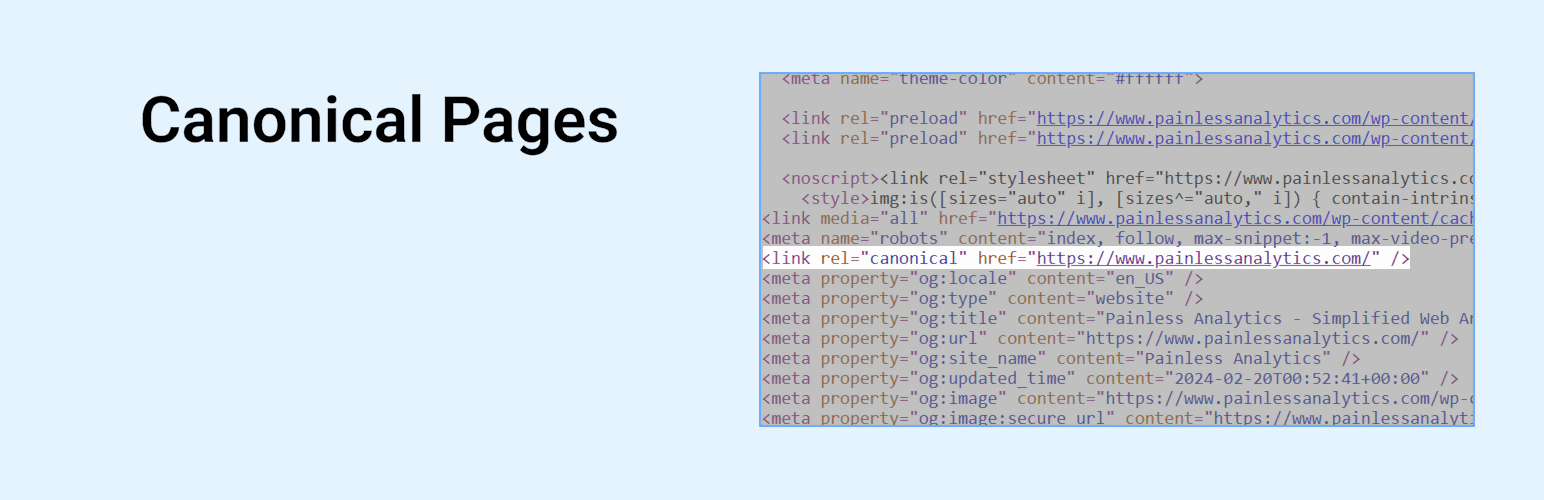
Canonical Pages Security & Risk Analysis
wordpress.org/plugins/canonical-pagesQuickly add the canonical meta tag and customize the url.
Is Canonical Pages Safe to Use in 2026?
Generally Safe
Score 100/100Canonical Pages has no known CVEs and is actively maintained. It's a solid choice for most WordPress installations.
The "canonical-pages" plugin v1.0.1 exhibits a strong security posture based on the provided static analysis. There are no identified entry points such as AJAX handlers, REST API routes, shortcodes, or cron events that could be directly exploited. The code adheres to secure development practices by utilizing prepared statements for all SQL queries and properly escaping all output. The absence of dangerous functions, file operations, and external HTTP requests further strengthens its security profile. The plugin also demonstrates a good understanding of WordPress security by including capability checks, although it's noted that there are no nonce checks. The vulnerability history is completely clean, with no recorded CVEs, which is a significant positive indicator of the plugin's long-term security maintenance. This suggests that the plugin authors have a strong commitment to security and have likely addressed any potential issues proactively. The plugin's greatest weakness lies in its zero-value attack surface, which while seemingly positive, might also indicate a lack of functionality that exposes it to potential attack vectors or a very narrow scope of operation. The absence of nonce checks, while not explicitly leading to a critical issue in this specific analysis, represents a missed opportunity for enhancing security on any potential future AJAX or similar interactions, however unlikely given the current attack surface.
Key Concerns
- No nonce checks present
Canonical Pages Security Vulnerabilities
Canonical Pages Release Timeline
Canonical Pages Code Analysis
Output Escaping
Canonical Pages Attack Surface
WordPress Hooks 8
Maintenance & Trust
Canonical Pages Maintenance & Trust
Maintenance Signals
Community Trust
Canonical Pages Alternatives
Canonical Link
canonical-link
Adds the canonical link to your site (https://wikipedia.org/wiki/Canonical_link_element). Activate and then set your permalinks to "Post name&quo …
Rapid Canonical URLs
rapid-canonical-urls
Reduce 301 redirects and HTTP requests by using HTML5’s history API to show visitors the correct, canonical URL.
Make Paths Relative
make-paths-relative
Convert Absolute URLs to be relative in your fingertip.
Advance Canonical URL
advance-canonical-url
Advanced Canonical URL is a powerful WordPress plugin designed to enhance your website’s SEO by preventing duplicate content issues.
Canonical SEO
canonical-seo
Plugin adds posibility to edit canonical URL and meta description
Canonical Pages Developer Profile
3 plugins · 90 total installs
How We Detect Canonical Pages
Patterns used to identify this plugin on WordPress sites during automated security audits and web crawling.
Asset Fingerprints
/wp-content/plugins/canonical-pages/canonical-pages.class.php/wp-content/plugins/canonical-pages/admin/canonical-pages-admin.class.php/wp-content/plugins/canonical-pages/admin/edit.min.jscanonical-pages/style.css?ver=canonical-pages/admin/edit.min.js?ver=HTML / DOM Fingerprints
data-canonical-pagescanonicalPages/wp-json/canonical-pages/v1/settings