DB Signatures Security & Risk Analysis
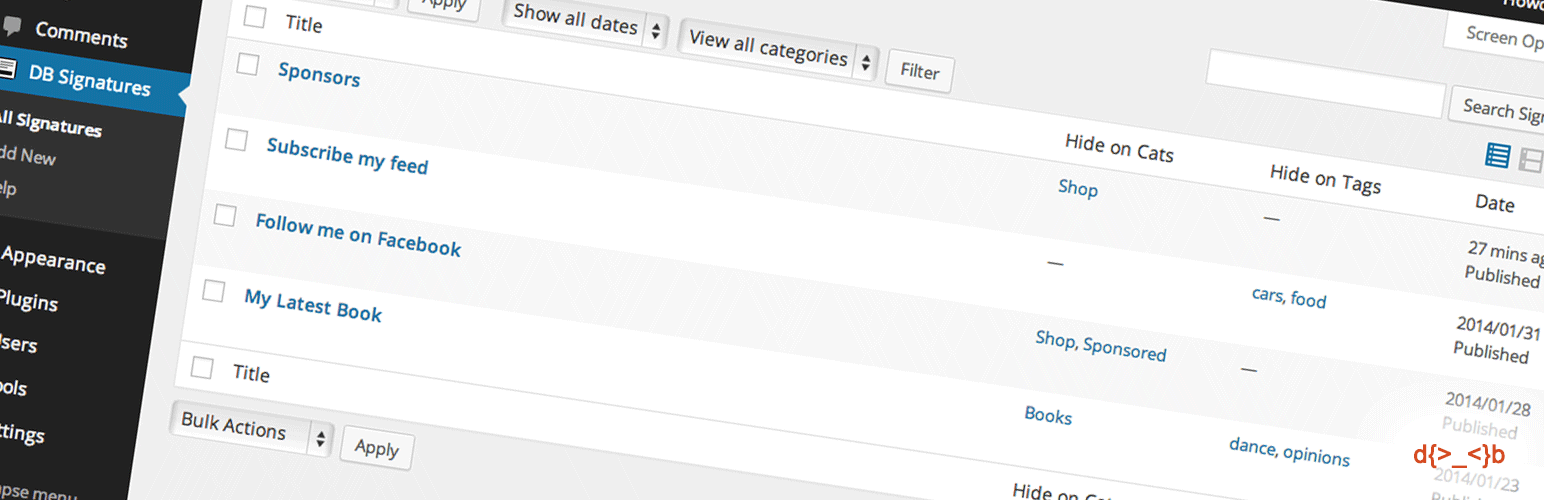
wordpress.org/plugins/db-signaturesAdd some HTML content to the bottom of every posts, pages and custom post types.
Is DB Signatures Safe to Use in 2026?
Generally Safe
Score 85/100DB Signatures has no known CVEs and is actively maintained. It's a solid choice for most WordPress installations.
The "db-signatures" v1.0 plugin exhibits a generally strong security posture based on the provided static analysis. The complete absence of AJAX handlers, REST API routes, shortcodes, and cron events significantly limits the potential attack surface. Furthermore, the reported absence of dangerous functions, file operations, and external HTTP requests, combined with 100% of SQL queries using prepared statements, indicates good coding practices in these critical areas. The presence of nonce checks is also a positive sign for input validation.
However, a significant concern arises from the complete lack of proper output escaping (0% escaped). This means that any data rendered to the user could potentially be vulnerable to cross-site scripting (XSS) attacks, depending on the nature of the plugin's output. The absence of capability checks is also noteworthy, as it suggests that plugin functionality might not be adequately protected against unauthorized access by lower-privileged users.
The plugin's vulnerability history shows zero known CVEs, which is an excellent track record. This lack of past vulnerabilities, coupled with the absence of critical taint flows, suggests that the plugin has historically been well-maintained and secure. Despite the strengths in attack surface reduction and SQL handling, the unescaped output represents a tangible risk that needs to be addressed to achieve a robust security profile.
Key Concerns
- Unescaped output
- Missing capability checks
DB Signatures Security Vulnerabilities
DB Signatures Release Timeline
DB Signatures Code Analysis
Output Escaping
DB Signatures Attack Surface
WordPress Hooks 9
Maintenance & Trust
DB Signatures Maintenance & Trust
Maintenance Signals
Community Trust
DB Signatures Alternatives
Head, Footer and Post Injections
header-footer
Head and Footer plugin lets you to add HTML code to the head and footer sections of your site pages, inside posts... and more!
AdPlugg WordPress Ad Plugin
adplugg
Advertising is easy with AdPlugg. The AdPlugg WordPress Ad Plugin and ad server allow you to easily manage, schedule, rotate and track your ads.
Ad Commander – Ad Manager for Banners, AdSense, Ad Networks
ad-commander
Insert image banner ads, Google AdSense, Amazon, affiliate ad networks. Rotate and randomize. Manage with AI agents. Track impressions and clicks.
PurpleAds Ad Network
purpleads
PurpleAds Wordpress Plugin
Ad Commander Tools
ad-commander-tools
Add-on for the Ad Commander plugin that allows you to import, export, and manage ad statistics. This plugin requires Ad Commander.
DB Signatures Developer Profile
3 plugins · 30 total installs
How We Detect DB Signatures
Patterns used to identify this plugin on WordPress sites during automated security audits and web crawling.
Asset Fingerprints
HTML / DOM Fingerprints
db_signatures_signature_db_signatures_signaturedb_signatures_signature_nonce_db_signatures_show_on