LogMate Security & Risk Analysis
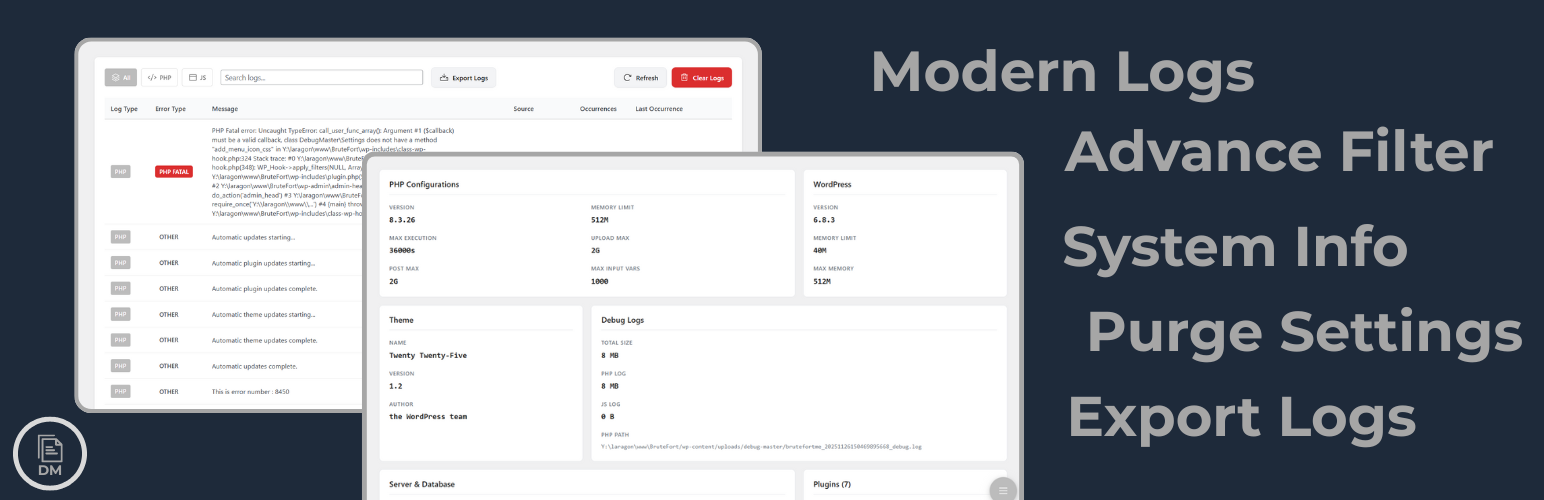
wordpress.org/plugins/logmateModern log management and export for WordPress with purging, filtering, and export. by BruteFort
Is LogMate Safe to Use in 2026?
Generally Safe
Score 100/100LogMate has no known CVEs and is actively maintained. It's a solid choice for most WordPress installations.
The plugin "logmate" v1.0.0 demonstrates a strong security posture with no known CVEs and a complete absence of critical or high-severity findings in the static and taint analysis. The code adheres to good security practices by utilizing prepared statements for all SQL queries, implementing nonce checks, and performing capability checks for its limited entry points. The high percentage of properly escaped output further indicates a diligent approach to preventing cross-site scripting vulnerabilities. The plugin's attack surface is minimal, with no apparent AJAX handlers, REST API routes, shortcodes, or cron events, significantly reducing the potential for unauthorized access or manipulation. The single flow with an unsanitized path, while not flagged as critical or high severity, warrants attention as it represents a potential area for improvement in input validation, particularly if it involves file operations. Overall, "logmate" v1.0.0 appears to be a securely developed plugin, with its vulnerability history being completely clear, suggesting a commitment to security by its developers.
Key Concerns
- Flow with unsanitized path detected
LogMate Security Vulnerabilities
LogMate Code Analysis
Output Escaping
Data Flow Analysis
LogMate Attack Surface
WordPress Hooks 7
Maintenance & Trust
LogMate Maintenance & Trust
Maintenance Signals
Community Trust
LogMate Alternatives
WP Developer's Toolbox
wp-developers-toolbox
"Great for turning DEBUG mode on and off - quickly!" * Hide or show error notifications - globally or conditionally!
Debug Log Manager – Conveniently Monitor and Inspect Errors
debug-log-manager
Log PHP, database and JavaScript errors via WP_DEBUG with one click. Conveniently create, view, filter and clear the debug.log file.
Developer Loggers for Simple History
developer-loggers-for-simple-history
Useful loggers for SimpleHistory for developers during development of a site or to maintain a live site.
Error Logs Emailer for WooCommerce
error-logs-emailer-for-woocommerce
Sends the previous day's WooCommerce fatal error log to specified email(s) using Action Scheduler.
Debug Console for PHP
debug-console-php
Log, Debug, Inspect ("Debug Bar" on steroids)
LogMate Developer Profile
2 plugins · 0 total installs
How We Detect LogMate
Patterns used to identify this plugin on WordPress sites during automated security audits and web crawling.
Asset Fingerprints
/wp-content/plugins/logmate/dist/assets/index.js/wp-content/plugins/logmate/dist/assets/vendor.js/wp-content/plugins/logmate/dist/assets/index.js/wp-content/plugins/logmate/dist/assets/vendor.jslogmate/dist/assets/index.js?ver=logmate/dist/assets/vendor.js?ver=HTML / DOM Fingerprints
logmate-admin-appdata-logmate-urldata-logmate-noncelogmate_vars/wp-json/logmate/