Password Strength Requirements for Woocommerce Security & Risk Analysis
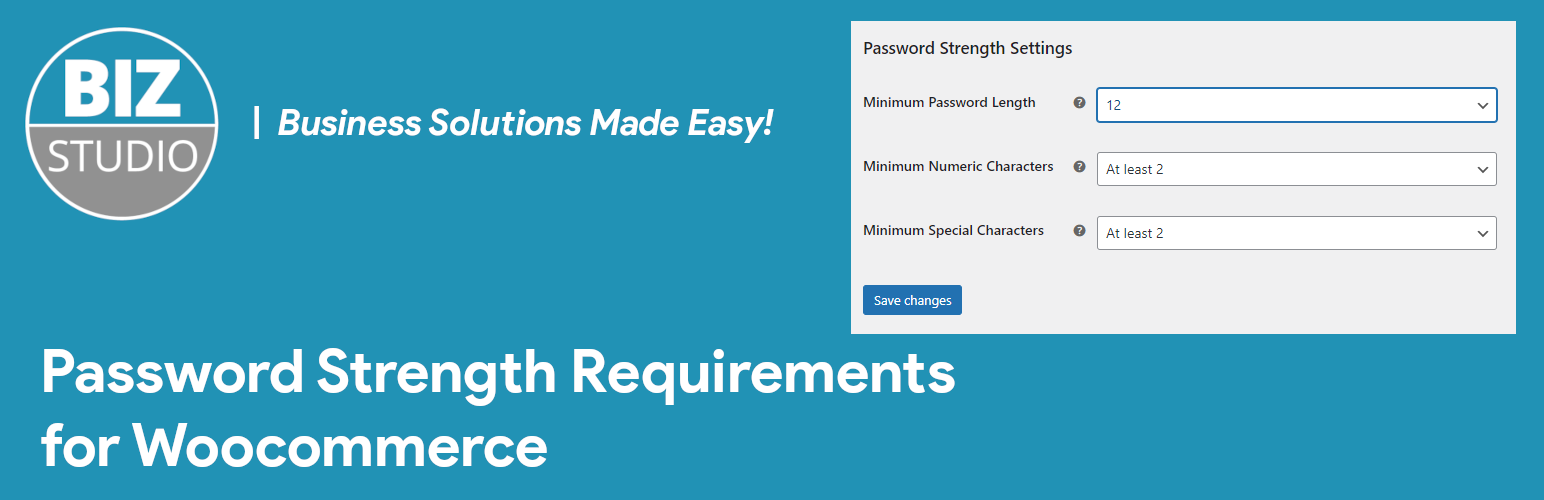
wordpress.org/plugins/password-strength-rwcShort Description: A plugin to customise password strength requirements in WooCommerce.
Is Password Strength Requirements for Woocommerce Safe to Use in 2026?
Generally Safe
Score 92/100Password Strength Requirements for Woocommerce has no known CVEs and is actively maintained. It's a solid choice for most WordPress installations.
The 'password-strength-rwc' plugin version 1.1.0 exhibits a strong security posture based on the provided static analysis. There are no identified dangerous functions, no raw SQL queries, and all output appears to be properly escaped. The plugin also demonstrates good practice by incorporating a nonce check and zero identified flows with unsanitized paths, indicating a well-implemented defense against common web vulnerabilities. The lack of any historical vulnerabilities further reinforces this positive assessment, suggesting a history of secure development and maintenance.
However, the complete absence of any attack surface entry points (AJAX handlers, REST API routes, shortcodes, cron events) is unusual and could be a sign that the plugin's functionality is extremely limited or relies entirely on frontend JavaScript without any server-side interaction. While this reduces direct attack vectors, it also means the plugin's security in practice is difficult to fully assess without understanding its actual implementation and usage. The lack of capability checks on any potential, though currently non-existent, entry points is a minor concern; if functionality were added in the future, proper permission checks would be crucial. Overall, the plugin appears secure based on the data, but its limited apparent attack surface warrants further investigation into its actual scope of operation.
Password Strength Requirements for Woocommerce Security Vulnerabilities
Password Strength Requirements for Woocommerce Code Analysis
Output Escaping
Password Strength Requirements for Woocommerce Attack Surface
WordPress Hooks 3
Maintenance & Trust
Password Strength Requirements for Woocommerce Maintenance & Trust
Maintenance Signals
Community Trust
Password Strength Requirements for Woocommerce Alternatives
Password Strength for WooCommerce
password-strength-for-woocommerce
Disables password strength enforcement in WooCommerce.
Captcha by BestWebSoft – Advanced Spam Protection, Math & OCR-Friendly Captcha for Site Forms
captcha-bws
1 The Ultimate Spam Protection Plugin Using Captcha for WordPress Forms.
Password Strength Settings for WooCommerce
wc-password-strength-settings
Help secure your WooCommerce site by enforcing stronger passwords and taking additional control of your strength requirements.
WP Advanced Math Captcha
wp-advanced-math-captcha
Protect your WordPress site with a powerful and user-friendly Math Captcha. Now with seamless WooCommerce, WPForms, and Formidable Forms integration!
Password Policy Manager | Password Manager
password-policy-manager
Enforce strong passwords with expiry, reset, score checks, inactive user lock, and user password management using Password Policy Manager.
Password Strength Requirements for Woocommerce Developer Profile
2 plugins · 120 total installs
How We Detect Password Strength Requirements for Woocommerce
Patterns used to identify this plugin on WordPress sites during automated security audits and web crawling.
Asset Fingerprints
HTML / DOM Fingerprints
bzwps_min_password_lengthbzwps_min_numeric_charsbzwps_min_special_chars