Insert Update Time Security & Risk Analysis
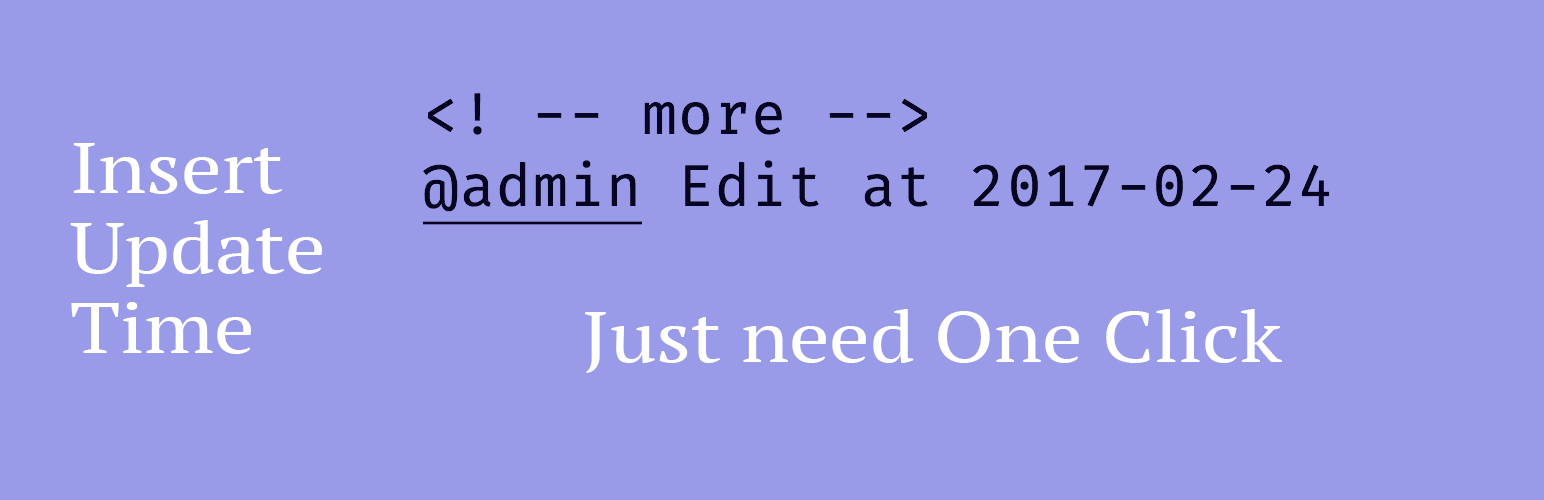
wordpress.org/plugins/insert-update-timeYou can get a New Button On your TinyMCE Editor to add Your Update Signature in your post or page.
Is Insert Update Time Safe to Use in 2026?
Generally Safe
Score 85/100Insert Update Time has no known CVEs and is actively maintained. It's a solid choice for most WordPress installations.
The "insert-update-time" plugin v0.0.2 exhibits a strong adherence to secure coding practices in several key areas. The absence of any reported CVEs and a clean vulnerability history suggest a well-maintained and secure codebase historically. Furthermore, the plugin demonstrates no external HTTP requests, file operations, or dangerous function usage, which are significant positives for security. The use of prepared statements for all SQL queries is also commendable, preventing common SQL injection vulnerabilities. However, a critical weakness is identified in the handling of output. With 100% of its outputs not being properly escaped, this presents a significant risk of Cross-Site Scripting (XSS) vulnerabilities. Even with a minimal attack surface, any data displayed to users that originates from an untrusted source (e.g., user input that might indirectly influence what gets outputted) could be exploited to inject malicious scripts. The plugin also lacks nonce checks on any potential entry points, which, while currently limited, could be a vector for Cross-Site Request Forgery (CSRF) if the attack surface were to expand in future versions. The presence of capability checks is good, but their effectiveness is undermined by the unescaped output. In conclusion, while the plugin has a solid foundation regarding SQL security and avoids common plugin pitfalls, the severe lack of output escaping represents a substantial, exploitable vulnerability that needs immediate attention.
Key Concerns
- 0% of outputs properly escaped
- No nonce checks on any entry points
Insert Update Time Security Vulnerabilities
Insert Update Time Release Timeline
Insert Update Time Code Analysis
Output Escaping
Insert Update Time Attack Surface
WordPress Hooks 5
Maintenance & Trust
Insert Update Time Maintenance & Trust
Maintenance Signals
Community Trust
Insert Update Time Alternatives
Black Studio TinyMCE Widget
black-studio-tinymce-widget
The visual editor widget for WordPress.
AddQuicktag
addquicktag
This plugin makes it easy to add Quicktags to the html - and visual-editor.
Post and Page Builder by BoldGrid – Visual Drag and Drop Editor
post-and-page-builder
Post and Page Builder is a standalone plugin which adds functionality to the existing TinyMCE Editor.
TinyMCE Templates
tinymce-templates
TinyMCE Template plugin will enable to use HTML template on WordPress Visual Editor.
Advanced Image Styles
advanced-image-styles
Adjust an image's margins and border with ease in the Visual editor.
Insert Update Time Developer Profile
12 plugins · 180 total installs
How We Detect Insert Update Time
Patterns used to identify this plugin on WordPress sites during automated security audits and web crawling.
Asset Fingerprints
/wp-content/plugins/insert-update-time/insert-update-time.css/wp-content/plugins/insert-update-time/insert-update-time.jsHTML / DOM Fingerprints
<!--more-->QTags