Change WP Cron Request URL Security & Risk Analysis
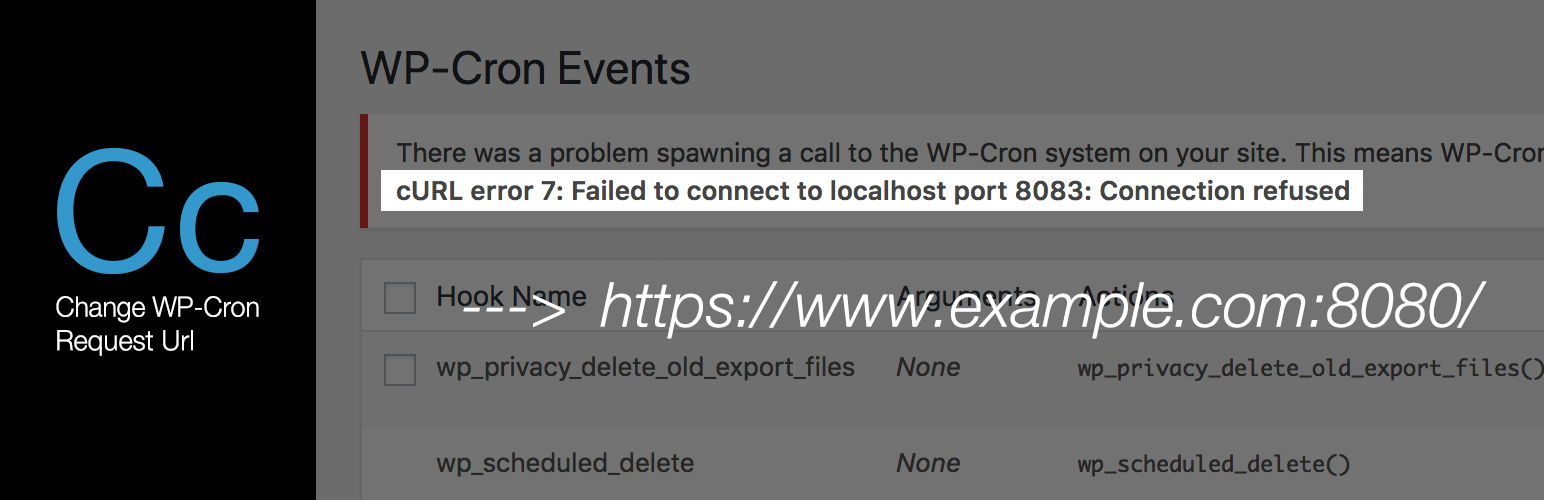
wordpress.org/plugins/change-wp-cron-request-urlThis plugin changes the request url when wp-cron executed.
Is Change WP Cron Request URL Safe to Use in 2026?
Generally Safe
Score 100/100Change WP Cron Request URL has no known CVEs and is actively maintained. It's a solid choice for most WordPress installations.
The 'change-wp-cron-request-url' plugin, version 1.0.2, exhibits a strong static security posture with no identified entry points, dangerous functions, or file operations. The plugin exclusively uses prepared statements for its SQL queries, which is a significant positive security practice. However, a major concern arises from the complete lack of output escaping, meaning that all 12 identified output operations are potentially vulnerable to cross-site scripting (XSS) attacks. This oversight can be exploited if any dynamic data is displayed to users without proper sanitization.
The plugin also shows no evidence of nonce or capability checks, which are crucial for protecting against various types of attacks, including cross-site request forgery (CSRF) and unauthorized privilege escalation. The absence of a vulnerability history suggests a lack of publicly disclosed security issues, which is positive. However, given the significant gaps in output escaping and authorization checks, this could also indicate a lack of thorough security auditing. In conclusion, while the plugin avoids common pitfalls like SQL injection and insecure file handling, the unescaped output and missing authorization controls represent significant security risks that need immediate attention.
Key Concerns
- 0% of outputs are properly escaped
- No nonce checks implemented
- No capability checks implemented
Change WP Cron Request URL Security Vulnerabilities
Change WP Cron Request URL Release Timeline
Change WP Cron Request URL Code Analysis
Output Escaping
Change WP Cron Request URL Attack Surface
WordPress Hooks 4
Maintenance & Trust
Change WP Cron Request URL Maintenance & Trust
Maintenance Signals
Community Trust
Change WP Cron Request URL Alternatives
WP Crontrol
wp-crontrol
WP Crontrol enables you to take control of the cron events on your WordPress website.
Cron Jobs
leira-cron-jobs
Easily manage and monitor your WordPress cron jobs from a clean, intuitive interface.
Cron Logger
cron-logger
Logs wp-cron.php runs.
WP-Cron Control
wp-cron-control
This plugin allows you to take control over the execution of cron jobs.
WP Cron HTTP Auth
wp-cron-http-auth
Enables WP Cron on sites using HTTP Authentication.
Change WP Cron Request URL Developer Profile
24 plugins · 130 total installs
How We Detect Change WP Cron Request URL
Patterns used to identify this plugin on WordPress sites during automated security audits and web crawling.