C9 Variables Security & Risk Analysis
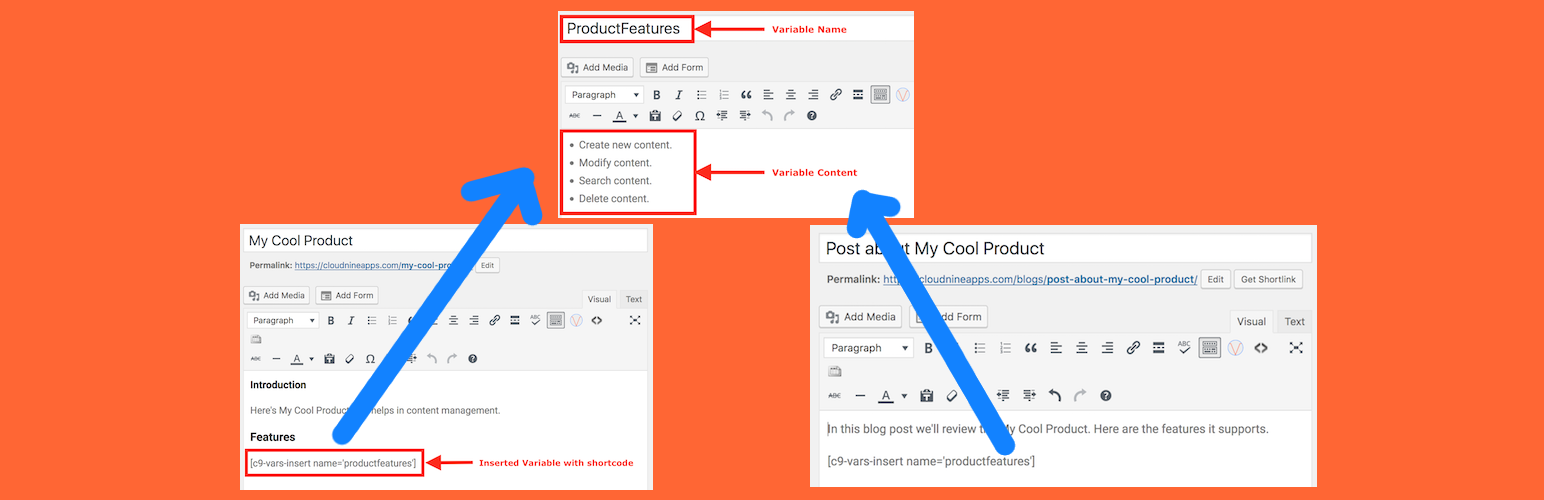
wordpress.org/plugins/c9-variablesUse variables to make smart reusable content. The basic plugin is fully functional and supports up to 10 variables. The Pro plugin supports unlimited …
Is C9 Variables Safe to Use in 2026?
Generally Safe
Score 85/100C9 Variables has no known CVEs and is actively maintained. It's a solid choice for most WordPress installations.
The c9-variables plugin v1.0.0 exhibits a concerning security posture primarily due to its unprotected AJAX handlers. While the plugin demonstrates good practices like using prepared statements for SQL queries and a history free of known vulnerabilities, the presence of four AJAX handlers without authentication checks represents a significant attack vector. This means any user, including unauthenticated ones, could potentially trigger these handlers, leading to unintended actions or information disclosure. The taint analysis reveals one flow with unsanitized paths, though it is not classified as critical or high, it still warrants attention as it indicates a potential for deeper issues if not addressed. The limited output escaping is also a weakness, potentially opening the door to cross-site scripting (XSS) vulnerabilities if user-supplied data is not properly handled before being displayed.
Key Concerns
- AJAX handlers without authentication checks
- Flows with unsanitized paths (taint analysis)
- Low percentage of properly escaped output
C9 Variables Security Vulnerabilities
C9 Variables Release Timeline
C9 Variables Code Analysis
Output Escaping
Data Flow Analysis
C9 Variables Attack Surface
AJAX Handlers 4
WordPress Hooks 16
Maintenance & Trust
C9 Variables Maintenance & Trust
Maintenance Signals
Community Trust
C9 Variables Alternatives
Post Lock
post-lock
Post Lock prevents accidental updating or publishing of content by requiring a password to do either.
Admin Calculator Widget
admin-calculator-widget
A simple floating calculator for WordPress admin dashboard to perform quick calculations while working.
Pimi Admin Agent
pimi-admin-agent
Manage your WordPress site using simple commands. Create pages, posts, users, manage plugins, and more with commands.
ST Admin Notes
st-admin-notes
A lightweight draggable admin notes plugin that lets you create sticky notes directly in the WordPress admin area.
Zen Smart Folders
zen-smart-folders
Organize your WordPress Pages & Posts into folders for better management.
C9 Variables Developer Profile
1 plugin · 0 total installs
How We Detect C9 Variables
Patterns used to identify this plugin on WordPress sites during automated security audits and web crawling.
Asset Fingerprints
/wp-content/plugins/c9-variables/admin/css/common/c9-common.css/wp-content/plugins/c9-variables/admin/css/c9-variables-admin.css/wp-content/plugins/c9-variables/admin/js/c9-variables-admin.js/wp-content/plugins/c9-variables/admin/js/c9-variables-admin.jsc9-variables-admin/css/common/c9-common.css?ver=c9-variables-admin/css/c9-variables-admin.css?ver=c9-variables-admin/js/c9-variables-admin.js?ver=HTML / DOM Fingerprints
window.C9_Variables_Constants