Duplicate Post and Clone Page Security & Risk Analysis
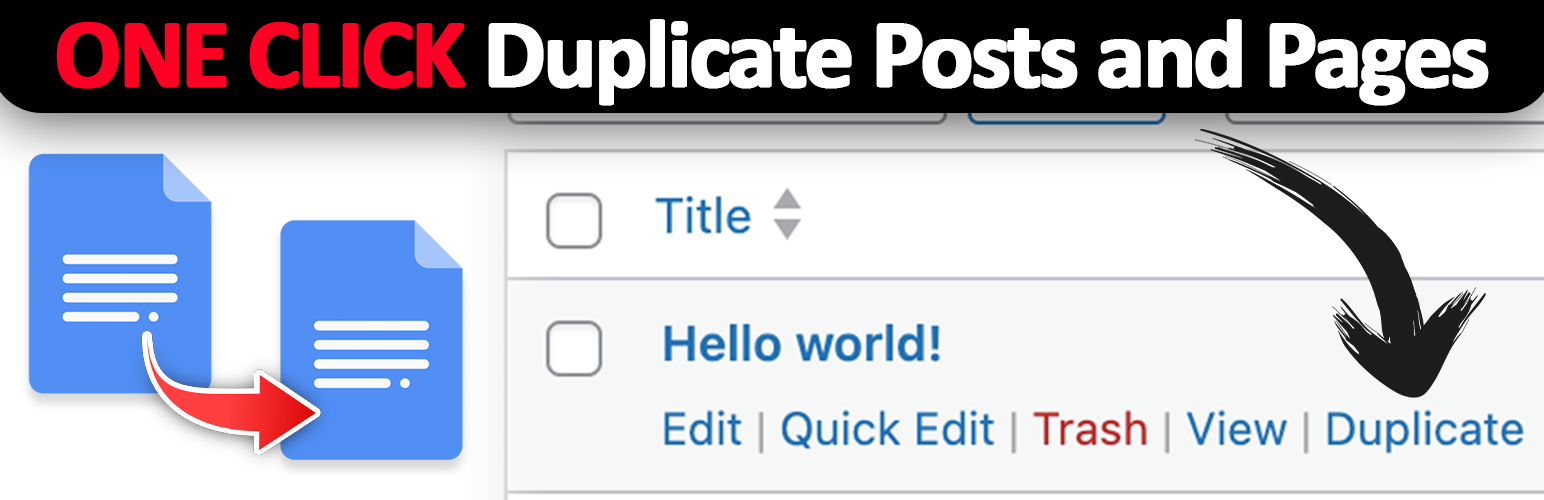
wordpress.org/plugins/duplicate-post-and-clone-pageOne click duplicate post and page. The best solution for easy copy page and post. It just works!
Is Duplicate Post and Clone Page Safe to Use in 2026?
Generally Safe
Score 92/100Duplicate Post and Clone Page has no known CVEs and is actively maintained. It's a solid choice for most WordPress installations.
The "duplicate-post-and-clone-page" plugin v1.0.0 exhibits a strong security posture based on the provided static analysis. It demonstrates excellent adherence to WordPress security best practices, with no dangerous functions, all SQL queries using prepared statements, and 100% of output properly escaped. The absence of file operations and the presence of robust nonce and capability checks on its two AJAX entry points further enhance its security. The plugin's clean vulnerability history, with no recorded CVEs, suggests a history of secure development and maintenance.
However, the plugin does make three external HTTP requests. While not explicitly flagged as a vulnerability in the static analysis, these requests represent a potential attack vector if the remote endpoints are compromised or malicious. The lack of taint analysis results (0 flows analyzed) is also a minor concern, as it implies a limited scope of analysis or potentially unanalyzed code paths that could hide vulnerabilities.
In conclusion, this plugin appears to be well-secured with no critical or high-severity vulnerabilities identified in the static analysis or historical data. The primary area for potential improvement lies in scrutinizing the security implications of its external HTTP requests and ensuring comprehensive taint analysis for any future updates.
Key Concerns
- External HTTP requests present a potential vector
- No taint analysis performed
Duplicate Post and Clone Page Security Vulnerabilities
Duplicate Post and Clone Page Release Timeline
Duplicate Post and Clone Page Code Analysis
Output Escaping
Duplicate Post and Clone Page Attack Surface
AJAX Handlers 2
WordPress Hooks 15
Maintenance & Trust
Duplicate Post and Clone Page Maintenance & Trust
Maintenance Signals
Community Trust
Duplicate Post and Clone Page Alternatives
Duplicate Post
copy-delete-posts
Duplicate post
Quick Copy – Duplicate Posts & Pages
duplicator-post-page
Easily duplicate any post or page, including all metadata and taxonomies, with just one click.
Duplicate Post – duplicate pages, copy content, clone posts
duplicate-post-rb
Duplicate Post RB makes it easy to duplicate posts, pages and custom post types. Create duplicate posts, clone content, automate duplication
Copy it
copy-it
Copy it
Clone Posts
clone-posts
Easily clone (duplicate) Posts, Pages and Custom Post Types, including their custom fields (post_meta)
Duplicate Post and Clone Page Developer Profile
1 plugin · 10 total installs
How We Detect Duplicate Post and Clone Page
Patterns used to identify this plugin on WordPress sites during automated security audits and web crawling.
Asset Fingerprints
/wp-content/plugins/duplicate-post-and-clone-page/assets/css/frontend.css/wp-content/plugins/duplicate-post-and-clone-page/assets/css/admin.cssduplicate-post-and-clone-page/assets/css/admin.css?ver=duplicate-post-and-clone-page/assets/css/frontend.css?ver=