BookServe Online Booking Calendar Security & Risk Analysis
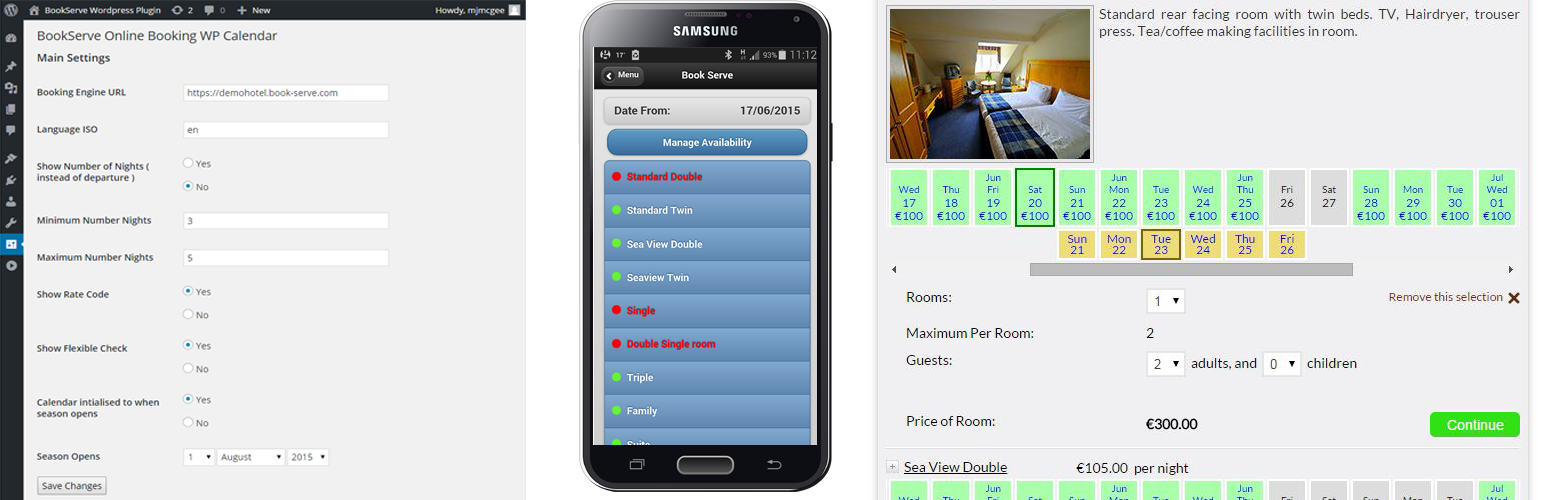
wordpress.org/plugins/book-serve-reservationsMakes a calendar and booking form widget to take the user to the Book Serve Hotel Booking Engine.
Is BookServe Online Booking Calendar Safe to Use in 2026?
Generally Safe
Score 85/100BookServe Online Booking Calendar has no known CVEs and is actively maintained. It's a solid choice for most WordPress installations.
The book-serve-reservations v3.2RC plugin presents a mixed security posture. On the positive side, there are no known CVEs, and the plugin appears to have a limited attack surface with no exposed AJAX handlers, REST API routes, or shortcodes without apparent authentication. All SQL queries are also using prepared statements, which is a strong indicator of good practice in database interaction. However, significant concerns arise from the static analysis of the code itself. A critical finding is that 100% of output is not properly escaped, creating a high risk of Cross-Site Scripting (XSS) vulnerabilities. Furthermore, the taint analysis revealed a flow with an unsanitized path, suggesting a potential for directory traversal or other file system manipulation vulnerabilities, even if no critical or high severity issues were flagged in the taint analysis itself. The single file operation also warrants attention given the lack of sanitization in the taint analysis.
Key Concerns
- 100% of output is not properly escaped
- Taint analysis shows unsanitized path flow
- File operation present without clear sanitization context
- No nonce checks on potential entry points
- No capability checks on potential entry points
BookServe Online Booking Calendar Security Vulnerabilities
BookServe Online Booking Calendar Release Timeline
BookServe Online Booking Calendar Code Analysis
Output Escaping
Data Flow Analysis
BookServe Online Booking Calendar Attack Surface
WordPress Hooks 4
Maintenance & Trust
BookServe Online Booking Calendar Maintenance & Trust
Maintenance Signals
Community Trust
BookServe Online Booking Calendar Alternatives
eZee Online Hotel Booking Engine
online-booking-engine
eZee Reservation plugin is solutions for hotel, resorts, B&B, hotel chains, to get commission free online bookings from their own hotel website.
WP Booking System – Booking Calendar
wp-booking-system
The booking calendar plugin for WordPress. Get easy online booking with this lightweight and powerful booking calendar.
WP Simple Booking Calendar
wp-simple-booking-calendar
This booking calendar shows when something is booked or available. Use it to show when your holiday home is available for rent, for example.
Pinpoint Booking System – Version 2
booking-system
Book anything, anytime, anywhere.
Booking System Trafft
booking-system-trafft
Trafft is a next-level booking system offering limitless opportunities for scheduling appointments and managing your calendar & all of your bookings.
BookServe Online Booking Calendar Developer Profile
1 plugin · 10 total installs
How We Detect BookServe Online Booking Calendar
Patterns used to identify this plugin on WordPress sites during automated security audits and web crawling.
Asset Fingerprints
/wp-content/plugins/book-serve-reservations/book_serve_booking_form/booking_form.css/wp-content/plugins/book-serve-reservations/book_serve_booking_form/booking_form.js/wp-content/plugins/book-serve-reservations/book_serve_booking_form/booking_form.jsHTML / DOM Fingerprints
vmbfWordpressWidgetvmbf_plugin_options