis
wordpress.org/plugins/upload-add-on-for-woocommerceUpload Add-on for Woocommerce
Is Upload Add-on for Woocommerce Safe to Use in 2026?
Generally Safe
Score 85/100Upload Add-on for Woocommerce has no known CVEs and is actively maintained. It's a solid choice for most WordPress installations.
The "upload-add-on-for-woocommerce" plugin v1.1.1 demonstrates a strong security posture based on the provided static analysis. The absence of any identified attack surface entries like AJAX handlers, REST API routes, shortcodes, or cron events is a significant positive. Furthermore, the code signals indicate good development practices, with no dangerous functions, all SQL queries using prepared statements, and no file operations or external HTTP requests. The presence of capability checks, even if only one is found, is also a good sign.
However, a notable concern arises from the output escaping, where only 55% of the 11 total outputs are properly escaped. This leaves a portion of the plugin's output potentially vulnerable to cross-site scripting (XSS) if user-supplied data is not adequately sanitized before being displayed. The lack of identified taint flows and vulnerability history suggests no known critical or high-severity issues at this time, but the partial output escaping remains a tangible risk. The absence of nonce checks is not explicitly flagged as a deduction because there are no AJAX handlers to protect, thus no immediate risk is evident from this specific finding in isolation.
In conclusion, while the plugin exhibits excellent fundamental security by minimizing its attack surface and using secure database practices, the partially unescaped output presents a clear, albeit potentially low to medium severity, risk. The lack of past vulnerabilities is encouraging, but the identified code signal weakness warrants attention. A thorough review of the output handling functions is recommended to ensure robust XSS protection.
Key Concerns
- Unescaped output detected (45%)
Upload Add-on for Woocommerce Security Vulnerabilities
Upload Add-on for Woocommerce Release Timeline
Upload Add-on for Woocommerce Code Analysis
Output Escaping
Upload Add-on for Woocommerce Attack Surface
WordPress Hooks 20
Maintenance & Trust
Upload Add-on for Woocommerce Maintenance & Trust
Maintenance Signals
Community Trust
Upload Add-on for Woocommerce Alternatives
File Uploads Addon for WooCommerce
woo-addon-uploads
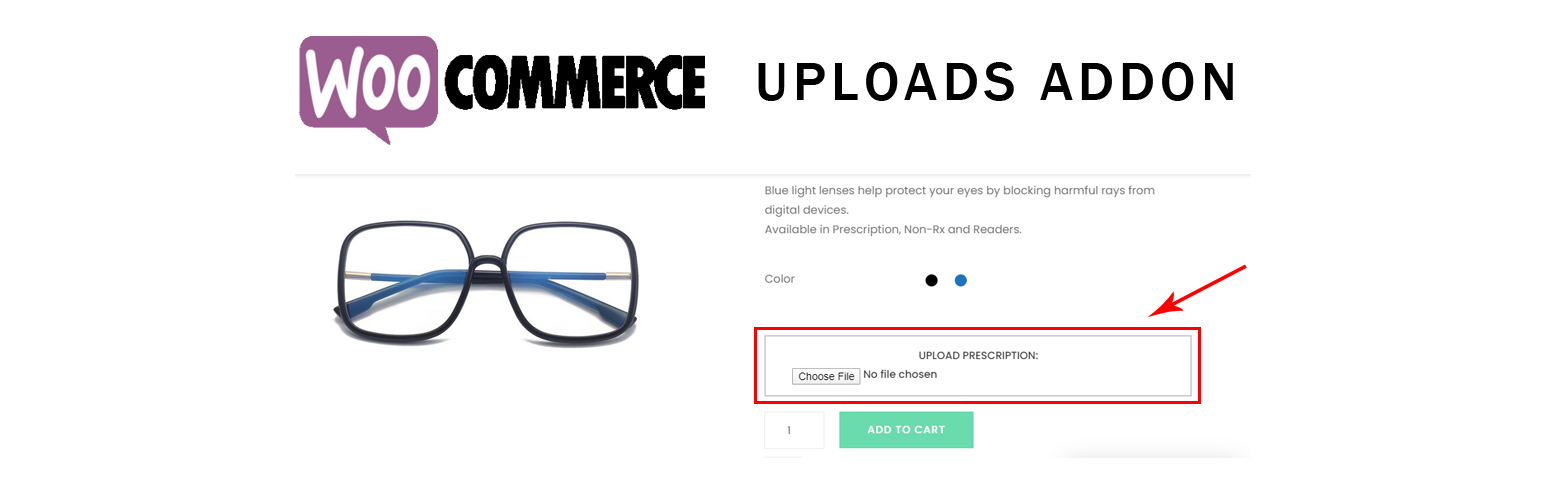
Let customers upload files directly on your WooCommerce product page — no more chasing emails for artwork, logos, prescriptions, or documents.
Product Add-Ons, Custom Fields, Booking & Extra Options for WooCommerce
product-add-ons-custom-fields-booking-extra-options-for-woocommerce
Create WooCommerce product addons, custom fields, and booking inputs. Perfect for appointments, services, and custom product pages.
Product File Upload for WooCommerce
products-file-upload-for-woocommerce
Professional AJAX Drag & Drop file upload for WooCommerce product pages. Allow customers to upload images, documents, and files instantly.
File Upload For WooCommerce
file-upload-for-woocommerce
A plugin For Uploading The Files On Product Pages And Checkout Pages of WooCommerce. Admin have so many controls over the plugin with a beatiful UI
Essential Addons for Elementor – Popular Elementor Templates & Widgets
essential-addons-for-elementor-lite
Elementor addon offering 110+ widgets and templates — Elementor Gallery, Slider, Form, Post Grid, Menu, Accordion, WooCommerce & more.
Upload Add-on for Woocommerce Developer Profile
2 plugins · 20 total installs
How We Detect Upload Add-on for Woocommerce
Patterns used to identify this plugin on WordPress sites during automated security audits and web crawling.
Asset Fingerprints
/wp-content/plugins/upload-add-on-for-woocommerce/assets/css/woo_ua-admin.css/wp-content/plugins/upload-add-on-for-woocommerce/assets/js/admin.js/wp-content/plugins/upload-add-on-for-woocommerce/assets/js/admin.jsupload-add-on-for-woocommerce/assets/css/woo_ua-admin.css?ver=upload-add-on-for-woocommerce/assets/js/admin.js?ver=HTML / DOM Fingerprints
woocommerce_options_panelfor="file_field"id="wua_file_addon"accept="image/*"<input type="file" name='wua_file_addon' id="wua_file_addon" accept='image/*'>