TextToMe Security & Risk Analysis
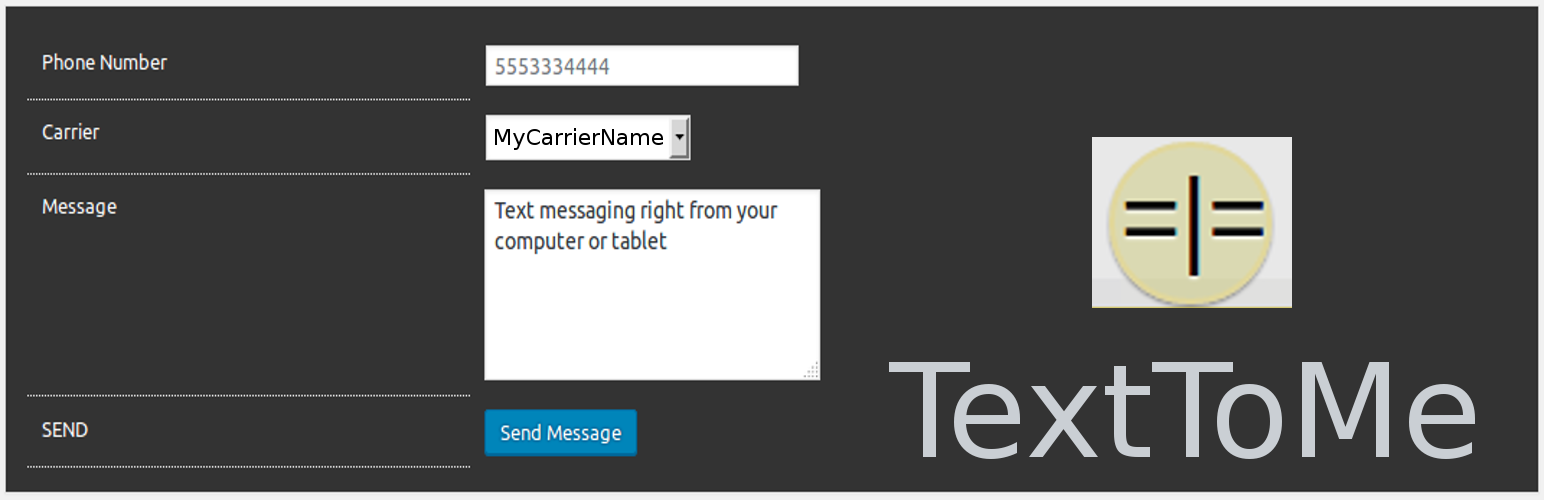
wordpress.org/plugins/texttomeText Messaging to a phone from your WordPress Admin panel.
Is TextToMe Safe to Use in 2026?
Generally Safe
Score 100/100TextToMe has no known CVEs and is actively maintained. It's a solid choice for most WordPress installations.
The texttome v0.2.0 plugin exhibits a seemingly strong security posture based on the provided static analysis. There are no identified entry points with unprotected access, no dangerous function calls, and all SQL queries utilize prepared statements. Furthermore, the plugin has no recorded vulnerability history, suggesting a clean track record.
However, a critical concern arises from the output escaping. With two total outputs and 0% properly escaped, this indicates a high risk of Cross-Site Scripting (XSS) vulnerabilities. Any user-supplied data that is displayed by the plugin without proper sanitization could be exploited to inject malicious scripts. The absence of capability checks and nonce checks, while not directly indicated as exploited in this version, are missed opportunities for robust security, especially if the attack surface were to expand.
In conclusion, while the plugin avoids common pitfalls like raw SQL and excessive attack vectors, the complete lack of output escaping is a significant and immediate security risk. This weakness, coupled with the absence of essential security checks, significantly overshadows the otherwise clean analysis and vulnerability history. Users should exercise extreme caution when employing this plugin.
Key Concerns
- Output escaping is completely missing
- No capability checks found
- No nonce checks found
TextToMe Security Vulnerabilities
TextToMe Release Timeline
TextToMe Code Analysis
Output Escaping
TextToMe Attack Surface
WordPress Hooks 3
Maintenance & Trust
TextToMe Maintenance & Trust
Maintenance Signals
Community Trust
TextToMe Alternatives
TextMe SMS
textme-sms-integration
Send custom SMS messages from your WordPress site to your customers using the TextMe SMS gateway.
SMS Abandoned Cart Recovery ✦ CartBoss
cartboss
Boost your sales by recovering abandoned carts with pre-prepared & translated text messages!
SMS Contact Form 7 Notifications by ClickSend
clicksend-contactform7
Reliable and global SMS notifications for Contact Form 7. ClickSend brings instant SMS communication to the mix. By integrating these tools, you eleva …
text message sms plugin
text-message
text message by biz text lets your website receive and send text messages. reply to text messages from a pc or forward messages to your mobile phone.
Text Message Contact Form
text-message-contact-form-biztext
Receive a Text or email, from your website through the Text Message Contact Form by Biz Text. SMS notification of email received, no third-party apps …
TextToMe Developer Profile
19 plugins · 2K total installs
How We Detect TextToMe
Patterns used to identify this plugin on WordPress sites during automated security audits and web crawling.
Asset Fingerprints
/wp-content/plugins/texttome/css/texttome.css/wp-content/plugins/texttome/js/texttome.js/wp-content/plugins/texttome/js/texttome.jstexttome/css/texttome.css?ver=texttome/js/texttome.js?ver=