ChronoFlo Calendar ShortCode Security & Risk Analysis
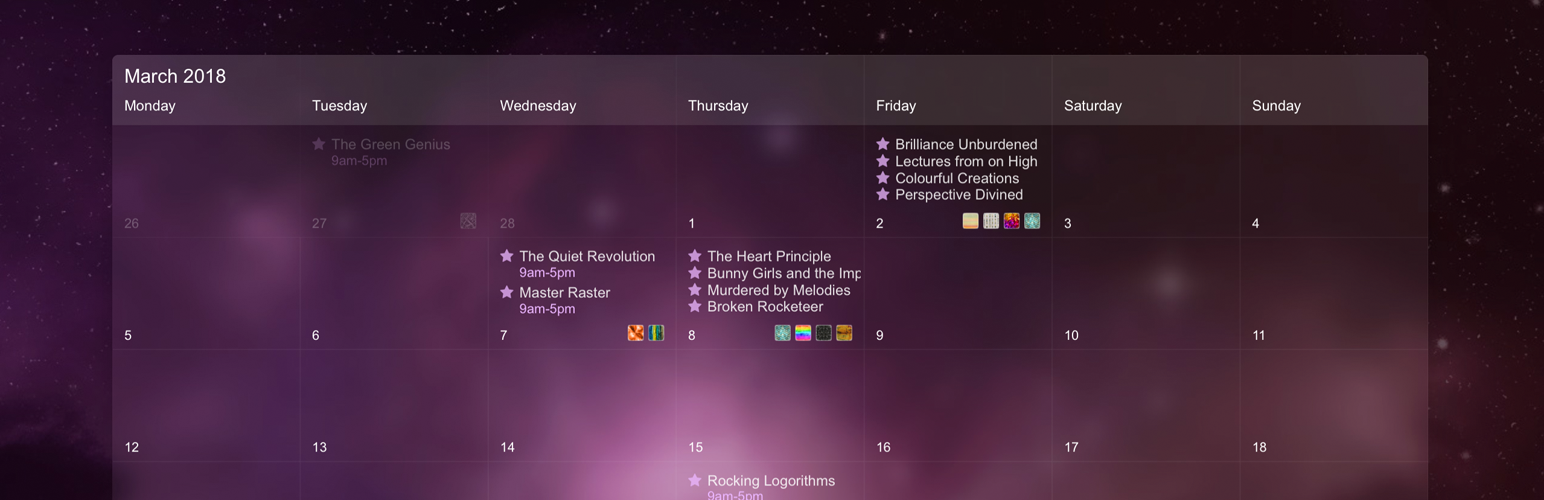
wordpress.org/plugins/chronoflo-calendar-shortcodeChronoFlo Calendar is a beautiful events calendar offering unrivalled visual customization. This plugin provides a shortcode to embed a ChronoFlo cale …
Is ChronoFlo Calendar ShortCode Safe to Use in 2026?
Generally Safe
Score 85/100ChronoFlo Calendar ShortCode has no known CVEs and is actively maintained. It's a solid choice for most WordPress installations.
The static analysis of chronoflo-calendar-shortcode v1.0 reveals a generally good security posture. The code adheres to several security best practices, including the absence of dangerous functions, all SQL queries utilizing prepared statements, and all output being properly escaped. Furthermore, there are no file operations or external HTTP requests, and no bundled libraries to potentially become outdated. The attack surface is minimal, consisting solely of one shortcode, and importantly, there are no unprotected entry points indicated in the static analysis.
However, a significant concern arises from the complete lack of nonce checks and capability checks. While the static analysis shows no unprotected AJAX or REST API routes, the absence of these fundamental security mechanisms for the shortcode is a notable weakness. This could potentially allow for unauthorized execution of the shortcode's functionality if an attacker can trick a logged-in user into triggering it. The taint analysis also shows no flows, which, while seemingly positive, could also indicate limited analysis or a very simple plugin where vulnerabilities might be harder to detect via this method.
With zero recorded vulnerabilities in its history, the plugin has a strong track record. This, combined with the good practices observed in the code, suggests a developer who is likely security-conscious. Nevertheless, the missing nonce and capability checks represent a potential vulnerability that could be exploited. The plugin's strengths lie in its clean code and lack of common pitfalls, but its primary weakness is the lack of authentication and authorization checks on its sole entry point.
Key Concerns
- Missing capability checks for shortcode
- Missing nonce checks for shortcode
ChronoFlo Calendar ShortCode Security Vulnerabilities
ChronoFlo Calendar ShortCode Release Timeline
ChronoFlo Calendar ShortCode Code Analysis
ChronoFlo Calendar ShortCode Attack Surface
Shortcodes 1
WordPress Hooks 1
Maintenance & Trust
ChronoFlo Calendar ShortCode Maintenance & Trust
Maintenance Signals
Community Trust
ChronoFlo Calendar ShortCode Alternatives
WP FullCalendar
wp-fullcalendar
Uses the FullCalendar library to create a stunning calendar view of events, posts and other custom post types
BeatGig WordPress Plugin
beatgig-calendar-embed
BeatGig's event calendar is a modern, beautiful calendar that embeds directly onto your website. When you book new shows on BeatGig, your website …
Timetable and Event Schedule by MotoPress
mp-timetable
Smart event organizer and time-management tool with a clean minimalist design for featuring your timetables and upcoming events.
Event Organiser
event-organiser
Create and maintain events, including complex reoccurring patterns, venue management (with Google Maps or OpenStreetMap), calendars and customisable e …
The Events Calendar Shortcode & Block
the-events-calendar-shortcode
Add shortcode, block, Elementor and Bricks functionality to The Events Calendar Plugin, so you can easily list and promote your events anywhere.
ChronoFlo Calendar ShortCode Developer Profile
1 plugin · 30 total installs
How We Detect ChronoFlo Calendar ShortCode
Patterns used to identify this plugin on WordPress sites during automated security audits and web crawling.