MegaSend for WooCommerce Security & Risk Analysis
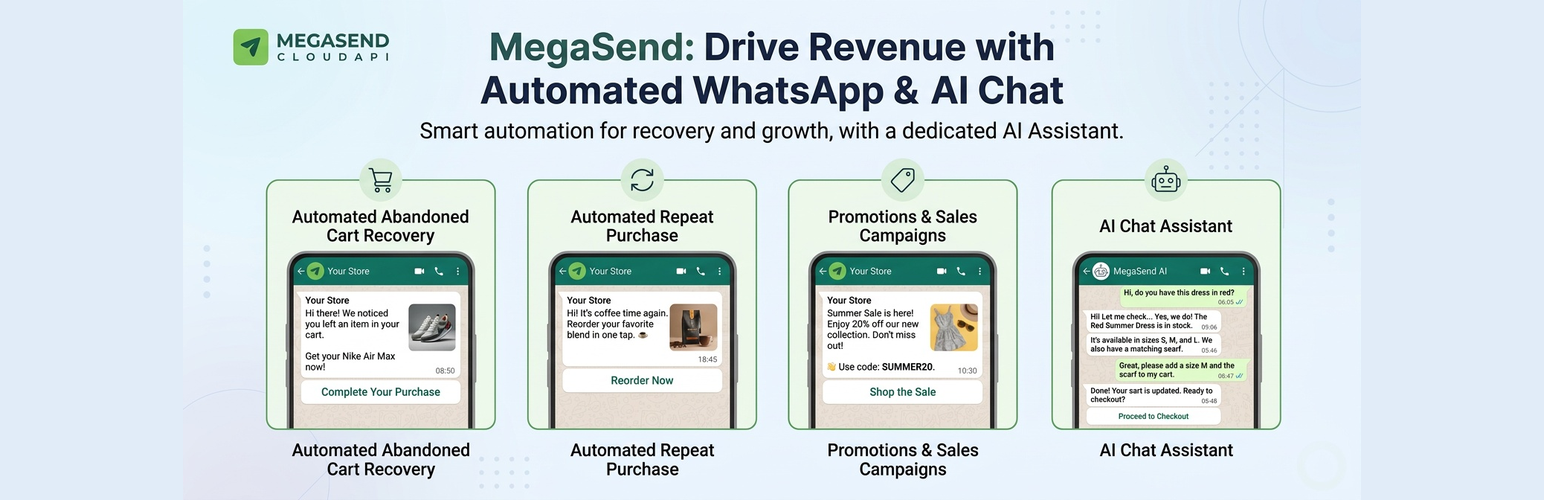
wordpress.org/plugins/megasend-for-woocommerceRecover abandoned carts and boost sales with automated WhatsApp messages powered by MegaSend.
Is MegaSend for WooCommerce Safe to Use in 2026?
Generally Safe
Score 100/100MegaSend for WooCommerce has no known CVEs and is actively maintained. It's a solid choice for most WordPress installations.
The "megasend-for-woocommerce" plugin version 1.0.2 exhibits a generally good security posture, with several strong practices in place. The complete absence of raw SQL queries, 100% output escaping, and a single nonce and capability check on its two AJAX entry points are commendable. Furthermore, the plugin has no recorded vulnerability history, which suggests a history of responsible development or diligent patching by users if past issues existed.
However, the analysis does reveal some areas of concern. The taint analysis identified three "flows with unsanitized paths" with a high severity. While the static analysis didn't immediately map these to exploitable vulnerabilities, this is a significant red flag. It implies that user-supplied data might be processed in a way that could lead to security issues, particularly if these paths are accessible without proper validation or sanitization, even if they don't immediately manifest as SQL injection or XSS. The two external HTTP requests also warrant careful review to ensure they are not susceptible to SSRF or other network-related vulnerabilities.
In conclusion, while the plugin benefits from a clean vulnerability history and good core security practices like prepared statements and output escaping, the high-severity unsanitized taint flows represent a notable risk. Addressing these potential pathways for unsanitized data is crucial for a truly robust security profile. The overall risk is moderate, leaning towards good, but with a clear need for investigation into the identified taint flows.
Key Concerns
- High severity unsanitized taint flows
MegaSend for WooCommerce Security Vulnerabilities
MegaSend for WooCommerce Release Timeline
MegaSend for WooCommerce Code Analysis
SQL Query Safety
Output Escaping
Data Flow Analysis
MegaSend for WooCommerce Attack Surface
AJAX Handlers 2
WordPress Hooks 24
Maintenance & Trust
MegaSend for WooCommerce Maintenance & Trust
Maintenance Signals
Community Trust
MegaSend for WooCommerce Alternatives
CartSaver Chat Recovery
cartsaver-chat-recovery
Recover WooCommerce abandoned carts automatically via Official WhatsApp API or one-click manual links.
Quick Cart Recovery
quick-cart-recovery
Recover lost WooCommerce sales instantly via WhatsApp chat. A lightweight and powerful abandoned cart recovery tool.
ShopNotify – Personalized Cart Recovery for WooCommerce
shopnotify
Track abandoned carts for logged-in and guest users in WooCommerce, send automated WhatsApp reminders, and gain insights into cart recovery and abando …
Booster for WooCommerce – PDF Invoices, Abandoned Cart, Variation Swatches & 100+ Tools
woocommerce-jetpack
Supercharge WooCommerce with FREE Abandoned Cart Recovery, Product Variation Swatches, PDF Invoices & 100+ tools. Boost sales & save time.
Abandoned Cart Recovery for WooCommerce
woo-abandoned-cart-recovery
A simple, effective solution to capture abandoned carts and auto-send reminders. Track logs and generate reports on carts, emails, and more
MegaSend for WooCommerce Developer Profile
1 plugin · 0 total installs
How We Detect MegaSend for WooCommerce
Patterns used to identify this plugin on WordPress sites during automated security audits and web crawling.
Asset Fingerprints
/wp-content/plugins/megasend-for-woocommerce/admin/build/index.js/wp-content/plugins/megasend-for-woocommerce/admin/build/index.cssmegasend-woo-adminmegasend-for-woocommerceHTML / DOM Fingerprints
megasendWoo/wp-json/megasend-woo/v1