JS Injector Security & Risk Analysis
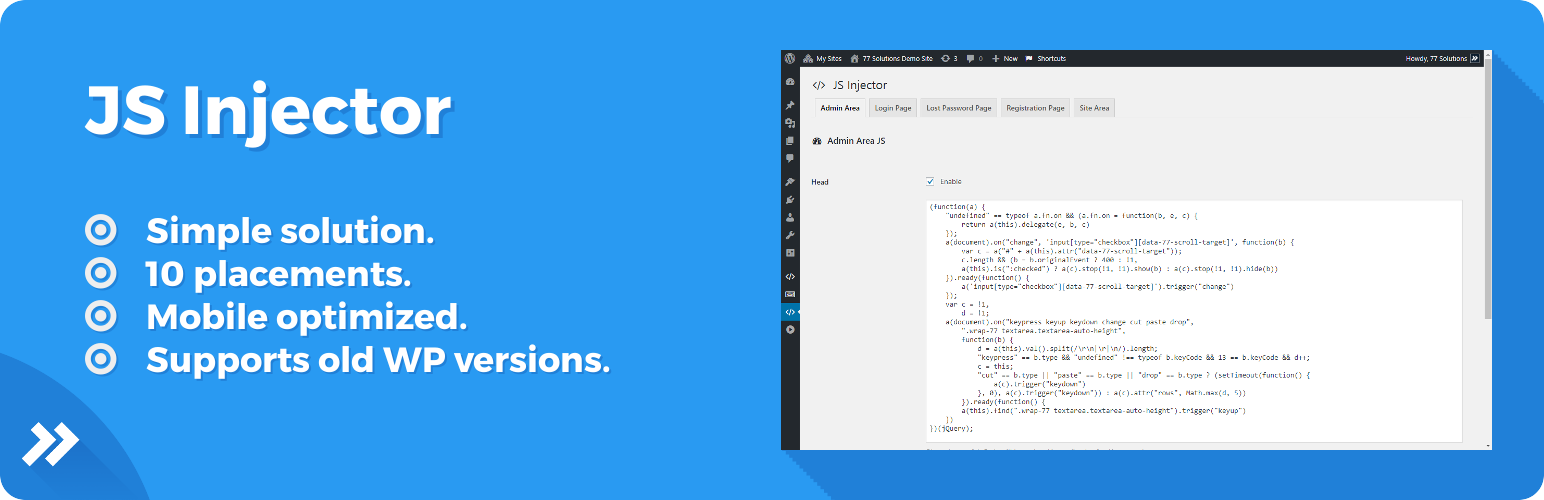
wordpress.org/plugins/js-injectorSuper simple solution to add, edit and control custom JS code in selected area of Your WordPress website. Check long description.
Is JS Injector Safe to Use in 2026?
Generally Safe
Score 85/100JS Injector has no known CVEs and is actively maintained. It's a solid choice for most WordPress installations.
The js-injector v1.0.0 plugin presents a mixed security posture. On the positive side, it exhibits no known vulnerabilities in its history and uses prepared statements for all SQL queries, which is a strong defense against SQL injection. The absence of AJAX handlers, REST API routes, shortcodes, and cron events significantly limits its direct attack surface and potential for direct unauthenticated exploitation.
However, the static analysis reveals significant concerns regarding output escaping. With 40 total outputs and 0% properly escaped, there is a high risk of Cross-Site Scripting (XSS) vulnerabilities. Any data that is outputted by this plugin without proper sanitization or escaping could be manipulated by an attacker to inject malicious scripts into the user's browser. Furthermore, the taint analysis indicating 10 flows with unsanitized paths, despite no critical or high severity classifications in this specific run, is a warning sign that potentially sensitive data might not be handled securely. The presence of file operations also warrants careful review depending on their nature and how they interact with user-supplied data.
While the vulnerability history is clean, this does not guarantee future security, especially given the identified weaknesses in output handling. The plugin's strengths lie in its limited attack surface and secure SQL practices. Its primary weakness is the prevalent lack of output escaping, which could lead to XSS vulnerabilities. A balanced conclusion is that while the plugin avoids common pitfalls like unpatched CVEs and insecure SQL, the unescaped output is a critical flaw that requires immediate attention. The taint analysis further reinforces the need for thorough code review of how data is processed and displayed.
Key Concerns
- 0% properly escaped output
- 10 flows with unsanitized paths
- No nonce checks
- No capability checks
JS Injector Security Vulnerabilities
JS Injector Release Timeline
JS Injector Code Analysis
Output Escaping
Data Flow Analysis
JS Injector Attack Surface
WordPress Hooks 7
Maintenance & Trust
JS Injector Maintenance & Trust
Maintenance Signals
Community Trust
JS Injector Alternatives
Simple Custom CSS and JS
custom-css-js
Easily add Custom CSS or JS to your website with an awesome editor.
TC Custom JavaScript
tc-custom-javascript
Add custom JavaScript to your site from a professional editor in the WordPress admin.
Custom CSS
custom-css-editor
Add custom CSS, JS, PHP, tracking code. Very easy to use!
Live Custom CSS JS Code Editor
live-css-js-code-editor
Live Custom CSS JS Code Editor allows you to easily add custom CSS, JavaScript, Header, Footer Code to your site, straight from your WordPress Customi …
Custom JS
custom-js
Custom JS is easy to use. Custom JS WordPress plugin allows you to Custom JS fields in your theme - include js in head or footer.
JS Injector Developer Profile
2 plugins · 70 total installs
How We Detect JS Injector
Patterns used to identify this plugin on WordPress sites during automated security audits and web crawling.
Asset Fingerprints
/wp-content/plugins/js-injector/_core/1.0.0L/js/77-scripts.js/wp-content/plugins/js-injector/_core/1.0.0L/js/77-styles.js/wp-content/plugins/js-injector/assets/css/dashboard.css/wp-content/plugins/js-injector/assets/js/dashboard.js/wp-content/plugins/js-injector/_core/1.0.0L/js/77-scripts.js/wp-content/plugins/js-injector/_core/1.0.0L/js/77-styles.js/wp-content/plugins/js-injector/assets/js/dashboard.jsjs-injector/_core/1.0.0L/js/77-scripts.js?ver=js-injector/_core/1.0.0L/js/77-styles.js?ver=js-injector/assets/css/dashboard.css?ver=js-injector/assets/js/dashboard.js?ver=HTML / DOM Fingerprints
js-injector-dashboard-formJS Injector - DashboardThis file is part of JS Injector.JS Injector is free software: you can redistribute it and/or modifyJS Injector is distributed in the hope that it will be useful,+2 moredata-js-injector-iddata-js-injector-typedata-js-injector-statusjsInjectorDashboard