IF Menu Visibility Security & Risk Analysis
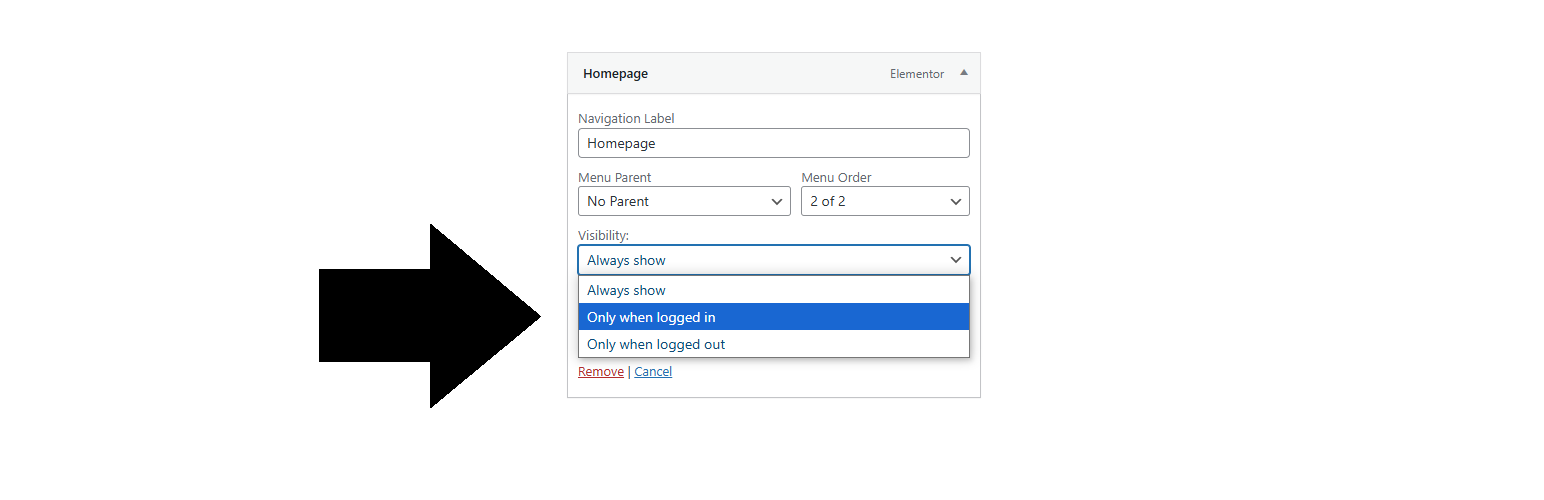
wordpress.org/plugins/if-menu-visibilityAdd login-based visibility control to WordPress menus. Show or hide menu items depending on whether users are logged in or not.
Is IF Menu Visibility Safe to Use in 2026?
Generally Safe
Score 100/100IF Menu Visibility has no known CVEs and is actively maintained. It's a solid choice for most WordPress installations.
The "if-menu-visibility" plugin, version 1.0.5, demonstrates a strong security posture based on the provided static analysis and vulnerability history. The absence of any AJAX handlers, REST API routes, shortcodes, or cron events significantly limits its attack surface, with zero identified unprotected entry points. The code analysis reveals excellent adherence to security best practices, including 100% proper output escaping, 100% of SQL queries using prepared statements, and the presence of both nonce and capability checks.
Furthermore, the plugin has no recorded vulnerabilities (CVEs) and no flagged taint analysis flows, indicating a clean codebase without apparent critical or high-severity flaws. The lack of file operations and external HTTP requests further minimizes potential vectors for compromise. This robust set of positive indicators suggests a well-developed and secure plugin that prioritizes user safety.
While the plugin's current state is highly secure, it's important to maintain vigilance. The absence of past vulnerabilities is a positive sign, but ongoing security audits and prompt updates for any future discoveries would be prudent. For now, the plugin presents a very low risk to WordPress installations.
IF Menu Visibility Security Vulnerabilities
IF Menu Visibility Release Timeline
IF Menu Visibility Code Analysis
Output Escaping
IF Menu Visibility Attack Surface
WordPress Hooks 9
Maintenance & Trust
IF Menu Visibility Maintenance & Trust
Maintenance Signals
Community Trust
IF Menu Visibility Alternatives
Different Menu in Different Pages – Conditional Menu
different-menus-in-different-pages
Easily assign different menus to pages, posts, user roles, devices, and custom URLs using advanced conditional menu visibility rules.
Menu Ghost
menu-ghost
Target menu items by role, device, schedule, and campaign rules using a fast, native conditions interface inside the menu editor.
When Last Login
when-last-login
Show a users last login date by creating a sortable column in your WordPress users list.
Require Login for WooCommerce
woo-for-logged-users
Set the WooCommerce Shop only for logged-in users. Just activate the plugin.
Menu By User Roles
menu-by-user-roles
Menu By User Roles allows you to control the visibility of menu items based on user roles.
IF Menu Visibility Developer Profile
2 plugins · 640 total installs
How We Detect IF Menu Visibility
Patterns used to identify this plugin on WordPress sites during automated security audits and web crawling.
Asset Fingerprints
/wp-content/plugins/if-menu-visibility/if-menu-visibility.phpHTML / DOM Fingerprints
field-if-menu-visibilityname="menu-item-if-visibilityid="edit-menu-item-if-visibility-