Checking Variables (Dev. Tool) Security & Risk Analysis
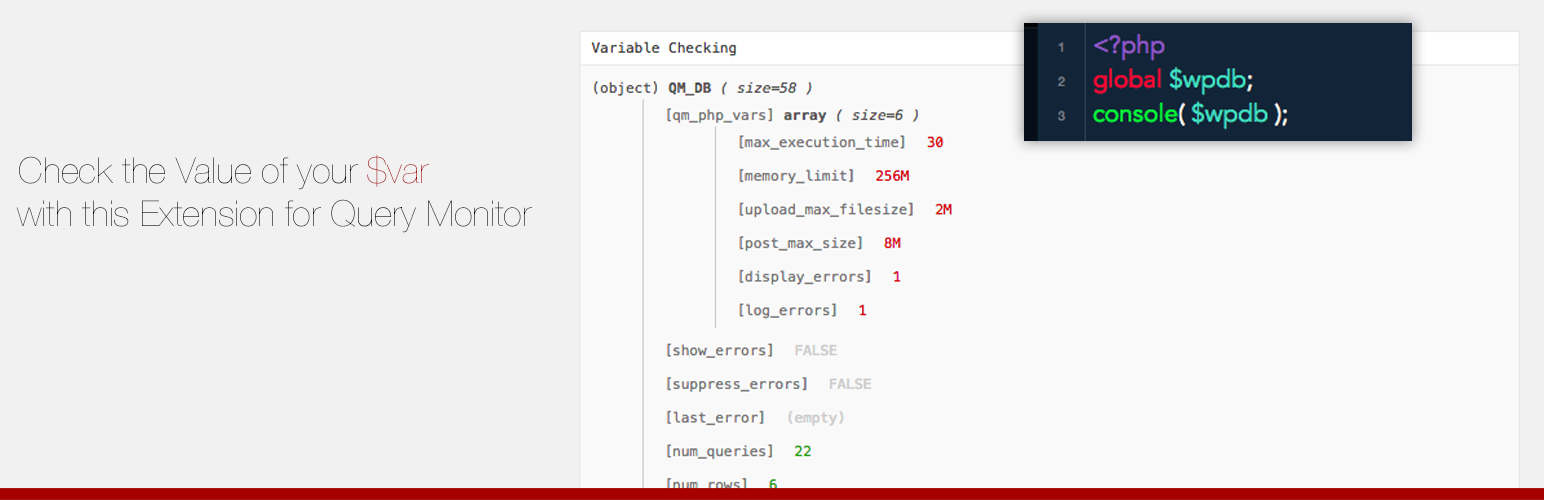
wordpress.org/plugins/query-monitor-extension-checking-variablesDevelopers! Check your variables.
Is Checking Variables (Dev. Tool) Safe to Use in 2026?
Generally Safe
Score 85/100Checking Variables (Dev. Tool) has no known CVEs and is actively maintained. It's a solid choice for most WordPress installations.
The "query-monitor-extension-checking-variables" plugin v4.0.0 demonstrates a generally strong security posture based on the provided static analysis. The complete absence of direct entry points like AJAX handlers, REST API routes, shortcodes, and cron events significantly limits the potential attack surface. Furthermore, the code shows excellent practice by using prepared statements for all SQL queries and not performing any file operations or external HTTP requests, which are common sources of vulnerabilities.
However, a notable concern is the low percentage (20%) of properly escaped output. With 49 total outputs, this indicates that a significant number of them might be vulnerable to Cross-Site Scripting (XSS) attacks if user-supplied data is involved. While there are no recorded vulnerabilities or taint flows indicating critical or high risks, the potential for XSS due to insufficient output escaping should not be overlooked. The presence of a nonce check is positive, but the absence of capability checks for any potential (though currently non-existent) entry points is a minor area for improvement in a comprehensive security model.
In conclusion, the plugin benefits from a minimal attack surface and responsible handling of database interactions. The primary weakness lies in the output escaping, which, if not addressed, could lead to medium or low severity vulnerabilities. The lack of past vulnerabilities is a positive sign, suggesting developers are attentive to security, but the current code analysis highlights an area requiring attention.
Key Concerns
- Low percentage of properly escaped output
Checking Variables (Dev. Tool) Security Vulnerabilities
Checking Variables (Dev. Tool) Release Timeline
Checking Variables (Dev. Tool) Code Analysis
Output Escaping
Checking Variables (Dev. Tool) Attack Surface
WordPress Hooks 13
Maintenance & Trust
Checking Variables (Dev. Tool) Maintenance & Trust
Maintenance Signals
Community Trust
Checking Variables (Dev. Tool) Alternatives
Query Monitor
query-monitor
Query Monitor is the developer tools panel for WordPress and WooCommerce.
DebugPress: Debugger in Popup
debugpress
Easy-to-use plugin for debugging and profiling website loading, SQL queries analysis, help with development, bug fixing, all in configurable popup.
Debug This
debug-this
Peek under the hood with sixty debugging reports just one click away.
Admin Bar Tools
sf-adminbar-tools
Adds some small development tools to the admin bar.
Variable Inspector
variable-inspector
Inspect PHP variables on a central dashboard in wp-admin for convenient debugging.
Checking Variables (Dev. Tool) Developer Profile
6 plugins · 130 total installs
How We Detect Checking Variables (Dev. Tool)
Patterns used to identify this plugin on WordPress sites during automated security audits and web crawling.
Asset Fingerprints
/wp-content/plugins/query-monitor-extension-checking-variables/assets/js/check-var.js/wp-content/plugins/query-monitor-extension-checking-variables/assets/css/check-var.css/wp-content/plugins/query-monitor-extension-checking-variables/assets/js/check-var.jsquery-monitor-extension-checking-variables/assets/js/check-var.js?ver=query-monitor-extension-checking-variables/assets/css/check-var.css?ver=HTML / DOM Fingerprints
QMCVar