Resource Library for Logged In Users Security & Risk Analysis
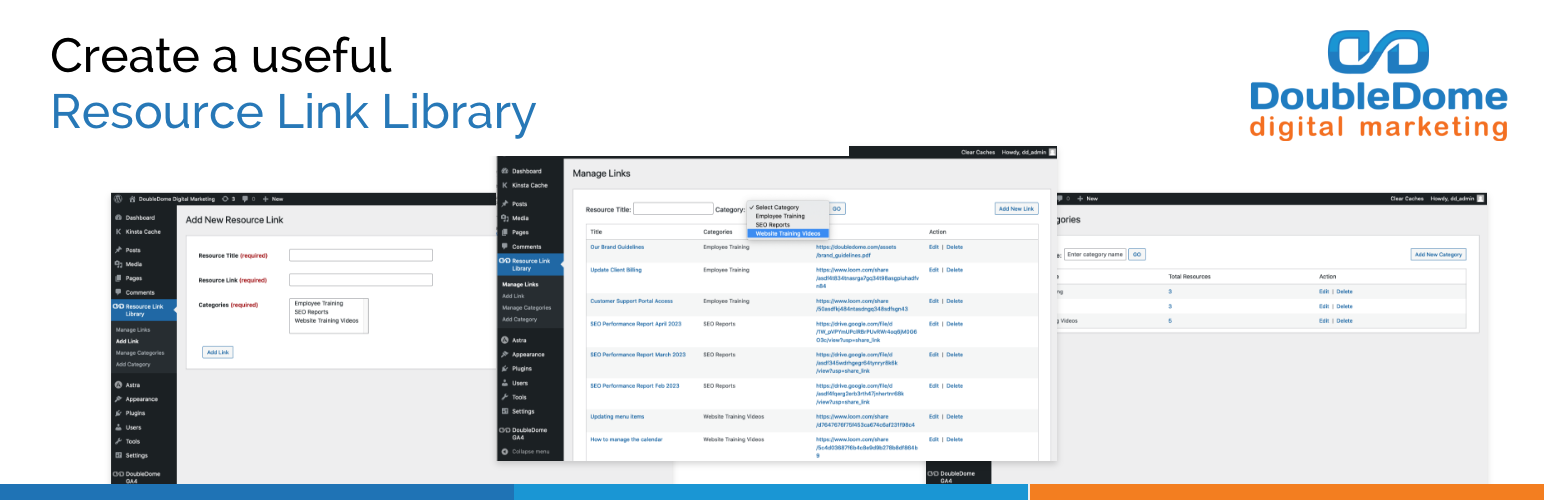
wordpress.org/plugins/doubledome-resource-link-libraryThis Resource Library, Link Library, PDF Library, Document Library, and Video Library plugin enables admins to organize and store categorized resource …
Is Resource Library for Logged In Users Safe to Use in 2026?
Generally Safe
Score 99/100Resource Library for Logged In Users has a strong security track record. Known vulnerabilities have been patched promptly. It's a solid choice for most WordPress installations.
The doubledome-resource-link-library v1.6 plugin exhibits a mixed security posture. On the positive side, the static analysis shows a clean attack surface with no identified AJAX handlers, REST API routes, shortcodes, or cron events that are unprotected. This indicates a good defensive design against common entry point exploitation. Furthermore, the plugin demonstrates awareness of security best practices by implementing a decent number of nonce and capability checks. However, there are areas for improvement. A significant concern is the relatively low percentage of SQL queries that use prepared statements, with 41% being potentially vulnerable to SQL injection if user input is not meticulously handled. Similarly, the output escaping is only properly implemented in 63% of cases, leaving room for cross-site scripting (XSS) vulnerabilities if dynamically generated content is not sanitized. The taint analysis revealed one flow with an unsanitized path, which, while not classified as critical or high, warrants attention as it represents a potential avenue for data leakage or manipulation. The vulnerability history notes one medium-severity CVE, which, although patched, highlights that the plugin has had past security weaknesses. The prevalence of Cross-Site Request Forgery (CSRF) in its history suggests a potential recurring pattern if input validation and nonce usage are not consistently robust across all functionalities. In conclusion, while the plugin has a strong foundation in limiting its attack surface, the code quality in terms of SQL prepared statements and output escaping, along with a past medium vulnerability, indicates a moderate risk profile.
Key Concerns
- SQL queries not using prepared statements
- Output escaping not properly implemented
- Taint flow with unsanitized path
- Past medium severity CVE
Resource Library for Logged In Users Security Vulnerabilities
CVEs by Year
Severity Breakdown
1 total CVE
Resource Library for Logged In Users <= 1.5 - Cross-Site Request Forgery to Multiple Administrative Actions
Resource Library for Logged In Users Release Timeline
Resource Library for Logged In Users Code Analysis
Bundled Libraries
SQL Query Safety
Output Escaping
Data Flow Analysis
Resource Library for Logged In Users Attack Surface
WordPress Hooks 2
Maintenance & Trust
Resource Library for Logged In Users Maintenance & Trust
Maintenance Signals
Community Trust
Resource Library for Logged In Users Alternatives
No alternatives data available yet.
Resource Library for Logged In Users Developer Profile
6 plugins · 620 total installs
How We Detect Resource Library for Logged In Users
Patterns used to identify this plugin on WordPress sites during automated security audits and web crawling.
Asset Fingerprints
/wp-content/plugins/doubledome-resource-link-library/assets/admin_settings.css/wp-content/plugins/doubledome-resource-link-library/assets/select2.min.css/wp-content/plugins/doubledome-resource-link-library/assets/select2.min.js/wp-content/plugins/doubledome-resource-link-library/assets/select2.min.js/wp-content/plugins/doubledome-resource-link-library/assets/admin_settings.css?ver=/wp-content/plugins/doubledome-resource-link-library/assets/select2.min.css?ver=/wp-content/plugins/doubledome-resource-link-library/assets/select2.min.js?ver=HTML / DOM Fingerprints
ddrll_box