FDP Debug Security & Risk Analysis
wordpress.org/plugins/fdp-debugIt adds an action button to collect information to debug Freesoul Deactivate Plugins. If you don't use Freesoul Deactivate Plugins you don't …
Is FDP Debug Safe to Use in 2026?
Generally Safe
Score 100/100FDP Debug has no known CVEs and is actively maintained. It's a solid choice for most WordPress installations.
The "fdp-debug" plugin v0.0.6 exhibits a generally strong security posture based on the static analysis. The complete absence of AJAX handlers, REST API routes, shortcodes, and cron events significantly limits the plugin's attack surface, with no entry points identified as unprotected. Furthermore, the code signals indicate a lack of dangerous functions, file operations, and external HTTP requests. The use of prepared statements for all SQL queries is a positive practice. However, a notable concern is the relatively low percentage (57%) of properly escaped output, which leaves room for potential cross-site scripting (XSS) vulnerabilities.
The taint analysis also shows no critical or high severity flows with unsanitized paths, suggesting that data input is not being mishandled in ways that could lead to severe exploits. The plugin's vulnerability history is clear, with no known CVEs recorded, indicating a lack of past security incidents. This, combined with the absence of critical findings in the static analysis, points to a plugin that, at this version, has been developed with security in mind, particularly in avoiding common vulnerable patterns like raw SQL or exposed entry points.
While the plugin demonstrates strengths in limiting its attack surface and secure data handling for SQL, the moderate output escaping rate represents a potential weakness that could be exploited. The lack of recorded vulnerabilities is encouraging, but it's crucial to maintain vigilance. Future versions should aim to improve output escaping to a higher standard to mitigate XSS risks, and continued monitoring for any emerging vulnerabilities is recommended.
Key Concerns
- Moderate output escaping rate
FDP Debug Security Vulnerabilities
FDP Debug Release Timeline
FDP Debug Code Analysis
Output Escaping
Data Flow Analysis
FDP Debug Attack Surface
WordPress Hooks 2
Maintenance & Trust
FDP Debug Maintenance & Trust
Maintenance Signals
Community Trust
FDP Debug Alternatives
WP Crontrol
wp-crontrol
WP Crontrol enables you to take control of the cron events on your WordPress website.
Query Monitor
query-monitor
Query Monitor is the developer tools panel for WordPress and WooCommerce.
Debug Bar
debug-bar
Adds a debug menu to the admin bar that shows query, cache, and other helpful debugging information.
Debug Log Manager – Conveniently Monitor and Inspect Errors
debug-log-manager
Log PHP, database and JavaScript errors via WP_DEBUG with one click. Conveniently create, view, filter and clear the debug.log file.
WP Debugging
wp-debugging
A support/troubleshooting plugin for WordPress.
FDP Debug Developer Profile
58 plugins · 26K total installs
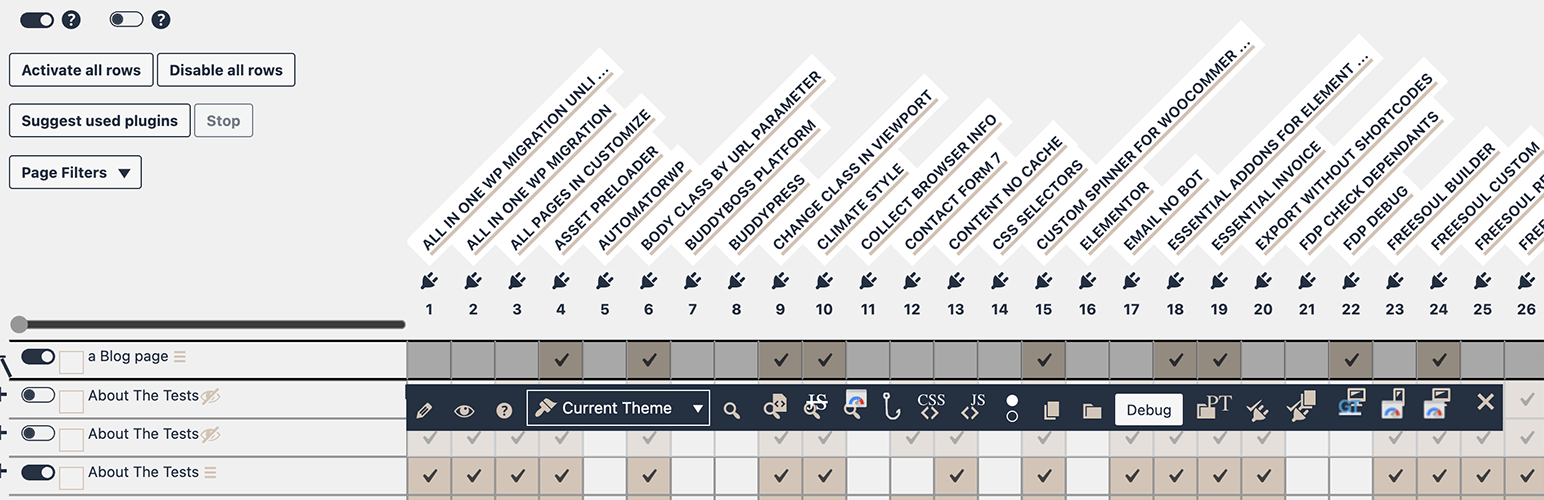
How We Detect FDP Debug
Patterns used to identify this plugin on WordPress sites during automated security audits and web crawling.
Asset Fingerprints
/wp-content/plugins/fdp-debug/css/fdp-debug.css/wp-content/plugins/fdp-debug/js/fdp-debug.js/wp-content/plugins/fdp-debug/js/fdp-debug.jsfdp-debug/css/fdp-debug.css?ver=fdp-debug/js/fdp-debug.js?ver=HTML / DOM Fingerprints
eos_dp_debug_print_disabled_pluginseos_dp_get_option