LoginRadius CIAM Security & Risk Analysis
wordpress.org/plugins/loginradius-customer-identity-and-access-managementFeatures of this Plugin A clean, user friendly WP admin U/I. Users can login via hosted page. Log generation functionality.
Is LoginRadius CIAM Safe to Use in 2026?
Generally Safe
Score 85/100LoginRadius CIAM has no known CVEs and is actively maintained. It's a solid choice for most WordPress installations.
The "loginradius-customer-identity-and-access-management" plugin v4.4.0 presents a mixed security posture. While the absence of known vulnerabilities and a generally low count of entry points are positive indicators, the static analysis reveals several concerning areas. The fact that 100% of its SQL queries are not using prepared statements is a significant risk, potentially exposing the application to SQL injection vulnerabilities. Furthermore, the low percentage of properly escaped output (28%) suggests a high likelihood of cross-site scripting (XSS) vulnerabilities, as data displayed to users may not be sanitized, allowing attackers to inject malicious scripts. The presence of file operations without clear indications of sanitization is another point of concern.
The plugin's vulnerability history is clean, with no recorded CVEs. This is a strong positive sign, suggesting that the developers may have a good security awareness or that previous versions have not been extensively targeted or found to be vulnerable. However, the static analysis findings, particularly concerning SQL and output escaping, indicate potential weaknesses that could lead to vulnerabilities. It is crucial to address these static code issues to maintain a strong security profile. The current lack of exploitable issues is a strength, but the underlying code quality concerns in the static analysis warrant attention.
Key Concerns
- SQL queries not using prepared statements
- Low percentage of properly escaped output
- File operations present without clear sanitization
- No nonce checks
LoginRadius CIAM Security Vulnerabilities
LoginRadius CIAM Release Timeline
LoginRadius CIAM Code Analysis
SQL Query Safety
Output Escaping
Data Flow Analysis
LoginRadius CIAM Attack Surface
Shortcodes 9
WordPress Hooks 86
Maintenance & Trust
LoginRadius CIAM Maintenance & Trust
Maintenance Signals
Community Trust
LoginRadius CIAM Alternatives
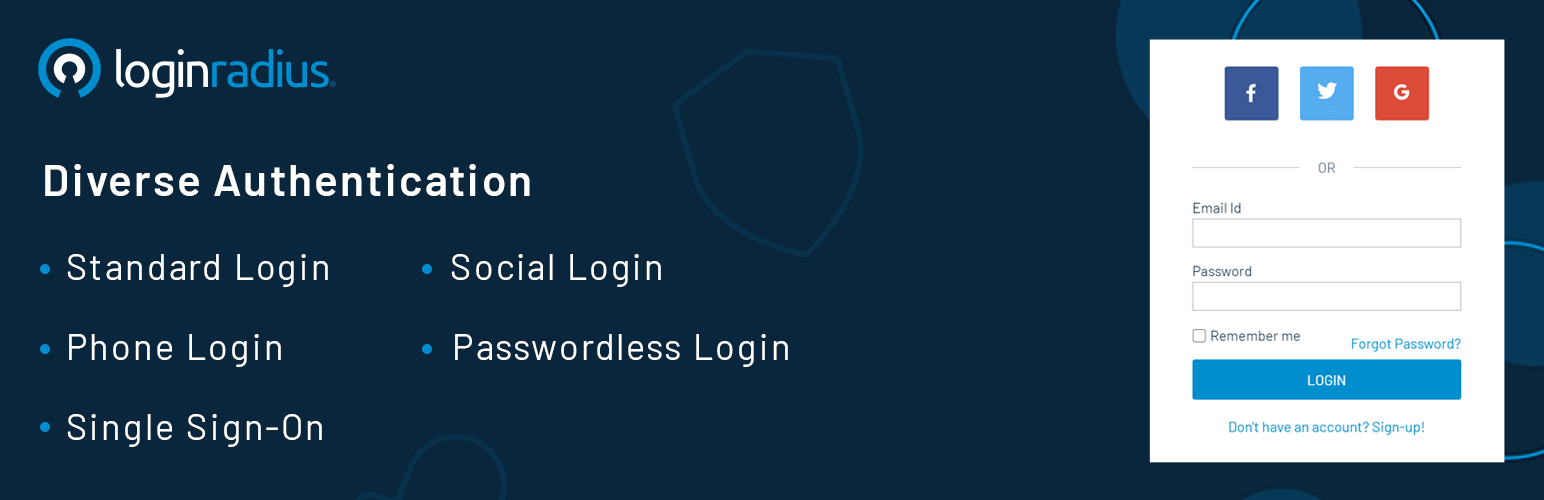
Authentication by LoginRadius
loginradius-for-wordpress
The Authentication by LoginRadius WordPress plugin allow you to replace the default WordPress Authentication feature with diverse authentication metho …
JSON API User
json-api-user
Extends the JSON API Plugin to allow RESTful user registration, authentication & many other User Meta, BP functions. A Pro version is also available.
All-In-One Security (AIOS) – Security and Firewall
all-in-one-wp-security-and-firewall
Protect your website investment with All-In-One Security (AIOS) – a comprehensive and easy to use security plugin designed especially for WordPress.
Solid Security – Password, Two Factor Authentication, and Brute Force Protection
better-wp-security
Harden your site security with Login Security, Two-Factor Authentication (2FA), Vulnerability Scanner, Firewall, and more. Formerly iThemes Security.
Limit Login Attempts
limit-login-attempts
Limit rate of login attempts, including by way of cookies, for each IP. Fully customizable.
LoginRadius CIAM Developer Profile
2 plugins · 100 total installs
How We Detect LoginRadius CIAM
Patterns used to identify this plugin on WordPress sites during automated security audits and web crawling.
Asset Fingerprints
/wp-content/plugins/loginradius-customer-identity-and-access-management/auto-loader.php/wp-content/plugins/loginradius-customer-identity-and-access-management/activation/admin/class-activation.php/wp-content/plugins/loginradius-customer-identity-and-access-management/authentication/lib/WPHttpClient.php/wp-content/plugins/loginradius-customer-identity-and-access-management/authentication/lib/LoginRadiusSDK/Clients/IHttpClientInterface.php/wp-content/plugins/loginradius-customer-identity-and-access-management/authentication/lib/LoginRadiusSDK/Clients/DefaultHttpClient.php/wp-content/plugins/loginradius-customer-identity-and-access-management/authentication/lib/LoginRadiusSDK/LoginRadiusException.php/wp-content/plugins/loginradius-customer-identity-and-access-management/authentication/lib/LoginRadiusSDK/Utility/Functions.php/wp-content/plugins/loginradius-customer-identity-and-access-management/authentication/lib/LoginRadiusSDK/CustomerRegistration/Advanced/ConfigurationAPI.php/wp-content/plugins/loginradius-customer-identity-and-access-management/js/common.js/wp-content/plugins/loginradius-customer-identity-and-access-management/js/admin.jsloginradius-customer-identity-and-access-management/js/common.js?ver=loginradius-customer-identity-and-access-management/js/admin.js?ver=HTML / DOM Fingerprints
<!-- LoginRadius CIAM Settings --><!-- End LoginRadius CIAM Settings -->data-plugin-name="loginradius-ciam"data-plugin-version="4.4.0"LoginRadius_ObjlrAPIClientlrAppConfiglrAPIUrllrID/wp-json/loginradius-ciam/v1/integration/status/wp-json/loginradius-ciam/v1/integration/enable/wp-json/loginradius-ciam/v1/integration/disable[loginradius_login][loginradius_social_login][loginradius_registration][loginradius_forgot_password]