Images Optimize and Upload CF7 Security & Risk Analysis
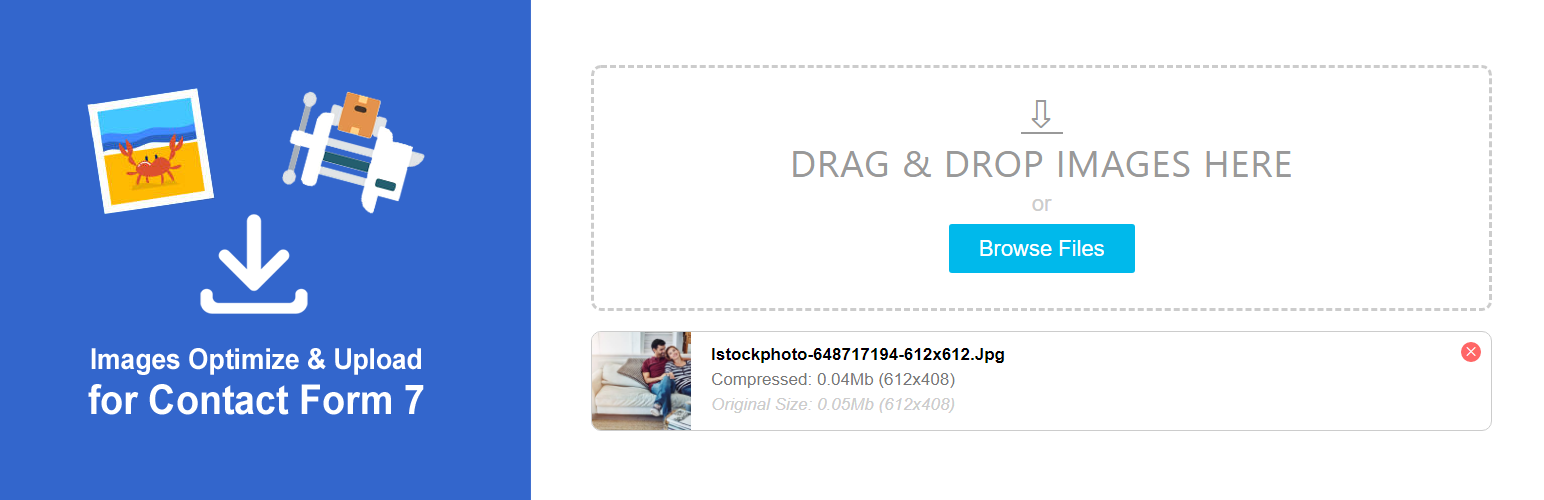
wordpress.org/plugins/images-optimize-and-upload-cf7Allows uploading and client-side compression of multiple images in Contact Form 7.
Is Images Optimize and Upload CF7 Safe to Use in 2026?
Generally Safe
Score 98/100Images Optimize and Upload CF7 has a strong security track record. Known vulnerabilities have been patched promptly. It's a solid choice for most WordPress installations.
The plugin "images-optimize-and-upload-cf7" v2.2.1 exhibits a mixed security posture. While it demonstrates good practices such as using prepared statements for all SQL queries and a high percentage of properly escaped output, significant security concerns arise from its attack surface and vulnerability history. The presence of two AJAX handlers without authentication checks is a major red flag, as these can be exploited by unauthenticated users to perform unintended actions. The lack of nonce checks and capability checks further exacerbates this risk, as it provides no mechanism to verify the origin or user's permission for these AJAX requests. The plugin's vulnerability history includes one critical CVE marked as missing authorization, which directly aligns with the findings in the static analysis. This pattern suggests a recurring weakness in authorization controls within the plugin. While the absence of critical taint flows and dangerous functions is positive, the unprotected AJAX endpoints and past critical vulnerability related to authorization present a substantial risk that needs immediate attention.
Key Concerns
- Unprotected AJAX handlers present
- Missing nonce checks on AJAX
- Missing capability checks
- One critical CVE historically
Images Optimize and Upload CF7 Security Vulnerabilities
CVEs by Year
Severity Breakdown
1 total CVE
Images Optimize and Upload CF7 <= 2.1.4 - Missing Authorization to Arbitrary File Deletion
Images Optimize and Upload CF7 Release Timeline
Images Optimize and Upload CF7 Code Analysis
Output Escaping
Images Optimize and Upload CF7 Attack Surface
AJAX Handlers 2
WordPress Hooks 11
Maintenance & Trust
Images Optimize and Upload CF7 Maintenance & Trust
Maintenance Signals
Community Trust
Images Optimize and Upload CF7 Alternatives
Drag and Drop Multiple File Upload for Contact Form 7
drag-and-drop-multiple-file-upload-contact-form-7
This simple plugin create Drag & Drop or choose Multiple File upload in your Confact Form 7 Forms.
Drag and Drop File Upload for Contact Form 7
drag-and-drop-file-upload-for-contact-form-7
Best Drag & Drop File Upload solution for Contact Form 7. Professional, fast AJAX-based uploading, and fully mobile responsive.
Multiple Files for Contact Form 7
multiple-files-for-contact-form-7
Multiple Files is addon for Contact Form 7
TinyPNG – JPEG, PNG & WebP image compression
tiny-compress-images
Speed up your website. Optimize your JPEG, PNG, and WebP images automatically with TinyPNG.
MultiLine Files for Contact Form 7
multiline-files-for-contact-form-7
Upload unlimited files to Contact Form 7 with an intuitive interface, file management, and automatic ZIP compression for email delivery.
Images Optimize and Upload CF7 Developer Profile
1 plugin · 600 total installs
How We Detect Images Optimize and Upload CF7
Patterns used to identify this plugin on WordPress sites during automated security audits and web crawling.
Asset Fingerprints
/wp-content/plugins/images-optimize-and-upload-cf7/frontend/js/custom-select.js/wp-content/plugins/images-optimize-and-upload-cf7/frontend/js/dropzone.js/wp-content/plugins/images-optimize-and-upload-cf7/frontend/js/images-optimize.js/wp-content/plugins/images-optimize-and-upload-cf7/frontend/js/custom-select.js/wp-content/plugins/images-optimize-and-upload-cf7/frontend/js/dropzone.js/wp-content/plugins/images-optimize-and-upload-cf7/frontend/js/images-optimize.jsimages-optimize-and-upload-cf7/frontend/js/custom-select.js?ver=images-optimize-and-upload-cf7/frontend/js/dropzone.js?ver=images-optimize-and-upload-cf7/frontend/js/images-optimize.js?ver=HTML / DOM Fingerprints
custom-selectdropzonecf7-images-optimize-uploaddata-namemax-file-errormax-fileyr3k_optimizer_3000<input type="file"