Primal for WordPress Security & Risk Analysis
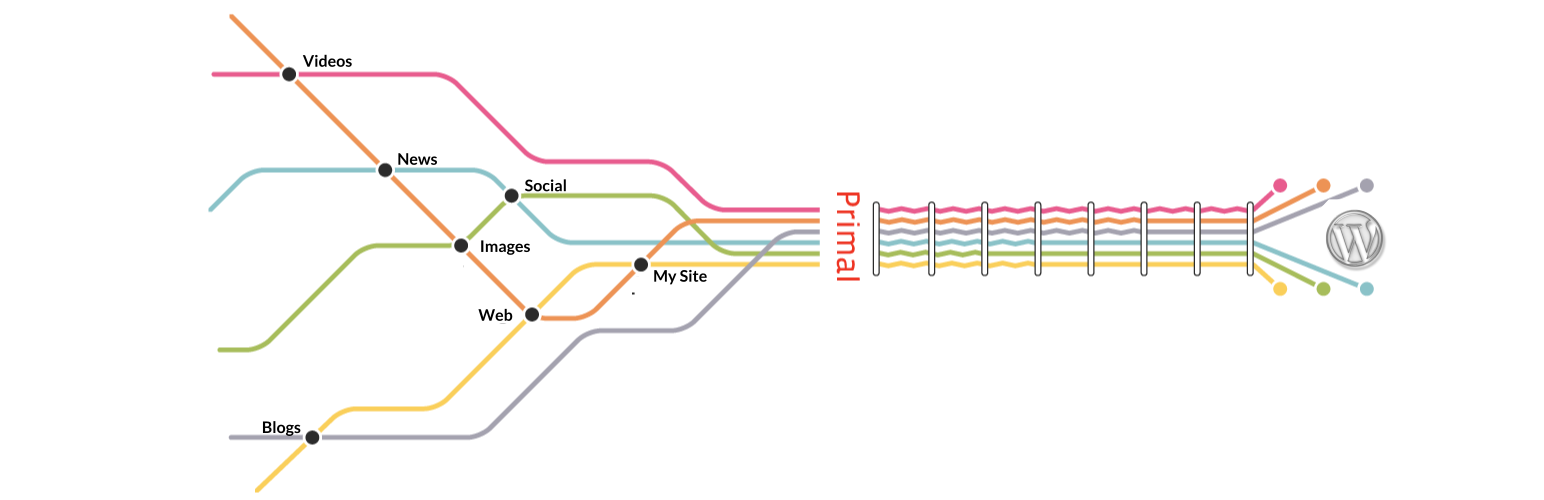
wordpress.org/plugins/primal-for-wpEngage your readers with great content that expresses your interests!
Is Primal for WordPress Safe to Use in 2026?
Generally Safe
Score 85/100Primal for WordPress has no known CVEs and is actively maintained. It's a solid choice for most WordPress installations.
The static analysis of Primal-for-WP v2.0.5 reveals a plugin with a remarkably small attack surface, as indicated by zero AJAX handlers, REST API routes, shortcodes, and cron events. This suggests a minimalistic design that inherently reduces potential entry points for attackers. Furthermore, the code signals show no dangerous functions, all SQL queries utilize prepared statements, and there are no file operations or external HTTP requests, which are all positive security indicators. However, a significant concern lies in the output escaping, where only 11% of outputs are properly escaped. This low percentage, despite a moderate number of output points, presents a substantial risk of Cross-Site Scripting (XSS) vulnerabilities. The absence of nonce and capability checks across all entry points (though there are zero entry points reported) is also a point of consideration; if any entry points were to be introduced or discovered, they would likely lack essential security checks. The plugin also has no recorded vulnerability history, which is positive, but this could also mean the plugin hasn't been extensively audited or is relatively new, making the existing code-level risks more critical. Overall, while the plugin demonstrates good practices in database interaction and attack surface minimization, the prevalent issue with output escaping requires immediate attention to mitigate XSS risks.
Key Concerns
- Low percentage of properly escaped output
- No capability checks on entry points
- No nonce checks on entry points
Primal for WordPress Security Vulnerabilities
Primal for WordPress Release Timeline
Primal for WordPress Code Analysis
Output Escaping
Primal for WordPress Attack Surface
WordPress Hooks 6
Maintenance & Trust
Primal for WordPress Maintenance & Trust
Maintenance Signals
Community Trust
Primal for WordPress Alternatives
EmbedPress – PDF Embedder, Embed YouTube Videos, 3D FlipBook, Social feeds, Docs & more
embedpress
EmbedPress lets you embed videos, pages, social feeds, embed PDF 3D flipbooks & other content on WordPress without coding & enhance storytelling.
Buttonizer – Social Media Share Buttons, Social Icons, & Social Feeds
facebook-pagelike-widget
Floating Social Media Icons, Sticky Share Buttons, Facebook Feeds, & Popup builder. Also, create Call, Email, SMS, & Contact buttons to increa …
WP Social Ninja – Embed Social Feeds, User Reviews & Chat Widgets
wp-social-reviews
Add Facebook feeds, Instagram feeds, TikTok feeds, Facebook reviews, WhatsApp Chat, Messenger chat, Testimonial, and others using a single dashboard.
Disable Feeds
disable-feeds
Disables all RSS/Atom/RDF feeds on your WordPress site.
GN Publisher: Google News Compatible RSS Feeds
gn-publisher
GN Publisher makes RSS feeds that comply with the Google News RSS Feed Technical Requirements for including your site in the Google News.
Primal for WordPress Developer Profile
1 plugin · 10 total installs
How We Detect Primal for WordPress
Patterns used to identify this plugin on WordPress sites during automated security audits and web crawling.
Asset Fingerprints
/wp-content/plugins/primal-for-wp/css/style.css/wp-content/plugins/primal-for-wp/js/resize.js/wp-content/plugins/primal-for-wp/js/resize.jsprimal_styleresize