Logto – User Authentication and Authorization Security & Risk Analysis
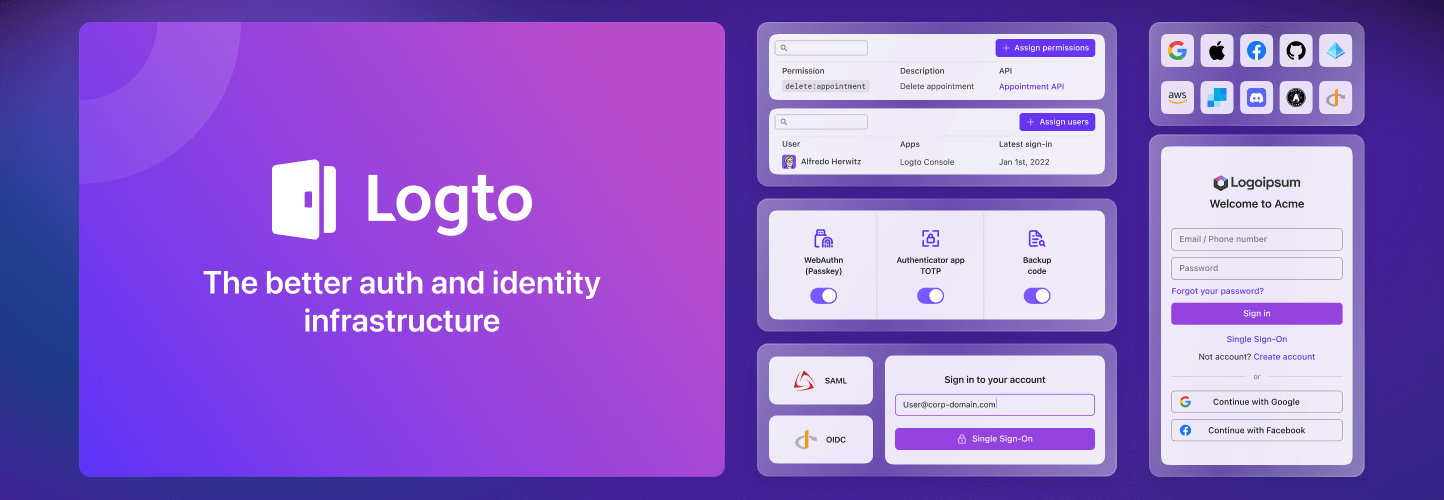
wordpress.org/plugins/logtoEnable beautiful and secure user authentication, including passwordless, social login, single sign-on, multi-factor authentication (MFA), and more.
Is Logto – User Authentication and Authorization Safe to Use in 2026?
Generally Safe
Score 92/100Logto – User Authentication and Authorization has no known CVEs and is actively maintained. It's a solid choice for most WordPress installations.
The logto v1.0.1 plugin exhibits an exceptionally strong security posture based on the provided static analysis. The absence of any identified attack surface points, dangerous functions, unescaped output, file operations, or external HTTP requests is highly commendable and suggests meticulous development practices aimed at minimizing potential vulnerabilities. The complete reliance on prepared statements for any potential SQL queries further solidifies this positive assessment, indicating robust data sanitization against SQL injection. The lack of any recorded CVEs in its history, spanning all severity levels, further reinforces the impression of a secure plugin that has maintained its integrity over time.
While the static analysis reveals no immediate concerns, the total absence of nonce checks and capability checks, despite the plugin having a zero-point attack surface, warrants a slight reservation. Although no entry points were found to exploit, best practices typically involve implementing these checks for any potential future expansion or unexpected interactions. The bundled Guzzle library, while not inherently a vulnerability, does represent a dependency that could, in the future, inherit vulnerabilities from its own ecosystem. However, based on the current data, this plugin is evaluated as highly secure with no direct exploitable flaws identified.
Key Concerns
- Missing nonce checks
- Missing capability checks
- Bundled library (Guzzle) potential future risk
Logto – User Authentication and Authorization Security Vulnerabilities
Logto – User Authentication and Authorization Release Timeline
Logto – User Authentication and Authorization Code Analysis
Bundled Libraries
Output Escaping
Logto – User Authentication and Authorization Attack Surface
WordPress Hooks 10
Maintenance & Trust
Logto – User Authentication and Authorization Maintenance & Trust
Maintenance Signals
Community Trust
Logto – User Authentication and Authorization Alternatives
SSO Login – Universal (OAuth + SAML)
authress
SSO Login provides user login, business authentication, SSO, Social login, and Single Sign-On for all sites.
Login for Google Apps
google-apps-login
Simple secure login and user management through your Google Workspace for WordPress (using oAuth2 and MFA if enabled).
OAuth Single Sign On – SSO (OAuth Client)
miniorange-login-with-eve-online-google-facebook
WordPress SSO (Single Sign On) with Azure, Azure B2C, Cognito, Okta, Classlink, Discord, Clever, Keycloak, OAuth & OpenID Providers [24/7 SUPPORT].
Log in with Google
login-with-google
Minimal plugin that allows WordPress users to log in using Google.
SAML IDP (Identity Provider) – Login with Website Users
miniorange-wp-as-saml-idp
Single sign on (SSO) login with WordPress Users into any Service Provider like Tableau, Thinkific, Zoom, Moodle LMS, Canvas LMS, Absorb LMS, TalentLMS
Logto – User Authentication and Authorization Developer Profile
1 plugin · 20 total installs
How We Detect Logto – User Authentication and Authorization
Patterns used to identify this plugin on WordPress sites during automated security audits and web crawling.
Asset Fingerprints
/wp-content/plugins/logto/assets/admin-menu.css/wp-content/plugins/logto/assets/admin-settings.cssHTML / DOM Fingerprints
data-logto-endpointdata-logto-client-iddata-logto-redirect-uridata-logto-scopedata-logto-extra-paramsdata-logto-post-sign-out-redirect-uri+2 morelogtoLogto