SwiftRules – Conditional Discounts for WooCommerce Security & Risk Analysis
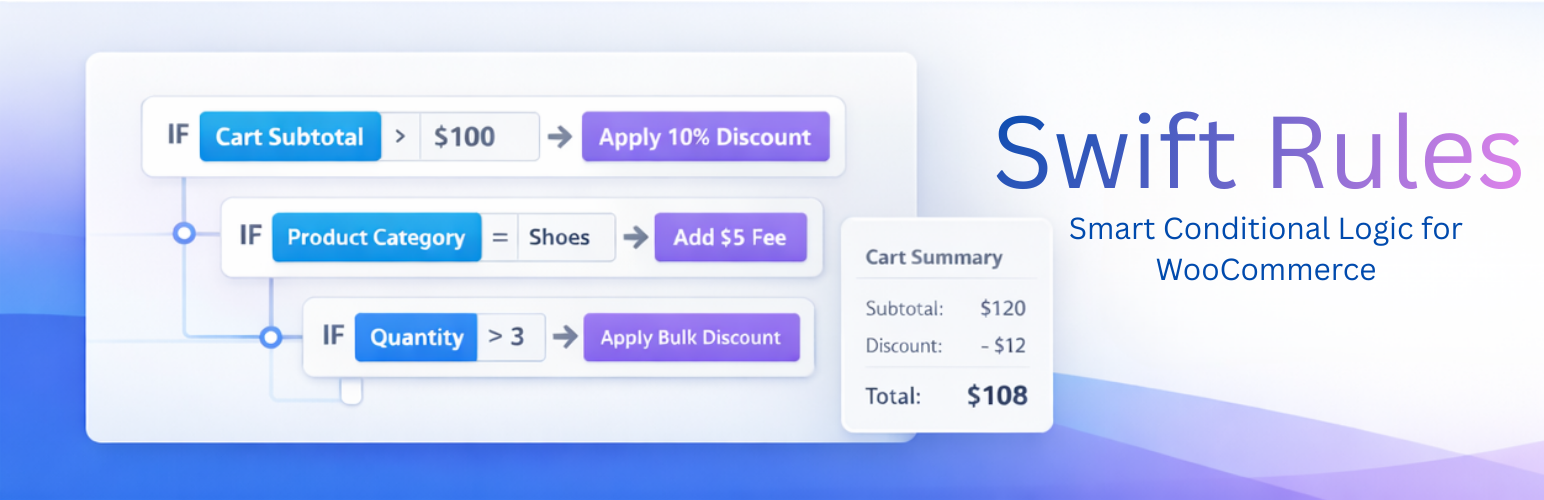
wordpress.org/plugins/swiftrules-conditional-discounts-for-woocommerceCreate conditional discounts, fees, and cart rules for WooCommerce using a flexible rule engine.
Is SwiftRules – Conditional Discounts for WooCommerce Safe to Use in 2026?
Generally Safe
Score 100/100SwiftRules – Conditional Discounts for WooCommerce has no known CVEs and is actively maintained. It's a solid choice for most WordPress installations.
The plugin 'swiftrules-conditional-discounts-for-woocommerce' v1.0.1 exhibits a generally good security posture based on the provided static analysis. The absence of known CVEs and a clean vulnerability history are significant strengths, suggesting a commitment to security or at least a lack of discovered exploitable flaws. The code also demonstrates good practices with a high percentage of SQL queries using prepared statements and a majority of output being properly escaped. The presence of nonce and capability checks further enhances its security.
However, a potential area of concern is a single flow identified with an unsanitized path in the taint analysis. While the severity is not explicitly stated as critical or high, this indicates a possible vector for directory traversal or similar file-related attacks. Furthermore, the presence of file operations, even if only one, warrants careful review to ensure it is handled securely. The use of bundled libraries like Select2, while common, can introduce risks if not kept up-to-date or if vulnerabilities are discovered within them, though no such issues are reported here.
In conclusion, the plugin appears to be relatively secure, with its strongest points being its clean vulnerability record and robust use of prepared statements and output escaping. The single taint flow with an unsanitized path is the primary area requiring attention and further investigation to confirm its impact and mitigate any potential risks.
Key Concerns
- Flow with unsanitized path
- File operations present
SwiftRules – Conditional Discounts for WooCommerce Security Vulnerabilities
SwiftRules – Conditional Discounts for WooCommerce Release Timeline
SwiftRules – Conditional Discounts for WooCommerce Code Analysis
Bundled Libraries
SQL Query Safety
Output Escaping
Data Flow Analysis
SwiftRules – Conditional Discounts for WooCommerce Attack Surface
WordPress Hooks 13
Maintenance & Trust
SwiftRules – Conditional Discounts for WooCommerce Maintenance & Trust
Maintenance Signals
Community Trust
SwiftRules – Conditional Discounts for WooCommerce Alternatives
Conditional Discounts for WooCommerce
conditional-discounts-for-woocommerce
Boost sales with rule-based WooCommerce discounts. Offer targeted deals based on cart totals, products, and user roles.
Discount Rules for WooCommerce
woo-discount-rules
The discount plugin for WooCommerce helps you create bulk discount, quantity discount, storewide sale, dynamic pricing discount offers easily.
Advanced Dynamic Pricing and Discount Rules for WooCommerce
advanced-dynamic-pricing-for-woocommerce
The discount plugin for WooCommerce supports any dynamic pricing discount: bulk discount, role discount, storewide, bogo, gifts, cart discount
Dynamic Pricing With Discount Rules for WooCommerce
aco-woo-dynamic-pricing
The Dynamic Pricing With Discount Rules plugin enables bulk discounts for WooCommerce products. Its simple design allows easy setup in minutes.
ELEX WooCommerce Product Price Custom Text (Before & After Text) and Discount
elex-product-price-custom-text-before-after-text-and-discount-for-woocommerce
Add a text before and after the product price both globally and individually. Also, apply a quick discount for your products.
SwiftRules – Conditional Discounts for WooCommerce Developer Profile
2 plugins · 0 total installs
How We Detect SwiftRules – Conditional Discounts for WooCommerce
Patterns used to identify this plugin on WordPress sites during automated security audits and web crawling.
Asset Fingerprints
/wp-content/plugins/swiftrules-conditional-discounts-for-woocommerce/assets/css/select2-bundle.css/wp-content/plugins/swiftrules-conditional-discounts-for-woocommerce/assets/js/admin.js/wp-content/plugins/swiftrules-conditional-discounts-for-woocommerce/assets/css/admin.css/wp-content/plugins/swiftrules-conditional-discounts-for-woocommerce/assets/js/admin.jsswiftrules-conditional-discounts-for-woocommerce/assets/css/select2-bundle.css?ver=swiftrules-conditional-discounts-for-woocommerce/assets/js/admin.js?ver=swiftrules-conditional-discounts-for-woocommerce/assets/css/admin.css?ver=HTML / DOM Fingerprints
swiftrules-admindata-swiftrules-nonceswiftrules