Sravnitel Security & Risk Analysis
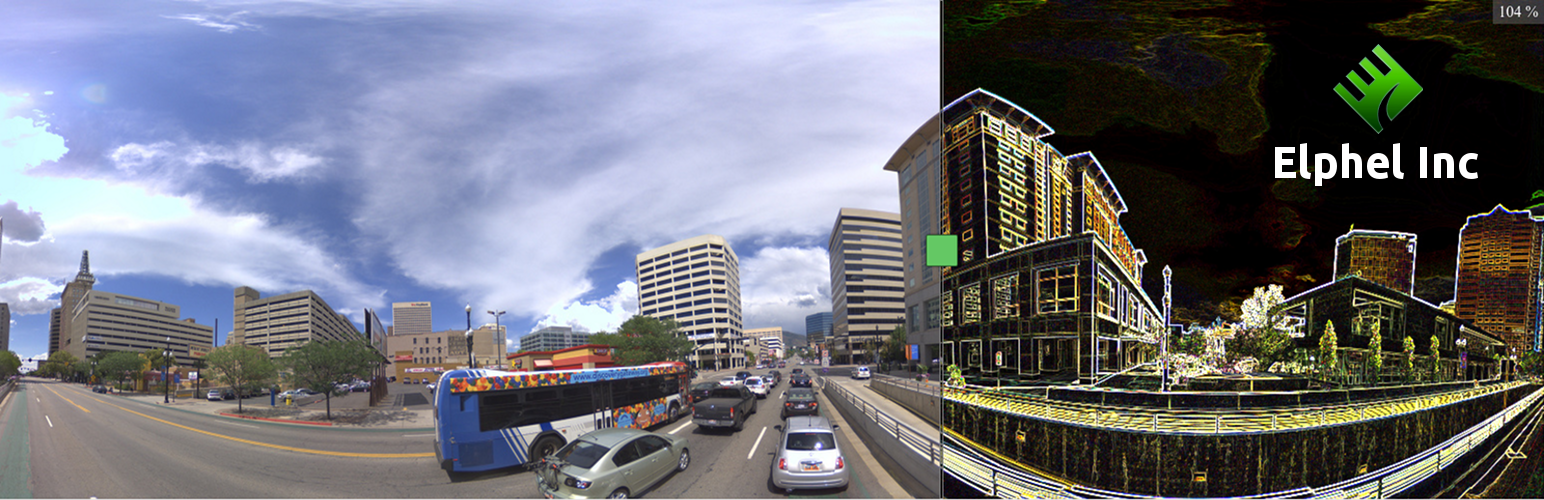
wordpress.org/plugins/sravnitelSravnitel is a WordPress plugin by Elphel Inc. based on a jQuery plugin jquery.sravnitel.js.
Is Sravnitel Safe to Use in 2026?
Generally Safe
Score 85/100Sravnitel has no known CVEs and is actively maintained. It's a solid choice for most WordPress installations.
The 'sravnitel' v1.3 plugin exhibits a strong security posture based on the provided static analysis. The absence of dangerous functions, the exclusive use of prepared statements for SQL queries, and proper output escaping all indicate good development practices aimed at preventing common web vulnerabilities. Furthermore, the lack of external HTTP requests and file operations limits the potential for remote code execution or sensitive data exfiltration.
The plugin's attack surface is minimal, with only one shortcode and no unprotected AJAX handlers or REST API routes. The taint analysis revealing zero flows with unsanitized paths is also a very positive sign, suggesting that user-supplied data is being handled securely. The plugin's vulnerability history is clean, with no recorded CVEs, which further bolsters confidence in its current security state.
However, the complete absence of nonce checks and capability checks across all entry points (even though the attack surface is small and unprotected entry points are zero) represents a potential area for improvement. While the current structure may not immediately lead to vulnerabilities due to the limited attack surface, implementing these standard WordPress security measures would further harden the plugin against potential future threats or when integrated into more complex environments. Overall, 'sravnitel' v1.3 appears to be a securely coded plugin, with its primary weakness being the lack of standard authentication and authorization checks on its sole entry point.
Key Concerns
- Missing nonce checks on shortcode
- Missing capability checks on shortcode
Sravnitel Security Vulnerabilities
Sravnitel Release Timeline
Sravnitel Code Analysis
Output Escaping
Sravnitel Attack Surface
Shortcodes 1
WordPress Hooks 2
Maintenance & Trust
Sravnitel Maintenance & Trust
Maintenance Signals
Community Trust
Sravnitel Alternatives
Default Image Link
default-image-link
Select default settings for image link when you upload or insert images. Select default image link to None, Attachment Page, Media File or Custom URL.
Duplicate Page
duplicate-page
Duplicate Posts, Pages and Custom Posts easily using single click
Autoptimize
autoptimize
Autoptimize speeds up your website by optimizing JS, CSS, images (incl. lazy-load), HTML and Google Fonts, asyncing JS, removing emoji cruft and more.
Duplicate Post
copy-delete-posts
Duplicate post
Smash Balloon Social Post Feed – Simple Social Feeds for WordPress
custom-facebook-feed
Formerly "Custom Facebook Feed". Display completely customizable Facebook feeds of a Facebook page. Supports Facebook oEmbeds.
Sravnitel Developer Profile
1 plugin · 10 total installs
How We Detect Sravnitel
Patterns used to identify this plugin on WordPress sites during automated security audits and web crawling.
Asset Fingerprints
/wp-content/plugins/sravnitel/assets/css/sravnitel.css/wp-content/plugins/sravnitel/assets/js/jquery.sravnitel.js/wp-content/plugins/sravnitel/assets/js/jquery.sravnitel.jssravnitel-stylesravnitelHTML / DOM Fingerprints
sravniteljQuery<div id="sravnitel_" style="position:relative;" class="sravnitel"></div><script>
jQuery(window).load(function(){
jQuery("#sravnitel_").sravnitel({