Refiner Microsurveys Plugin Security & Risk Analysis
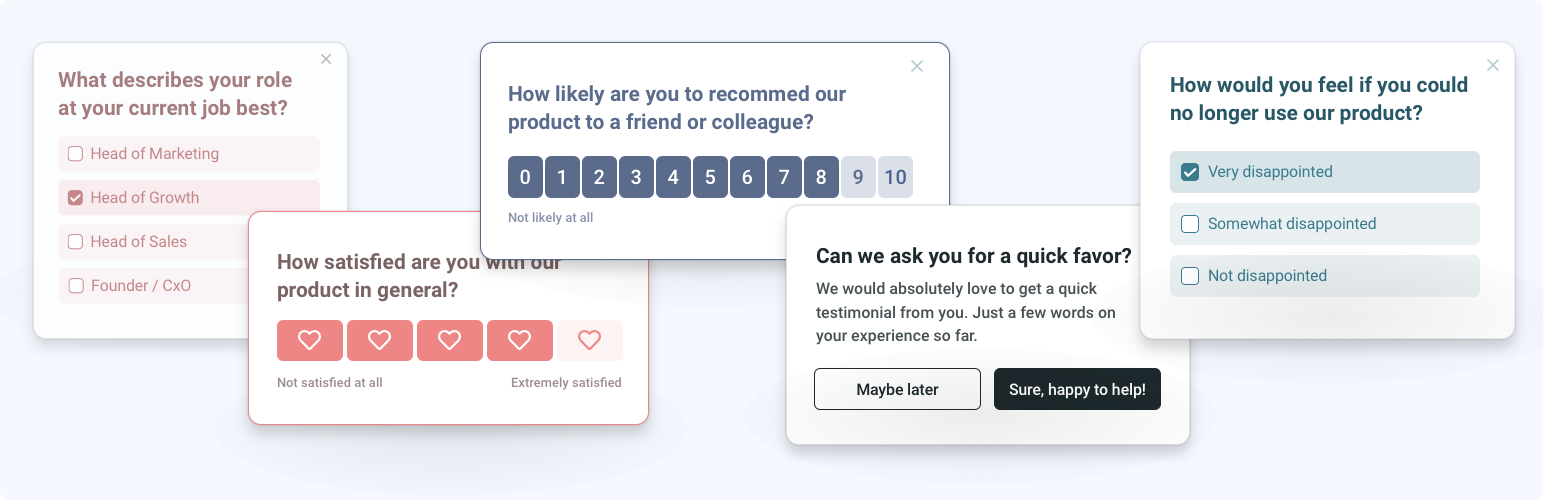
wordpress.org/plugins/refinerInstall Refiner on your WordPress site and launch microsurveys within your website or web applicaiton.
Is Refiner Microsurveys Plugin Safe to Use in 2026?
Generally Safe
Score 92/100Refiner Microsurveys Plugin has no known CVEs and is actively maintained. It's a solid choice for most WordPress installations.
Based on the static analysis and vulnerability history, the 'refiner' plugin v1.0.0 appears to have a strong initial security posture. There are no identified entry points (AJAX, REST API, shortcodes, cron events), no dangerous functions used, and all SQL queries leverage prepared statements. The absence of file operations, external HTTP requests, and bundled libraries further reduces the potential attack surface. The vulnerability history is also clean, with no known CVEs, suggesting a history of secure development or a lack of past scrutiny.
However, there are notable concerns. The lack of any nonce checks or capability checks, combined with 40% of output not being properly escaped, presents a significant risk. While the static analysis found no direct flows of unsanitized data, the absence of these fundamental security mechanisms means that if any input were to be processed and outputted without proper sanitization or authorization in the future, it could lead to vulnerabilities. The current lack of identified vulnerabilities might be due to the plugin's limited functionality or attack surface, rather than a proven history of robust security implementation across all potential scenarios.
In conclusion, the 'refiner' plugin v1.0.0 exhibits strengths in its minimal attack surface and secure database interaction. However, the critical weaknesses lie in the complete absence of nonce and capability checks and a significant amount of unescaped output. These omissions, despite the current clean slate, represent a substantial security debt and a high potential for exploitation if the plugin's functionality evolves or if new, previously undiscovered, interaction points are introduced.
Key Concerns
- Missing nonce checks on all entry points
- Missing capability checks on all entry points
- Significant amount of unescaped output (40%)
Refiner Microsurveys Plugin Security Vulnerabilities
Refiner Microsurveys Plugin Release Timeline
Refiner Microsurveys Plugin Code Analysis
Output Escaping
Refiner Microsurveys Plugin Attack Surface
WordPress Hooks 5
Maintenance & Trust
Refiner Microsurveys Plugin Maintenance & Trust
Maintenance Signals
Community Trust
Refiner Microsurveys Plugin Alternatives
NativeForms – Contact, NPS, Payment, Feedback, Newsletter Forms
nativeforms
Build forms, surveys & polls for WordPress. Add forms to your website in few minutes and start getting more from your visitors.
Grappin.io Micro Surveys Widget
grappin
Install Grappin on your WordPress site and launch surveys
Crowdsignal Forms
crowdsignal-forms
The Crowdsignal Forms plugin allows you to create and manage polls right from within the block editor.
UserFeedback – Create Interactive Feedback Form, User Surveys, and Polls in Seconds
userfeedback-lite
Ultimate user feedback plugin to ask questions, surveys, polls, from your website in seconds
Crowdsignal Dashboard – Polls, Surveys & more
polldaddy
Manage your Crowdsignal polls, surveys, quizzes, and ratings directly from the WordPress dashboard.
Refiner Microsurveys Plugin Developer Profile
1 plugin · 10 total installs
How We Detect Refiner Microsurveys Plugin
Patterns used to identify this plugin on WordPress sites during automated security audits and web crawling.
Asset Fingerprints
/wp-content/plugins/refiner/admin/assets/main.csshttps://js.refiner.io/v001/client.jsHTML / DOM Fingerprints
window._refinerQueuewindow._refiner