Project World Impact Security & Risk Analysis
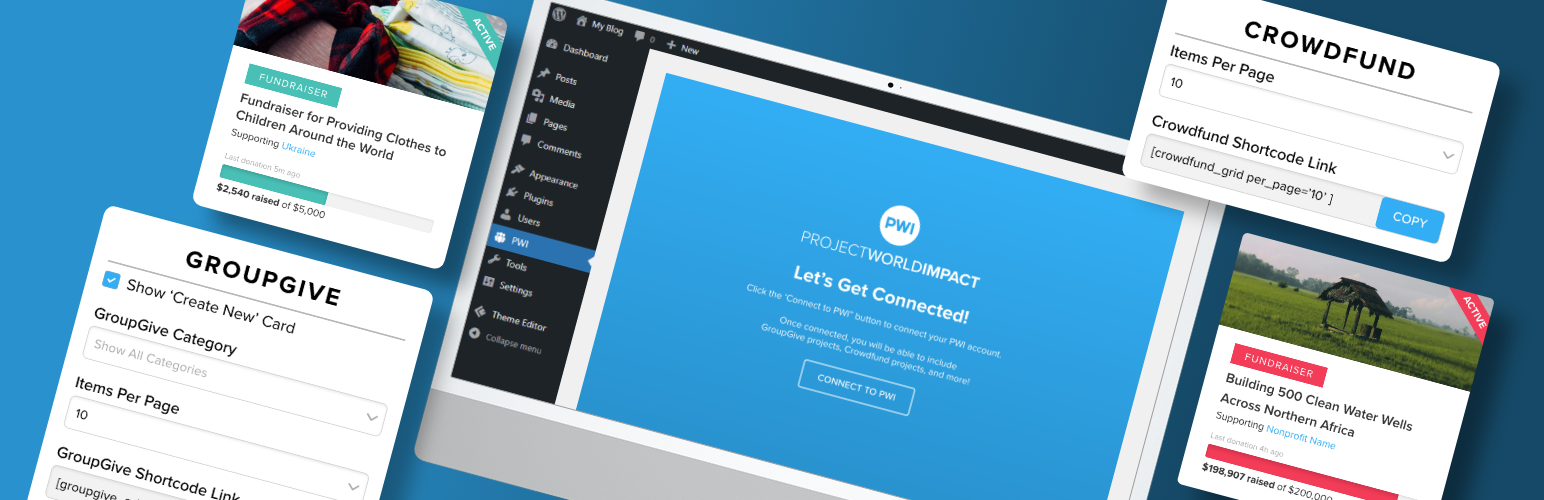
wordpress.org/plugins/project-world-impactIntegrate PWI Crowdfund, PWI GroupGive, and PWI Storyteller features into your WordPress site with our powerful plugin for nonprofit partners.
Is Project World Impact Safe to Use in 2026?
Generally Safe
Score 100/100Project World Impact has no known CVEs and is actively maintained. It's a solid choice for most WordPress installations.
The "project-world-impact" plugin v2.3 demonstrates a strong security posture based on the provided static analysis. The absence of shortcodes, cron events, and REST API routes significantly limits its attack surface. Crucially, all identified AJAX handlers are protected by authentication checks, and there are no unescaped outputs or dangerous functions detected. The code also shows good practices in using prepared statements for all SQL queries, robust nonce checks, and capability checks, along with zero taint flows of critical or high severity. The lack of any known vulnerabilities in its history further reinforces this positive assessment.
However, while the current analysis reveals no immediate critical flaws, a potential area for attention is the presence of three external HTTP requests. Without further context on the destination and purpose of these requests, they represent a minor vector for potential supply chain attacks or data exfiltration if the external services are compromised or malicious. The small number of entry points is a strength, but the plugin's reliance on external HTTP requests warrants a mention in the overall risk assessment. The plugin's current security profile is very good, with its strengths significantly outweighing any minor potential concerns.
In conclusion, "project-world-impact" v2.3 appears to be a securely developed plugin. Its adherence to common WordPress security best practices, such as input validation, output escaping, and proper authentication/authorization, is commendable. The absence of known vulnerabilities and the clean static analysis results suggest a low risk of exploitation. The only minor point to monitor would be the nature and trustworthiness of the external HTTP requests made by the plugin, but this is not a vulnerability in itself based on the data.
Key Concerns
- External HTTP requests (3)
Project World Impact Security Vulnerabilities
Project World Impact Release Timeline
Project World Impact Code Analysis
Output Escaping
Data Flow Analysis
Project World Impact Attack Surface
AJAX Handlers 2
WordPress Hooks 9
Maintenance & Trust
Project World Impact Maintenance & Trust
Maintenance Signals
Community Trust
Project World Impact Alternatives
GiveWP – Donation Plugin and Fundraising Platform
give
Accept donations and begin fundraising with GiveWP, the highest rated WordPress donation plugin for online giving.
Charitable – Donation Plugin for WordPress – Fundraising with Recurring Donations & More
charitable
The best WordPress donation plugin. Create fundraising donation forms, accept recurring donations, easy donor management, add crowdfunding, and more.
Leyka
leyka
Leyka is a plugin for crowdfunding and donations collection via WordPress website.
FundEngine – Donation and Crowdfunding Platform
wp-fundraising-donation
FundEngine - Fundraising Donation plugin and Crowdfunding Platform comes with Single donation and crowdfunding solution. You can use our plugin Either …
Crowded Collect — Dues & Fundraising
crowded-collect-dues-fundraising
Embed your Crowded collection directly into your WordPress site with no coding required!
Project World Impact Developer Profile
1 plugin · 0 total installs
How We Detect Project World Impact
Patterns used to identify this plugin on WordPress sites during automated security audits and web crawling.
Asset Fingerprints
/wp-content/plugins/project-world-impact/assets/css/admin.css/wp-content/plugins/project-world-impact/assets/js/admin.jsproject-world-impact/assets/css/admin.css?ver=project-world-impact/assets/js/admin.js?ver=HTML / DOM Fingerprints
mpwi_design_settings_sectionmpwi_design_main_grid_colormpwi_design_heading_font_sizempwi_design_heading_colormpwi_design_description_font_sizempwi_design_button_font_sizename="mpwi_design_settings[main_grid_color]"mpwi_ajax_object