Distributor – Remote Quickedit Security & Risk Analysis
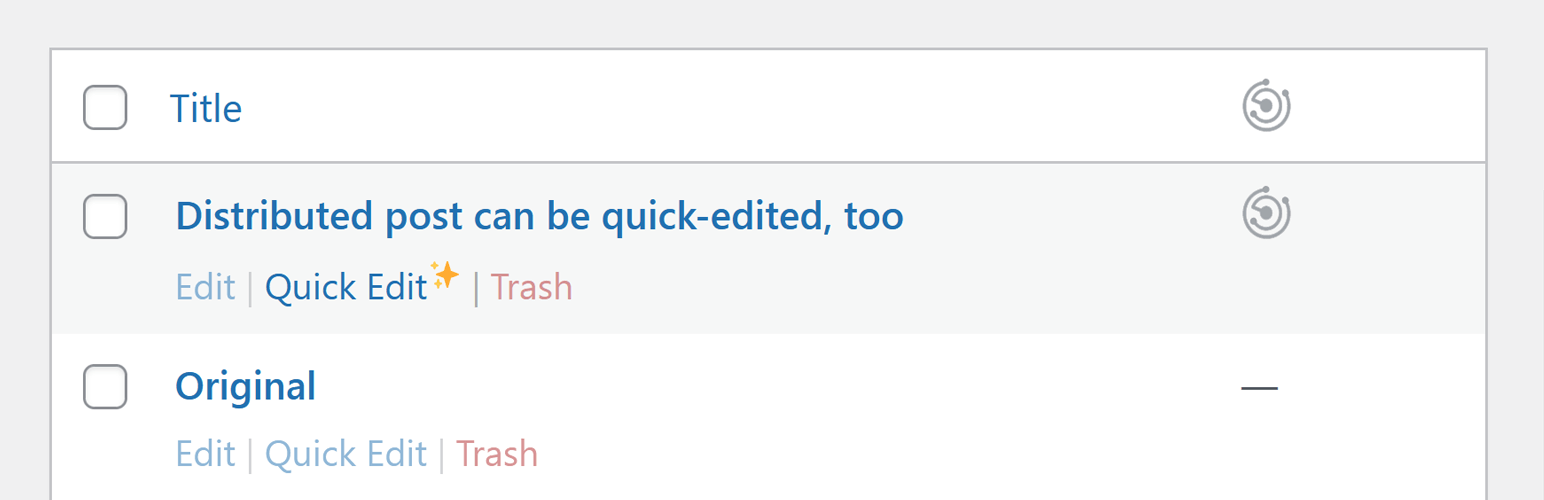
wordpress.org/plugins/distributor-remote-quickeditRe-enable quickedit for distributed posts.
Is Distributor – Remote Quickedit Safe to Use in 2026?
Generally Safe
Score 85/100Distributor – Remote Quickedit has no known CVEs and is actively maintained. It's a solid choice for most WordPress installations.
The "distributor-remote-quickedit" plugin v0.2.2 exhibits a mixed security posture. On the positive side, the code demonstrates good practices in several areas. It utilizes prepared statements for all SQL queries, ensuring protection against SQL injection. Furthermore, all identified output operations are properly escaped, mitigating cross-site scripting (XSS) vulnerabilities. The absence of file operations and external HTTP requests also reduces potential attack vectors. The plugin has no recorded vulnerability history, suggesting a stable and less frequently targeted codebase.
However, a significant concern arises from the static analysis revealing one unprotected AJAX handler within the plugin's attack surface. This handler, lacking any form of authentication or capability checks, represents a direct entry point for potential malicious activity. The complete absence of nonce checks on this AJAX handler further exacerbates this risk, making it susceptible to Cross-Site Request Forgery (CSRF) attacks. While taint analysis and vulnerability history are clean, this single unprotected entry point is a critical weakness that could be exploited if an attacker can trigger the AJAX action without proper authorization.
In conclusion, while the plugin adheres to good security practices in its handling of database queries and output, the presence of an unprotected AJAX handler is a notable weakness. The lack of any known vulnerabilities in its history is a positive sign, but it does not negate the immediate risk posed by the unauthenticated AJAX endpoint. Users should be aware of this specific vulnerability and consider mitigation strategies until it is addressed by the plugin developer.
Key Concerns
- AJAX handler without auth checks
- AJAX handler without nonce checks
Distributor – Remote Quickedit Security Vulnerabilities
Distributor – Remote Quickedit Release Timeline
Distributor – Remote Quickedit Code Analysis
Output Escaping
Distributor – Remote Quickedit Attack Surface
AJAX Handlers 1
WordPress Hooks 4
Maintenance & Trust
Distributor – Remote Quickedit Maintenance & Trust
Maintenance Signals
Community Trust
Distributor – Remote Quickedit Alternatives
ACF Quick Edit Fields
acf-quickedit-fields
Enable Columns, Filters, Quick Edit and Bulk Edit for ACF Fields in WordPress List Tables
Editorial Calendar
editorial-calendar
Editorial Calendar allows you to view all your posts, schedule post, make quick edits, and manage your blog by dragging and dropping posts.
g-FFL Cockpit
g-ffl-cockpit
Built by a FFL, for FFL's. Automate inventory synchronization and order fulfillment with multiple distributors.
Ultimate WooCommerce Brands
ultimate-woocommerce-brands
Add Brands taxonomy for products for WooCommerce plugin. Show brand name on product pages and category pages. Use widgets to display brands list.
Data Feed by TTG for WooCommerce
data-feed-by-ttg-for-woocommerce
Real-time firearm data feed for WooCommerce with support for RSR, Zanders, Sports South, Lipseys, Davidsons, and more.
Distributor – Remote Quickedit Developer Profile
3 plugins · 40 total installs
How We Detect Distributor – Remote Quickedit
Patterns used to identify this plugin on WordPress sites during automated security audits and web crawling.