ChordChartWP Security & Risk Analysis
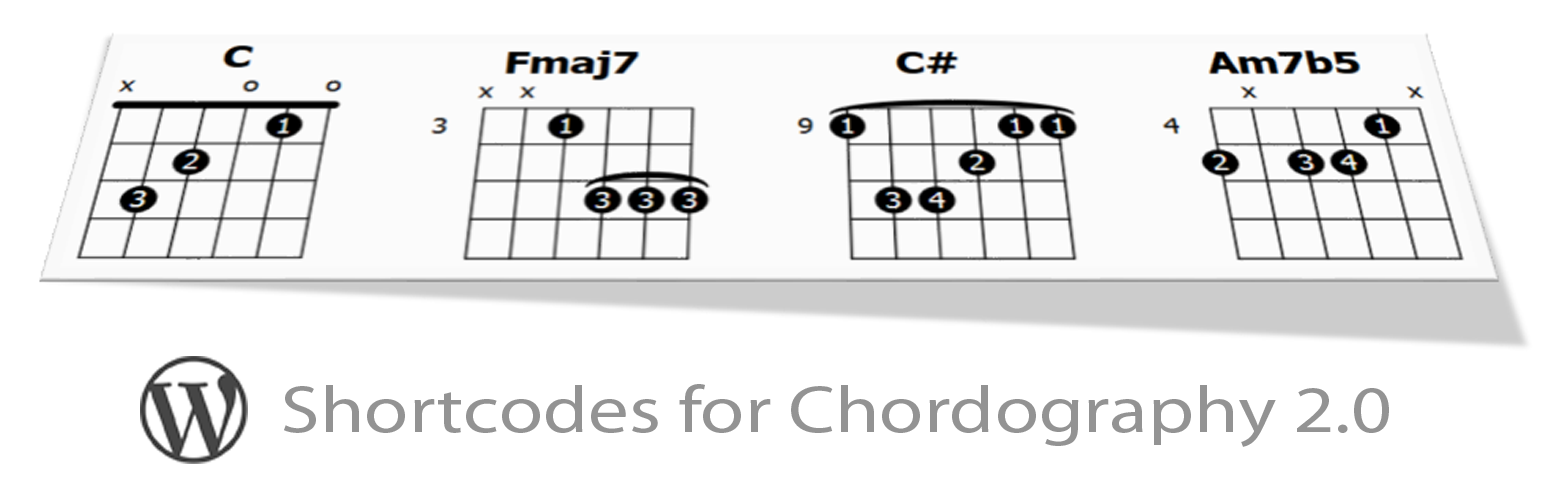
wordpress.org/plugins/chordchartwpUsers write shortcodes of text tab notation which will be then be parsed and rendered as svg chord chart images.
Is ChordChartWP Safe to Use in 2026?
Generally Safe
Score 85/100ChordChartWP has no known CVEs and is actively maintained. It's a solid choice for most WordPress installations.
The plugin "chordchartwp" version 1.0 exhibits a generally strong security posture based on the provided static analysis. There are no identified dangerous functions, SQL queries are exclusively executed with prepared statements, and all output appears to be properly escaped. Furthermore, the absence of file operations, external HTTP requests, and a complete lack of recorded vulnerabilities in its history are positive indicators. The plugin also demonstrates good practice by not bundling external libraries, reducing the risk of inheriting vulnerabilities from outdated components.
However, a significant concern arises from the complete absence of nonce checks and capability checks. While the plugin has a very small attack surface consisting of a single shortcode and no unprotected entry points detected in this specific analysis, the lack of these fundamental security mechanisms means that if any functionality is ever exposed or modified, it could be vulnerable to CSRF or privilege escalation attacks. The analysis also indicates zero flows were analyzed for taint, which is a limitation, but in the absence of known vulnerabilities, this might be acceptable for a simple plugin. The critical weakness lies in the absence of these essential security checks, which could become a problem if the plugin's functionality expands or is inadvertently exposed.
In conclusion, "chordchartwp" v1.0 currently appears to be a safe plugin due to its simplicity and lack of known vulnerabilities. Its adherence to secure coding practices like prepared statements and output escaping is commendable. The primary weakness is the complete omission of nonce and capability checks, which represents a foundational security oversight. While not immediately exploitable given the current limited attack surface, this omission leaves the plugin susceptible to common web vulnerabilities should its functionality change or be expanded in the future.
Key Concerns
- Missing nonce checks
- Missing capability checks
ChordChartWP Security Vulnerabilities
ChordChartWP Release Timeline
ChordChartWP Code Analysis
ChordChartWP Attack Surface
Shortcodes 1
WordPress Hooks 1
Maintenance & Trust
ChordChartWP Maintenance & Trust
Maintenance Signals
Community Trust
ChordChartWP Alternatives
ChordChartWP Developer Profile
1 plugin · 10 total installs
How We Detect ChordChartWP
Patterns used to identify this plugin on WordPress sites during automated security audits and web crawling.
Asset Fingerprints
/wp-content/plugins/chordchartwp/js/chart.data.js/wp-content/plugins/chordchartwp/js/chart.js/wp-content/plugins/chordchartwp/js/chart.data.js/wp-content/plugins/chordchartwp/js/chart.jsHTML / DOM Fingerprints
diagramdata-chordography-configchordography<div class="diagram"><div id="