Invoices by Customer Security & Risk Analysis
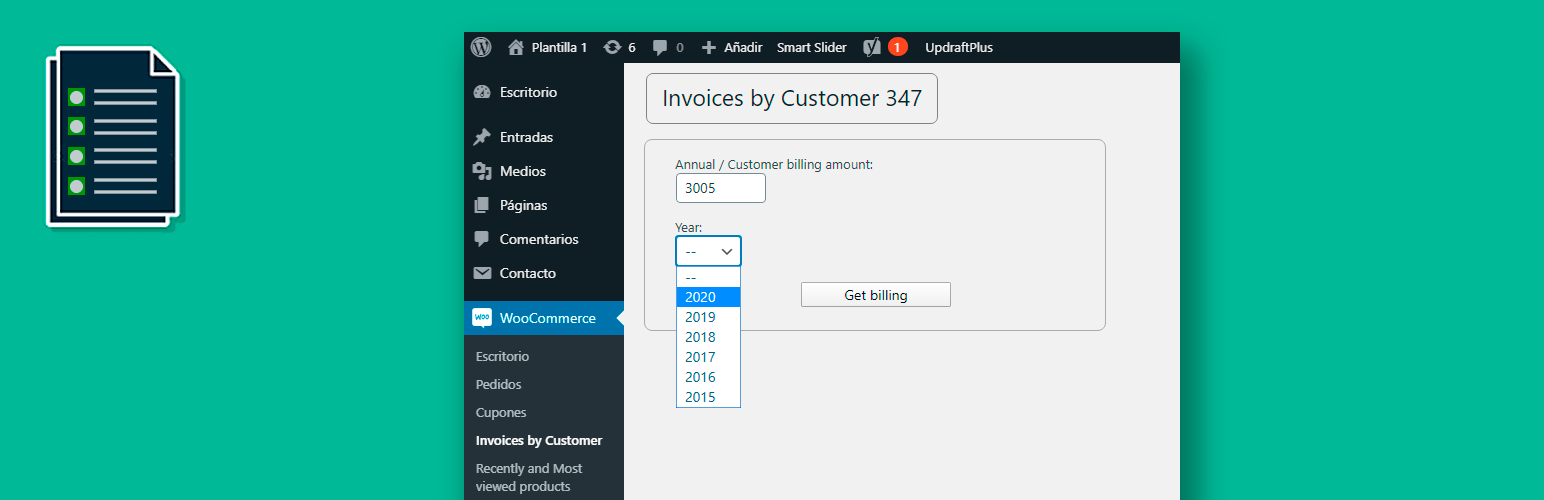
wordpress.org/plugins/invoices-by-customer-347Obtain a list of invoices by quarter and year for customers who exceed a certain amount.
Is Invoices by Customer Safe to Use in 2026?
Generally Safe
Score 85/100Invoices by Customer has no known CVEs and is actively maintained. It's a solid choice for most WordPress installations.
The plugin 'invoices-by-customer-347' v1.0.3 exhibits a mixed security posture. On the positive side, it has a zero attack surface exposed via AJAX, REST API, shortcodes, or cron events. The code also shows strong adherence to output escaping practices, with 98% of outputs properly escaped, and no dangerous functions, file operations, or external HTTP requests were detected. The absence of any recorded vulnerabilities in its history is also a significant positive indicator.
However, there are notable concerns stemming from the static analysis. The taint analysis revealed two flows with unsanitized paths, both flagged as high severity. This indicates a potential for sensitive data to be mishandled or exposed if these paths are exploited. Furthermore, while the plugin uses prepared statements for 33% of its SQL queries, 67% do not, posing a risk of SQL injection vulnerabilities. The complete absence of nonce checks and capability checks across all entry points (though limited) is also a weakness that could be exploited if entry points were to be introduced or discovered.
In conclusion, while the plugin demonstrates good practices in output escaping and has a clean vulnerability history, the presence of high-severity taint flows and the significant proportion of SQL queries not using prepared statements present tangible risks. The lack of robust authentication checks on potential (even if currently zero) entry points is also a concern. Addressing the taint flows and securing the SQL queries should be the immediate priorities.
Key Concerns
- High severity taint flows found
- SQL queries not using prepared statements (67%)
- No nonce checks on entry points
- No capability checks on entry points
Invoices by Customer Security Vulnerabilities
Invoices by Customer Release Timeline
Invoices by Customer Code Analysis
SQL Query Safety
Output Escaping
Data Flow Analysis
Invoices by Customer Attack Surface
WordPress Hooks 2
Maintenance & Trust
Invoices by Customer Maintenance & Trust
Maintenance Signals
Community Trust
Invoices by Customer Alternatives
Subscriptions for WooCommerce
subscriptions-for-woocommerce
With WooCommerce Subscription, turn your physical or online store into a WooCommerce product subscription store and avail recurring revenue.
YITH WooCommerce Subscription
yith-woocommerce-subscription
It allows you to manage recurring payments for product subscription that grant you constant periodical income
WHMCS Bridge
whmcs-bridge
WHMCS Bridge is a plugin that integrates the powerful WHMCS support and billing software with WordPress.
Billingo Official for WooCommerce
billingo
Hivatalos Billingo összeköttetés WooCommerce-hez.
Remove Checkout Fields for Woocommerce
remove-default-checkout-fields-for-woocommerce
Remove Fields from woocommerce Checkout page
Invoices by Customer Developer Profile
4 plugins · 510 total installs
How We Detect Invoices by Customer
Patterns used to identify this plugin on WordPress sites during automated security audits and web crawling.
Asset Fingerprints
/wp-content/plugins/invoices-by-customer-347/style-347.cssinvoices-by-customer-347/style-347.css?ver=