FetchWire Security & Risk Analysis
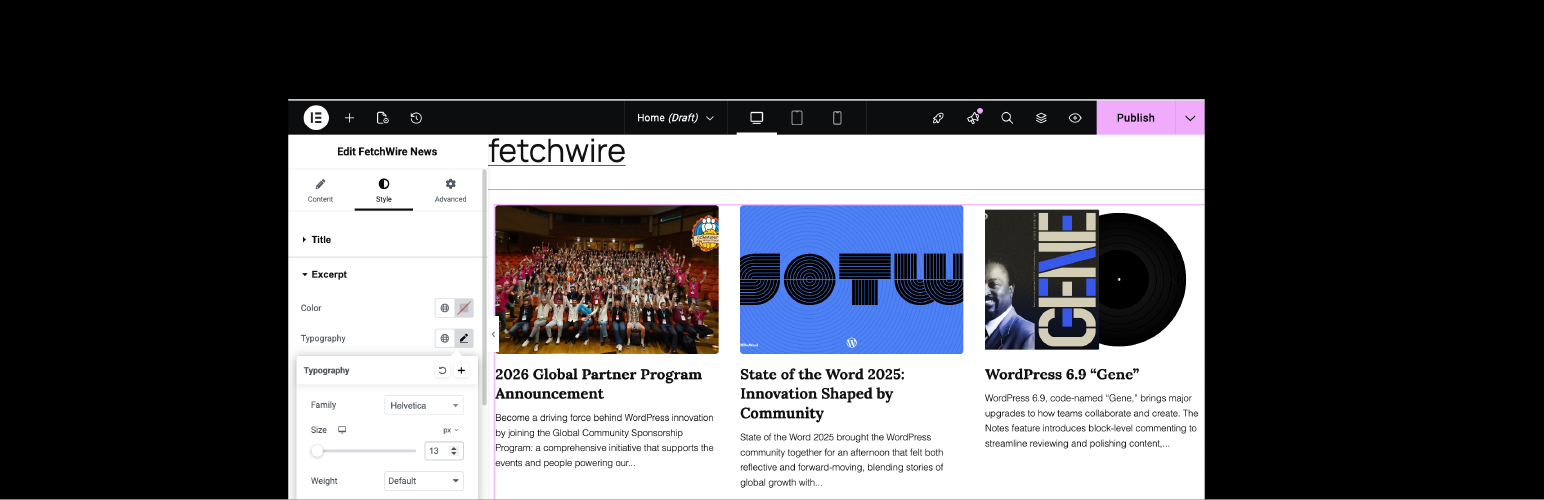
wordpress.org/plugins/fetchwireFetch and display news from any WordPress site using a powerful, highly customizable Elementor widget.
Is FetchWire Safe to Use in 2026?
Generally Safe
Score 100/100FetchWire has no known CVEs and is actively maintained. It's a solid choice for most WordPress installations.
The "fetchwire" v1.0.0 plugin exhibits a strong security posture based on the provided static analysis. The absence of any identified attack surface, including AJAX handlers, REST API routes, shortcodes, or cron events, is a significant strength. Furthermore, the complete absence of dangerous functions, file operations, and raw SQL queries (all SQL queries use prepared statements) indicates a commitment to secure coding practices. The high percentage of properly escaped output is also commendable, minimizing the risk of cross-site scripting vulnerabilities.
However, there are a couple of areas that warrant attention. The presence of two external HTTP requests without explicit mention of authentication or sanitization on the fetched data introduces a potential risk if the target endpoints are compromised or if the plugin does not properly validate the responses. Additionally, the complete absence of nonce checks and capability checks across all entry points (even though the attack surface is zero) suggests a lack of defense-in-depth, which could become a vulnerability if the plugin were to evolve and introduce new entry points without proper security measures.
The plugin's vulnerability history is entirely clear, with no known CVEs or past incidents. This, combined with the current clean code analysis, paints a picture of a well-maintained and secure plugin. Despite the minor concerns regarding external requests and the lack of specific authorization checks on non-existent entry points, the overall security of fetchwire v1.0.0 appears to be very good. Developers should continue to prioritize secure coding and consider adding checks for external requests in future updates.
Key Concerns
- External HTTP requests made without specified security checks
- Zero nonce checks present across entry points
- Zero capability checks present across entry points
FetchWire Security Vulnerabilities
FetchWire Release Timeline
FetchWire Code Analysis
Output Escaping
FetchWire Attack Surface
WordPress Hooks 2
Maintenance & Trust
FetchWire Maintenance & Trust
Maintenance Signals
Community Trust
FetchWire Alternatives
News Kit Addons For Elementor
news-kit-elementor-addons
All News focused elementor widgets that you are looking for in Elementor Page Builder. Currently, with 57 feature rich widgets and theme builder you c …
News Ticker Widget for Elementor
news-ticker-widget-for-elementor
News ticker widget for elementor helps you showcase your latest news/posts in a marquee or slider format.
Advanced Marquee Effect for Elementor
advanced-marquee-effect
Create smooth logo sliders, post sliders, and testimonial carousels in Elementor. No coding required.
News Ticker for Elementor
news-ticker-for-elementor
News icker for Elementor lets you add news ticker with the Elementor Page builder.You can use any of your blog post as news ticker.
MarqueeAll – Elementor Marquee for Image, Text, Post Grid, Testimonial, Cryptocurrency & News Ticker 🌀
marqueeall
All-in-one Elementor marquee addon for scrolling text, images, posts, testimonials, cryptocurrency price ticker, and news ticker widgets.
FetchWire Developer Profile
1 plugin · 10 total installs
How We Detect FetchWire
Patterns used to identify this plugin on WordPress sites during automated security audits and web crawling.
Asset Fingerprints
/wp-content/plugins/fetchwire/assets/css/style.cssfetchwire-style?ver=1.0.0