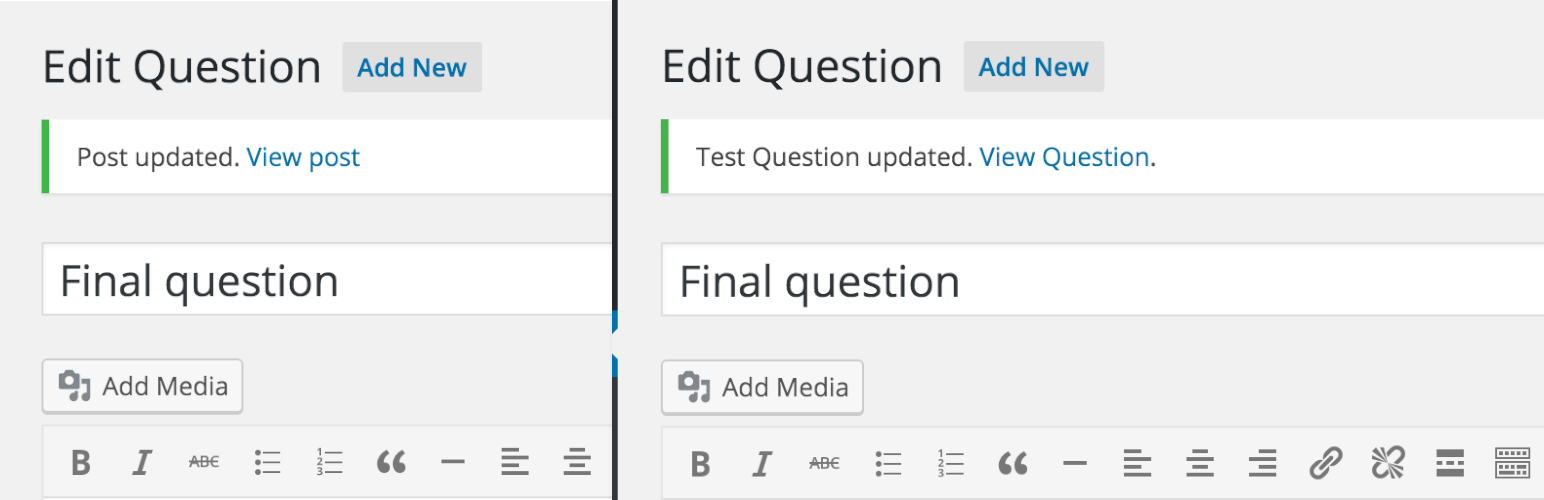
Post Updated Messages Security & Risk Analysis
wordpress.org/plugins/post-updated-messagesTailored updated messages for custom post types.
Is Post Updated Messages Safe to Use in 2026?
Generally Safe
Score 85/100Post Updated Messages has no known CVEs and is actively maintained. It's a solid choice for most WordPress installations.
The 'post-updated-messages' plugin v1.0.2 exhibits a strong security posture based on the provided static analysis. The absence of any identified attack surface entry points like AJAX handlers, REST API routes, shortcodes, or cron events is a significant strength. Furthermore, the code demonstrates excellent practices by utilizing prepared statements for all SQL queries and ensuring all output is properly escaped. The lack of dangerous functions, file operations, external HTTP requests, and the absence of taint analysis findings further bolster its security.
However, the complete absence of nonce and capability checks is a notable concern. While there's no current attack surface exposed, any future addition of functionality without these fundamental WordPress security mechanisms would introduce significant risks. The vulnerability history being entirely clear is positive and suggests a well-maintained plugin, but it's important to remember that this is based on past data and doesn't guarantee future security. In conclusion, while the current implementation of 'post-updated-messages' appears very secure due to its limited scope and adherence to secure coding practices for SQL and output, the lack of authorization checks on potential future entry points is a weakness that warrants attention.
Key Concerns
- No nonce checks implemented
- No capability checks implemented
Post Updated Messages Security Vulnerabilities
Post Updated Messages Release Timeline
Post Updated Messages Code Analysis
Output Escaping
Post Updated Messages Attack Surface
WordPress Hooks 4
Maintenance & Trust
Post Updated Messages Maintenance & Trust
Maintenance Signals
Community Trust
Post Updated Messages Alternatives
Post Admin Word Count
post-admin-word-count
Adds a sortable word count column to the admin post list for all public post types. Efficient, lightweight and built with modern best practices.
More Types
more-types
Adds any number of extra Post types, besides Post and Page, for the WordPess Admin. Also allows for special editing rights for specific User roles for …
At A Glance Widget Plus
at-a-glance-widget-plus
A WordPress plugin to extend the core at a glance widget. This adds available custom post types and their count on at a glance widget.
Abandon Themes Admin
abandon-theme-options
This is a WordPress plugin that adds an admin options page to your theme and all the main options a theme designer would need.
Comments by Post Type
comments-by-post-type
Separate comments by post type in admin menu.
Post Updated Messages Developer Profile
7 plugins · 120 total installs
How We Detect Post Updated Messages
Patterns used to identify this plugin on WordPress sites during automated security audits and web crawling.