StickyBoard Security & Risk Analysis
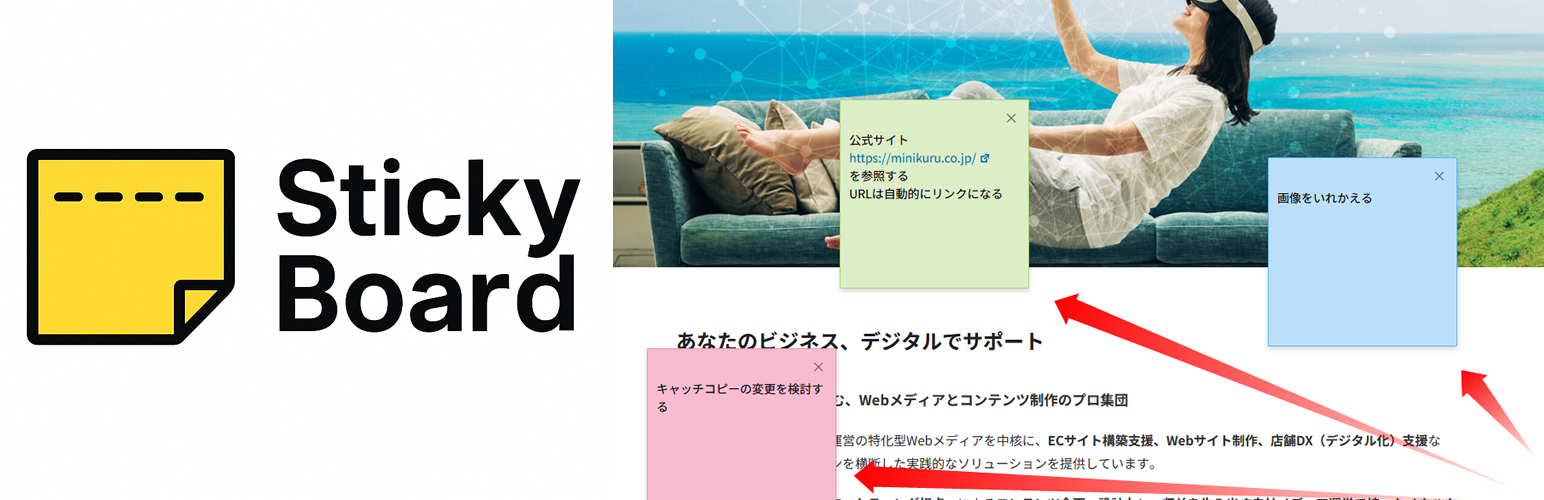
wordpress.org/plugins/stickyboardログインユーザーがWebページに付箋を追加できるようにするプラグイン。Create personal sticky notes on any WordPress page.
Is StickyBoard Safe to Use in 2026?
Generally Safe
Score 92/100StickyBoard has no known CVEs and is actively maintained. It's a solid choice for most WordPress installations.
The stickyboard plugin v1.1.0 exhibits a generally strong security posture based on the static analysis. The absence of dangerous functions, file operations, and external HTTP requests is a positive sign. Furthermore, the high percentage of SQL queries using prepared statements and properly escaped output suggests good development practices regarding data handling and preventing cross-site scripting (XSS) vulnerabilities. The limited attack surface, with all entry points having permission checks, is also commendable. The plugin also has no recorded vulnerability history, which further reinforces its perceived security.
However, a notable concern is the complete lack of capability checks in conjunction with REST API routes. While these routes do have permission callbacks, the absence of specific capability checks means that access control might be broader than intended, potentially allowing users with less privileged roles to perform actions they shouldn't. The limited number of nonce checks (only 2) also raises a slight concern for potential Cross-Site Request Forgery (CSRF) vulnerabilities, although without specific flows identified, this remains a theoretical risk. The absence of any recorded historical vulnerabilities is a strength, indicating consistent secure development, but it doesn't negate the need to scrutinize the current code for potential weaknesses.
In conclusion, stickyboard v1.1.0 appears to be a securely developed plugin with robust data handling. The primary areas for potential improvement lie in refining access control for its REST API endpoints by incorporating specific capability checks and potentially increasing the number of nonce checks to mitigate CSRF risks more thoroughly. The lack of historical vulnerabilities is a significant positive, but the current analysis reveals areas where security could be further hardened.
Key Concerns
- REST API routes lack capability checks
- Low number of nonce checks
StickyBoard Security Vulnerabilities
StickyBoard Release Timeline
StickyBoard Code Analysis
SQL Query Safety
Output Escaping
Data Flow Analysis
StickyBoard Attack Surface
REST API Routes 4
WordPress Hooks 6
Maintenance & Trust
StickyBoard Maintenance & Trust
Maintenance Signals
Community Trust
StickyBoard Alternatives
Plugin Notes Plus
plugin-notes-plus
Adds a column to the Plugins page where you can add, edit, or delete notes about a plugin.
Dashboard Sticky Notes
dashboard-sticky-notes
This plugin adds the functionality to add sticky notes into the dashboard.
Page & Post Notes
page-post-notes
Simple plugin that allow you to notes on pages and posts
Sticky Notes for WP Dashboard
wb-sticky-notes
Create sticky notes in your WP admin for reminders and to-dos. Restrict notes by user roles and disable them on specific pages.
Notely
notely
Create admin text notes for any post, page or custom post type.
StickyBoard Developer Profile
3 plugins · 80 total installs
How We Detect StickyBoard
Patterns used to identify this plugin on WordPress sites during automated security audits and web crawling.
Asset Fingerprints
/wp-content/plugins/stickyboard/assets/css/stickyboard.css/wp-content/plugins/stickyboard/assets/js/stickyboard.js/wp-content/plugins/stickyboard/assets/js/stickyboard.jsstickyboard.css?ver=stickyboard.js?ver=HTML / DOM Fingerprints
stickyBoard/stickyboard/v1