Smart Syntax Security & Risk Analysis
wordpress.org/plugins/smart-syntaxAutomatic google prettify syntax highlighting for jetpack markdown fenced code blocks
Is Smart Syntax Safe to Use in 2026?
Generally Safe
Score 85/100Smart Syntax has no known CVEs and is actively maintained. It's a solid choice for most WordPress installations.
The 'smart-syntax' plugin v1.0.2 exhibits a generally strong security posture based on the provided static analysis. The absence of any recorded vulnerabilities in its history, coupled with the complete lack of detected SQL injection vulnerabilities and the use of prepared statements for all queries, is a significant strength. Furthermore, the plugin demonstrates good practices by employing nonce checks and having no external HTTP requests, which limits potential attack vectors. However, the presence of the `unserialize` function is a notable concern. While the static analysis didn't flag any specific taint flows stemming from it, `unserialize` is inherently risky if not handled with extreme caution, as it can lead to Remote Code Execution (RCE) if processing untrusted input. The relatively low percentage of properly escaped output also presents a minor risk of Cross-Site Scripting (XSS) vulnerabilities, although the attack surface appears to be minimal. The lack of capability checks on any identified entry points is also a weakness, though this is mitigated by the reported zero entry points. Overall, the plugin appears to be developed with security in mind, but the `unserialize` function warrants careful review and monitoring.
Key Concerns
- Presence of unserialize function
- Low output escaping percentage
- Missing capability checks on entry points
Smart Syntax Security Vulnerabilities
Smart Syntax Release Timeline
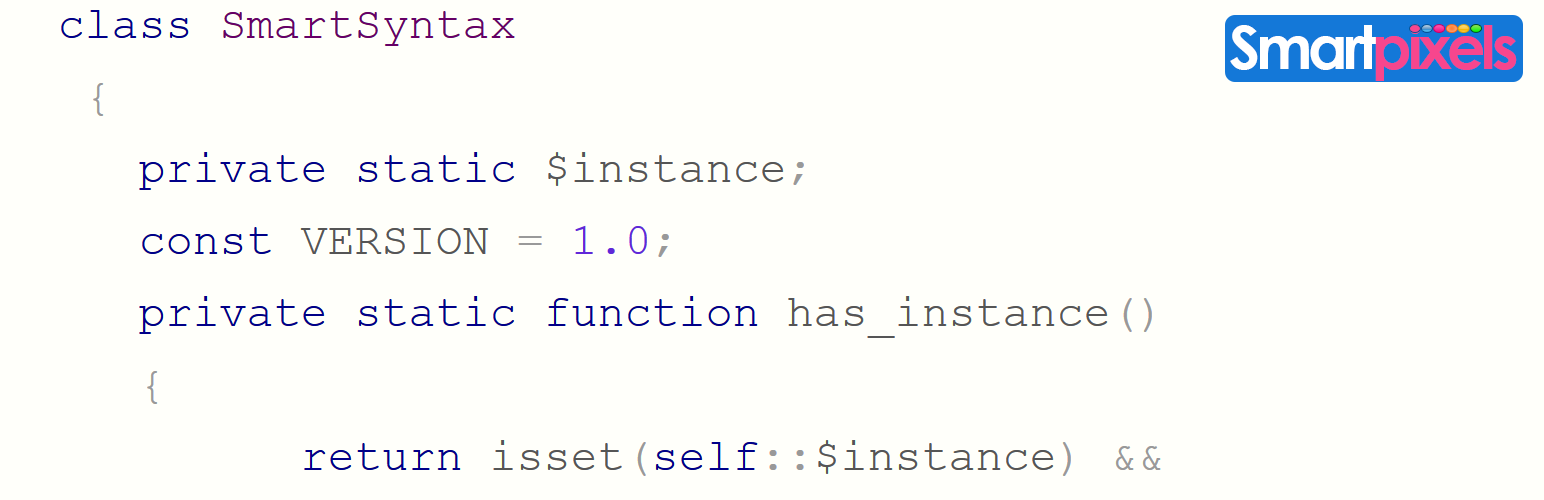
Smart Syntax Code Analysis
Dangerous Functions Found
Output Escaping
Data Flow Analysis
Smart Syntax Attack Surface
WordPress Hooks 5
Maintenance & Trust
Smart Syntax Maintenance & Trust
Maintenance Signals
Community Trust
Smart Syntax Alternatives
WP-Markdown
wp-markdown
Allows Markdown to be enabled in posts, comments and bbPress forums.
Markdown Highlighter
markdown-highlighter
A plugin to parse the markdown content from post then highlight it as syntax highlight.
Vaaky Highlighter – Syntax Highlighter for Gutenberg
vaaky-highlighter
Lightweight syntax highlighter plugin for WordPress Gutenberg powered by Highlight.js. Add beautiful, fast, and responsive code blocks with ease.
HTML Editor Syntax Highlighter
html-editor-syntax-highlighter
Add syntax highlighting to WordPress code editors using CodeMirror.js
Enlighter – Customizable Syntax Highlighter
enlighter
All-in-one Syntax Highlighting solution. Full Gutenberg and Classic Editor integration. Graphical theme customizer. Based on EnlighterJS.
Smart Syntax Developer Profile
2 plugins · 20 total installs
How We Detect Smart Syntax
Patterns used to identify this plugin on WordPress sites during automated security audits and web crawling.
Asset Fingerprints
/wp-content/plugins/smart-syntax/assets/css/smart_syntax.css/wp-content/plugins/smart-syntax/assets/css/prettify.css/wp-content/plugins/smart-syntax/assets/js/src/run_prettify.jssmart-syntax/style.css?ver=smart-syntax/script.js?ver=HTML / DOM Fingerprints
prettyprintlang-prettyPrint()