Podamibe Appointment Calendar Security & Risk Analysis
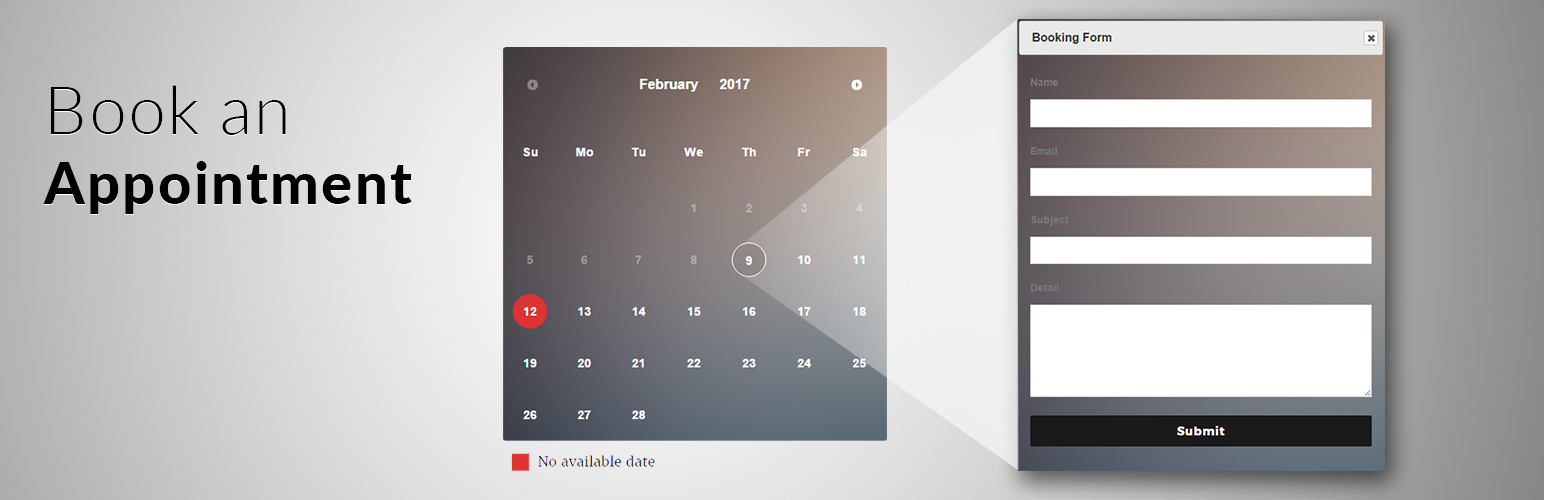
wordpress.org/plugins/podamibe-appointment-calendarDisplay your appointment,availability,book date on calendar with various layout and form in more easier and quicker way.
Is Podamibe Appointment Calendar Safe to Use in 2026?
Generally Safe
Score 85/100Podamibe Appointment Calendar has no known CVEs and is actively maintained. It's a solid choice for most WordPress installations.
The "podamibe-appointment-calendar" plugin v1.1.6 exhibits several concerning security practices, despite having no recorded historical vulnerabilities. The static analysis reveals a significant attack surface with 3 out of 4 entry points lacking authentication checks. This is particularly worrisome as 100% of the detected SQL queries are not using prepared statements, making them highly susceptible to SQL injection attacks if an unauthenticated user can trigger them. Furthermore, the presence of a taint flow with unsanitized paths, flagged as high severity, indicates a potential for arbitrary code execution or data compromise. The low percentage of properly escaped output (23%) also suggests a risk of Cross-Site Scripting (XSS) vulnerabilities. While the plugin has no known CVEs, the identified weaknesses in authentication, input sanitization, and output escaping create a substantial risk profile. The absence of capability checks on entry points further amplifies these risks.
Key Concerns
- AJAX handlers without auth checks
- SQL queries without prepared statements
- High severity taint flow with unsanitized paths
- Low percentage of properly escaped output
- No capability checks on entry points
Podamibe Appointment Calendar Security Vulnerabilities
Podamibe Appointment Calendar Release Timeline
Podamibe Appointment Calendar Code Analysis
SQL Query Safety
Output Escaping
Data Flow Analysis
Podamibe Appointment Calendar Attack Surface
AJAX Handlers 3
Shortcodes 1
WordPress Hooks 8
Maintenance & Trust
Podamibe Appointment Calendar Maintenance & Trust
Maintenance Signals
Community Trust
Podamibe Appointment Calendar Alternatives
Pinpoint Booking System – Version 2
booking-system
Book anything, anytime, anywhere.
Booking System Trafft
booking-system-trafft
Trafft is a next-level booking system offering limitless opportunities for scheduling appointments and managing your calendar & all of your bookings.
8 Degree Availability Calendar
8-degree-availability-calendar
Availability Calendar | Simple Booking Calendar | Appointment Calendar | check availability calendar
Doctor Appointment Booking Plugin – EMSB
emsb-service-booking
Allow your customers to book your service like appointment, event, reservation, etc. Manage your bookings through wp admin dashboard.
TalkHours Widget
talkhours
Adds online appointment booking to your Wordpress site ... for FREE !
Podamibe Appointment Calendar Developer Profile
8 plugins · 6K total installs
How We Detect Podamibe Appointment Calendar
Patterns used to identify this plugin on WordPress sites during automated security audits and web crawling.
Asset Fingerprints
/wp-content/plugins/podamibe-appointment-calendar/assets/pac-calendar.css/wp-content/plugins/podamibe-appointment-calendar/assets/pac-front-style.css/wp-content/plugins/podamibe-appointment-calendar/assets/pac-front-style-two.css/wp-content/plugins/podamibe-appointment-calendar/assets/pac-front-style-three.css/wp-content/plugins/podamibe-appointment-calendar/assets/pac-calendar.js/wp-content/plugins/podamibe-appointment-calendar/assets/pac-front.js/wp-content/plugins/podamibe-appointment-calendar/assets/pac-backend-style.css/wp-content/plugins/podamibe-appointment-calendar/assets/pac-extra.js+1 morepodamibe-appointment-calendar/assets/pac-calendar.css?ver=podamibe-appointment-calendar/assets/pac-front-style.css?ver=podamibe-appointment-calendar/assets/pac-front-style-two.css?ver=podamibe-appointment-calendar/assets/pac-front-style-three.css?ver=podamibe-appointment-calendar/assets/pac-calendar.js?ver=podamibe-appointment-calendar/assets/pac-front.js?ver=podamibe-appointment-calendar/assets/pac-backend-style.css?ver=podamibe-appointment-calendar/assets/pac-extra.js?ver=podamibe-appointment-calendar/assets/pac-color-picker.js?ver=HTML / DOM Fingerprints
pac-calendar-wrapperPAC_TEXT_DOMAINPAC_VERSIONpac_localize_backend_array