EndPointy Menus Security & Risk Analysis
wordpress.org/plugins/endpointy-menusExpose WordPress menus via a custom REST API endpoint for headless and external applications.
Is EndPointy Menus Safe to Use in 2026?
Generally Safe
Score 100/100EndPointy Menus has no known CVEs and is actively maintained. It's a solid choice for most WordPress installations.
The 'endpointy-menus' plugin version 1.1.0 exhibits a concerning security posture due to a significant portion of its attack surface being exposed without proper authorization checks. Specifically, all four identified REST API routes lack permission callbacks, meaning any authenticated user could potentially interact with these endpoints, leading to unauthorized actions or data exposure depending on their implementation. While the static analysis does not reveal dangerous functions, raw SQL, or unescaped output, the absence of nonce checks and capability checks on these REST API routes is a critical oversight that creates a wide opening for potential exploits.
The plugin's vulnerability history is clean, showing no recorded CVEs. This, combined with the absence of dangerous code signals and taint flows, suggests that the core code might be well-written in terms of preventing common vulnerabilities like SQL injection or cross-site scripting (XSS). However, this positive aspect is heavily overshadowed by the identified attack surface issues. The plugin's strength lies in its apparent lack of overtly malicious code patterns, but its weakness is the fundamental security gap in its REST API implementation.
In conclusion, while 'endpointy-menus' v1.1.0 does not appear to contain intentionally malicious code or known vulnerabilities, the direct exposure of its REST API routes without any form of authorization check presents a significant and immediate risk. This flaw could allow authenticated users to perform unintended actions. Robust permission checks are essential for all API endpoints to ensure data integrity and prevent unauthorized access.
Key Concerns
- REST API routes without permission callbacks
- No capability checks on entry points
- No nonce checks on entry points
EndPointy Menus Security Vulnerabilities
EndPointy Menus Release Timeline
EndPointy Menus Code Analysis
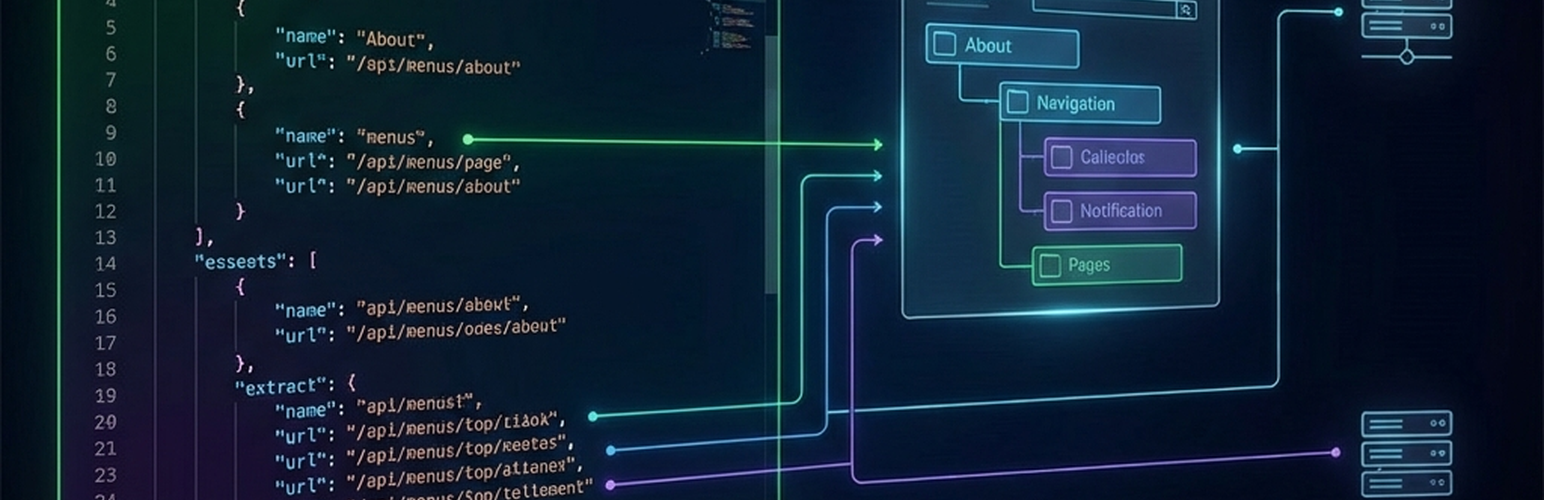
EndPointy Menus Attack Surface
REST API Routes 4
WordPress Hooks 2
Maintenance & Trust
EndPointy Menus Maintenance & Trust
Maintenance Signals
Community Trust
EndPointy Menus Alternatives
WP-REST-API V2 Menus
wp-rest-api-v2-menus
Adding menus endpoints on WP REST API v2
WP API Menus
wp-api-menus
Extends WordPress WP REST API with new routes pointing to WordPress menus.
WP-REST-API Menus
wp-rest-api-menus
Adds menu endpoints to core WP REST API.
Tutexp Rest Api Menu
tutexp-rest-api-menu
Adding menus endpoints on WP REST API v2
Disable REST API
disable-json-api
Disable the use of the REST API on your website to site users. Now with User Role support!
EndPointy Menus Developer Profile
6 plugins · 170 total installs
How We Detect EndPointy Menus
Patterns used to identify this plugin on WordPress sites during automated security audits and web crawling.
Asset Fingerprints
HTML / DOM Fingerprints
/endpointy-menus/v1/locations/endpointy-menus/v1/locations/(?P<location>[a-zA-Z0-9_-]+)/endpointy-menus/v1/menus/endpointy-menus/v1/menus/(?P<id>[0-9]+)