Reset Complete Site Security & Risk Analysis
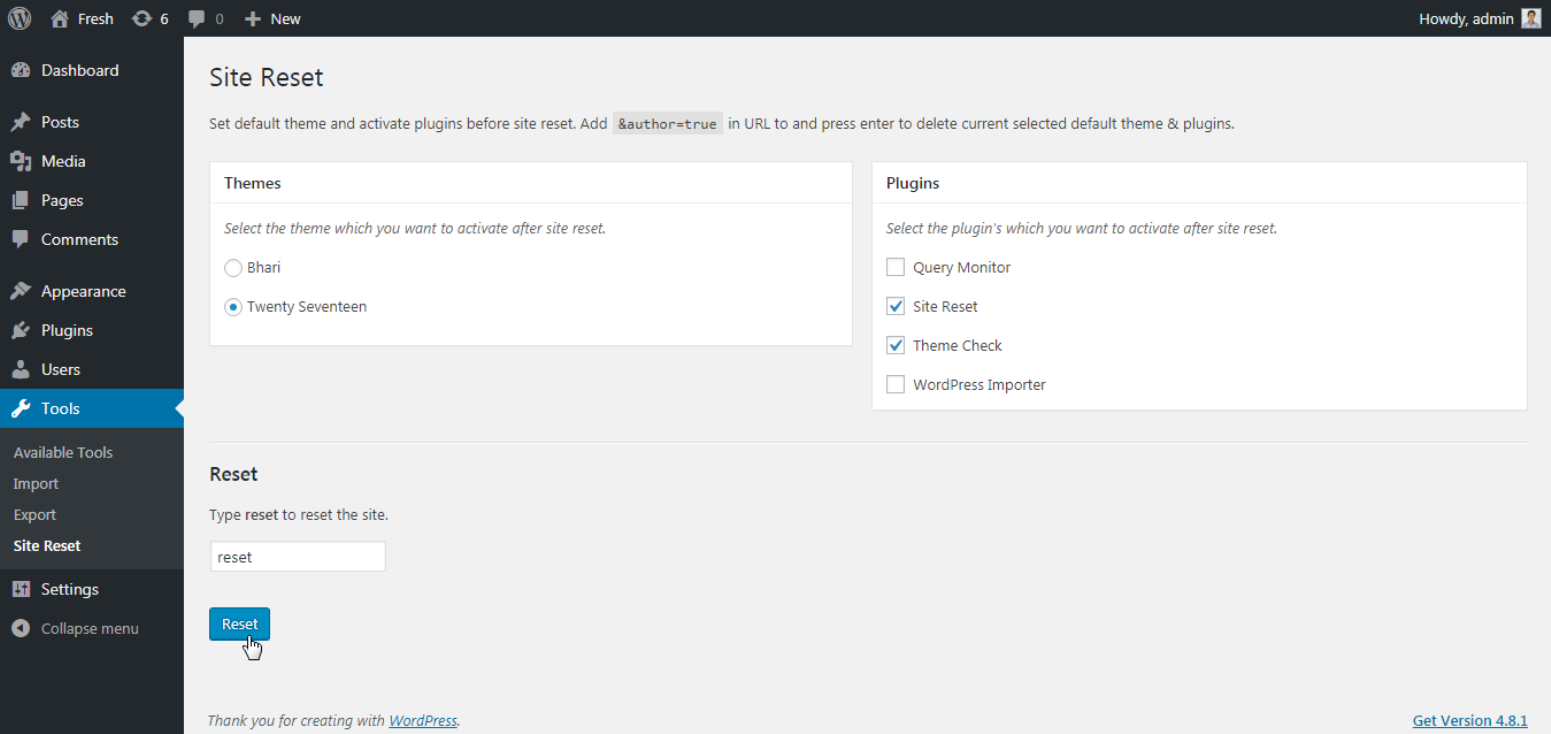
wordpress.org/plugins/site-resetSelect your favorite theme and active plugin's which you want to see after site reset.
Is Reset Complete Site Safe to Use in 2026?
Generally Safe
Score 85/100Reset Complete Site has no known CVEs and is actively maintained. It's a solid choice for most WordPress installations.
The "site-reset" plugin, v1.2.1, exhibits a strong security posture based on the provided static analysis. The complete absence of AJAX handlers, REST API routes, shortcodes, and cron events significantly limits the attack surface, and all identified entry points are secured with authentication checks. The code demonstrates good security practices with 100% output escaping, a single nonce check, and a single capability check, indicating developers are mindful of common web vulnerabilities. The lack of dangerous functions, file operations, and external HTTP requests further enhances its security profile. The vulnerability history is also clean, with no recorded CVEs, which is a very positive sign, suggesting a history of secure development and maintenance. The plugin appears to be well-protected against common attack vectors.
While the static analysis shows no critical or high severity taint flows and a reasonable percentage of SQL queries using prepared statements, it's worth noting that 50% of SQL queries are not prepared. While not a critical finding with the current data, this represents a potential area for improvement to further strengthen the plugin against SQL injection, especially as the plugin grows or if new database interactions are added. The limited scope of SQL queries (4 total) and the presence of some prepared statements mitigate this risk for now. Overall, "site-reset" v1.2.1 presents as a secure plugin with a minimal attack surface and good coding practices, with the only notable area for potential improvement being the 50% of SQL queries not using prepared statements.
Key Concerns
- 50% of SQL queries not using prepared statements
Reset Complete Site Security Vulnerabilities
Reset Complete Site Release Timeline
Reset Complete Site Code Analysis
SQL Query Safety
Output Escaping
Reset Complete Site Attack Surface
WordPress Hooks 5
Maintenance & Trust
Reset Complete Site Maintenance & Trust
Maintenance Signals
Community Trust
Reset Complete Site Alternatives
Reset Complete Site Developer Profile
9 plugins · 270 total installs
How We Detect Reset Complete Site
Patterns used to identify this plugin on WordPress sites during automated security audits and web crawling.
Asset Fingerprints
/wp-content/plugins/site-reset/assets/admin.js/wp-content/plugins/site-reset/assets/admin.jssite-reset-admin?ver=HTML / DOM Fingerprints
aria-label="Settings"aria-label="Reset Complete Site"siteReset