Postaga Security & Risk Analysis
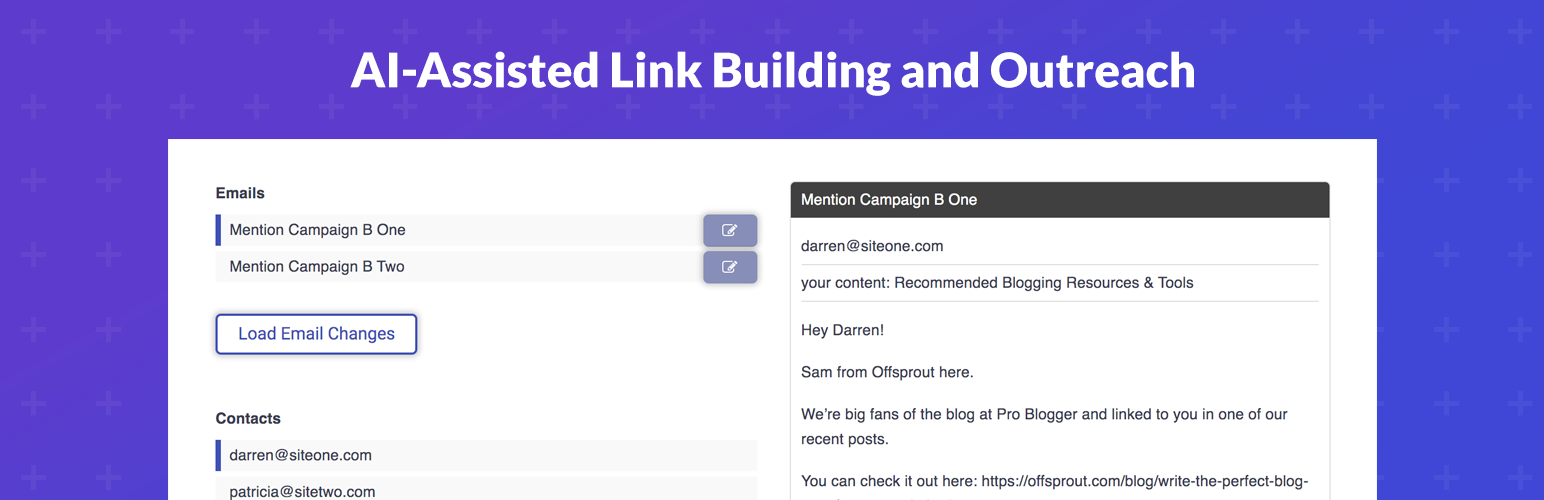
wordpress.org/plugins/postagaPostaga helps you automate your link building, content promotion, and outreach efforts with the power of AI.
Is Postaga Safe to Use in 2026?
Generally Safe
Score 85/100Postaga has no known CVEs and is actively maintained. It's a solid choice for most WordPress installations.
The 'postaga' plugin version 0.9 exhibits an excellent security posture based on the provided static analysis. The complete absence of any identified attack surface entry points like AJAX handlers, REST API routes, shortcodes, or cron events is a significant strength. Furthermore, the code demonstrates robust security practices, with zero dangerous functions, 100% prepared SQL statements, and 100% properly escaped output. The lack of file operations, external HTTP requests, and crucially, the absence of nonce and capability checks on all entry points (as there are none) further reinforces this strong foundation.
The taint analysis also indicates no identified vulnerabilities, with zero flows analyzed and consequently zero flows with unsanitized paths. The plugin's vulnerability history is also clean, with no recorded CVEs of any severity. This lack of historical issues and the clean static analysis suggest a well-developed and secure plugin. While the analysis is comprehensive, the extremely low attack surface and lack of specific security checks (like nonces and capabilities) are a direct consequence of there being no entry points to secure. This makes it difficult to assess the plugin's behavior when it *does* have interactions.
In conclusion, based solely on the provided data, 'postaga' v0.9 appears to be a highly secure plugin with no immediate exploitable vulnerabilities identified in its code or history. Its strengths lie in its minimal attack surface and adherence to secure coding practices for the limited code present. The primary "weakness" is the lack of discernible interaction points, which, while a positive for security in this context, limits the depth of security assessment.
Postaga Security Vulnerabilities
Postaga Release Timeline
Postaga Code Analysis
Postaga Attack Surface
WordPress Hooks 1
Maintenance & Trust
Postaga Maintenance & Trust
Maintenance Signals
Community Trust
Postaga Alternatives
Linkbuildr
linkbuildr
Automated content promotion. Share your content with the people who care the most, automatically.
Link Whisper Free
link-whisper
The AI-powered internal linking plugin for WordPress. Build internal links faster, find linking opportunities, and improve SEO automatically.
Internal Links Manager
seo-automated-link-building
Boost your SEO and get better rankings with our automated link building plugin. With this plugin you can link any keyword to any URL - internal or ext …
Interlinks Manager – Internal Links Optimizer
daext-interlinks-manager
Interlinks Manager is an SEO WordPress plugin that gives you the ability to monitor and optimize your internal links.
Autolinks Manager – SEO Auto Linker
daext-autolinks-manager
Automate your affiliate links, increase product page visits, link glossary keywords, and more with this advanced SEO auto-linker plugin.
Postaga Developer Profile
2 plugins · 10 total installs
How We Detect Postaga
Patterns used to identify this plugin on WordPress sites during automated security audits and web crawling.
Asset Fingerprints
/wp-content/plugins/postaga/js/postaga.js/wp-content/plugins/postaga/js/postaga.jsHTML / DOM Fingerprints
POSTAGA