Identityplus Security & Risk Analysis
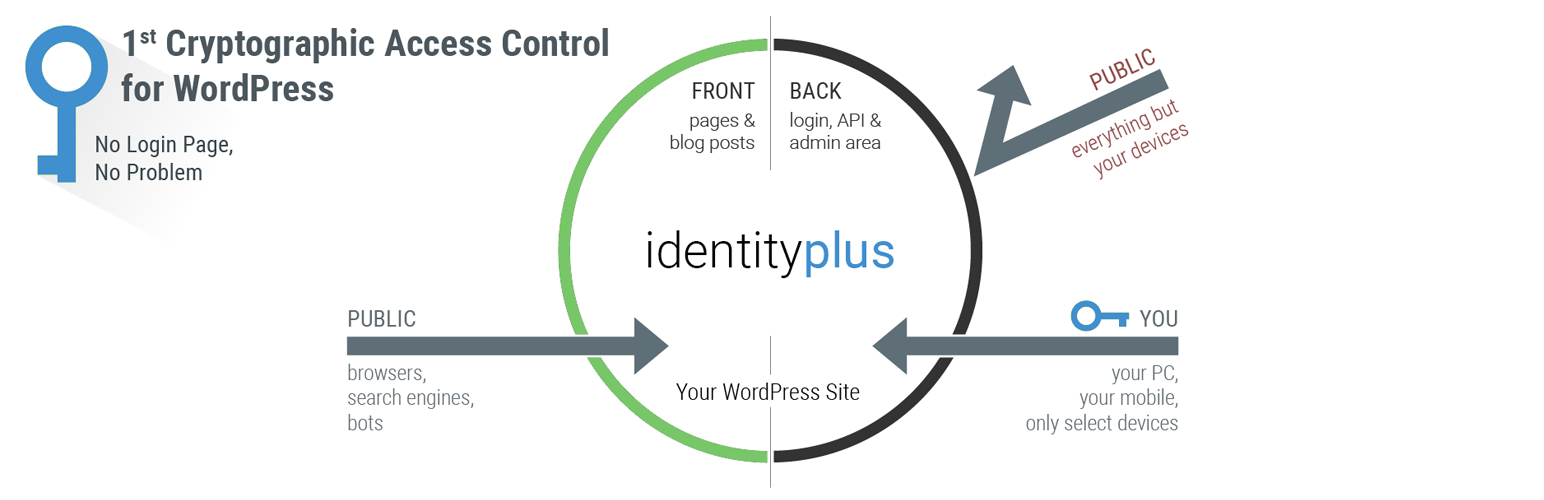
wordpress.org/plugins/identity-plusIdentityplus is a novel security solution based on PKI (Public Key Infrastructure) called a network of trust. It features an all-in-one 2 (ocasionally …
Is Identityplus Safe to Use in 2026?
Generally Safe
Score 85/100Identityplus has no known CVEs and is actively maintained. It's a solid choice for most WordPress installations.
The static analysis of "identity-plus" v2.4.3 reveals a plugin with a seemingly robust security posture based on the provided metrics. There are no identified entry points like AJAX handlers, REST API routes, shortcodes, or cron events that are exposed without authentication or permission checks. Furthermore, the code signals indicate a lack of dangerous functions, all SQL queries utilize prepared statements, and all output is properly escaped. The absence of file operations, external HTTP requests, and the explicit mention of zero nonce and capability checks are positive indicators, suggesting that the core development practices are security-conscious. The taint analysis also reports zero flows with unsanitized paths, reinforcing the impression of well-sanitized code. The plugin's vulnerability history is clean, with no recorded CVEs, which further bolsters confidence in its security. However, the complete absence of AJAX handlers, REST API routes, shortcodes, and cron events, along with zero nonce and capability checks, while appearing safe on the surface, is unusual for a plugin that likely needs to interact with WordPress in some way. This could indicate that the plugin has a very limited functionality or that the static analysis might have missed certain interaction points. The lack of recorded vulnerabilities is a strong positive, but it's important to remember that no plugin is inherently "unhackable." The current data suggests a strong defensive approach by the developers, but the absence of certain typical interaction points warrants a cautious interpretation of the overall risk.
Identityplus Security Vulnerabilities
Identityplus Release Timeline
Identityplus Code Analysis
Identityplus Attack Surface
WordPress Hooks 8
Maintenance & Trust
Identityplus Maintenance & Trust
Maintenance Signals
Community Trust
Identityplus Alternatives
Titan Anti-spam & Security
anti-spam
Block spam comments, defend against login attempts, and strengthen site security with anti-spam, brute-force protection, and two-factor authentication …
Comment Form CSRF Protection
comment-form-csrf-protection
Prevent Cross-Site Request Forgery attacks on your comments form.
Spam Comment Remover
spam-comment-remover
Automatically remove spam comments without Akismet. Universal spam detection that blocks junk, hidden links, fake names, gibberish, and automated subm …
HTML Purified
html-purified
HTML Purified replaces the default comments filters with the more secure HTML Purifier.
GhostTrap
ghosttrap
Advanced 5-layer invisible spam protection for comments. No captcha, no user friction - professional spam blocking.
Identityplus Developer Profile
1 plugin · 10 total installs
How We Detect Identityplus
Patterns used to identify this plugin on WordPress sites during automated security audits and web crawling.
Asset Fingerprints
/wp-content/plugins/identity-plus/lib/js/identity_plus.js/wp-content/plugins/identity-plus/lib/css/identity_plus.css/wp-content/plugins/identity-plus/lib/js/identity_plus.jsidentity-plus/lib/js/identity_plus.js?ver=identity-plus/lib/css/identity_plus.css?ver=