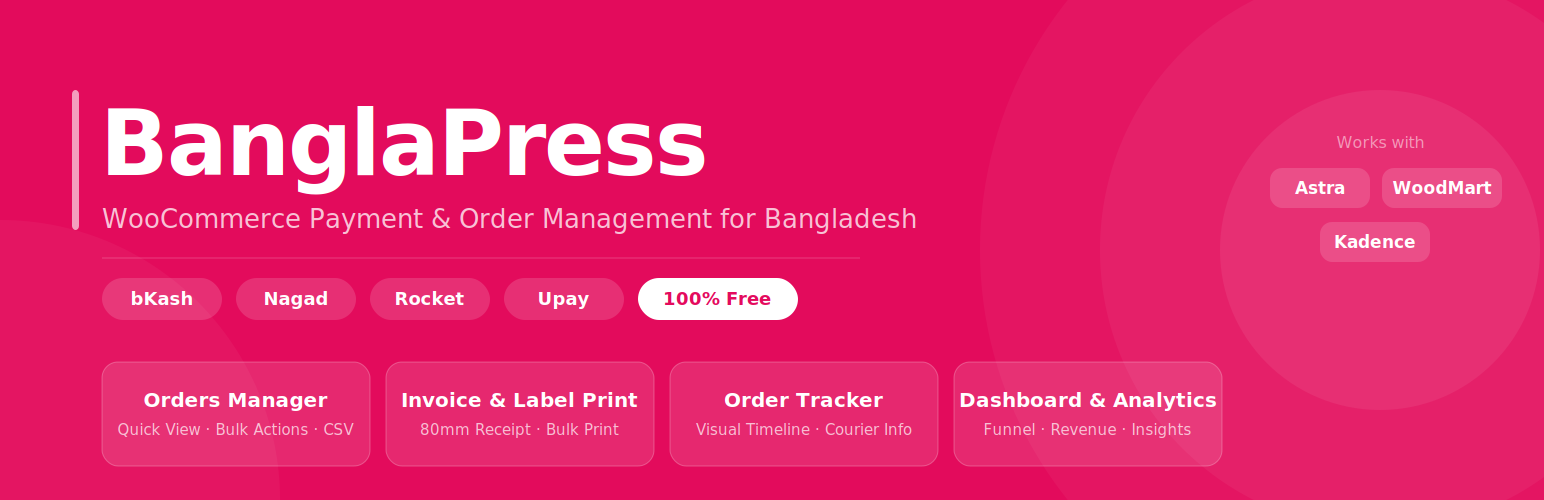
BanglaPress – bKash, & Mobile Payment with Order Tracking & Invoice & Shipping Label Printing for WooCommerce Security & Risk Analysis
wordpress.org/plugins/bangla-pressbKash, Nagad, Rocket & Upay for WooCommerce — Label Print, Invoice, Order Tracker, Orders Manager.
Is BanglaPress – bKash, & Mobile Payment with Order Tracking & Invoice & Shipping Label Printing for WooCommerce Safe to Use in 2026?
Generally Safe
Score 100/100BanglaPress – bKash, & Mobile Payment with Order Tracking & Invoice & Shipping Label Printing for WooCommerce has no known CVEs and is actively maintained. It's a solid choice for most WordPress installations.
The Bangla Press plugin v1.2 exhibits a mixed security posture. On the positive side, it demonstrates strong practices in avoiding dangerous functions, executing all SQL queries using prepared statements, and performing a high percentage of output escaping. It also has no recorded vulnerabilities in its history, suggesting a general awareness of security or a lack of past exploitation. However, significant concerns arise from its attack surface. Two AJAX handlers are present without authentication checks, representing a direct pathway for potential unauthorized actions. The taint analysis also indicates one flow with an unsanitized path, which could lead to exploitable vulnerabilities if not handled carefully, though it's not categorized as critical or high severity.
While the absence of known CVEs is a positive sign, the presence of unprotected entry points in the code analysis, specifically the AJAX handlers, remains a notable weakness. The taint flow with an unsanitized path, even if not critical, warrants attention as it suggests a potential for input validation issues. The plugin's strengths lie in its secure database interactions and output handling, but the critical need for robust authentication and input sanitization on its AJAX endpoints cannot be overlooked.
Key Concerns
- Unprotected AJAX handlers
- Taint flow with unsanitized path
BanglaPress – bKash, & Mobile Payment with Order Tracking & Invoice & Shipping Label Printing for WooCommerce Security Vulnerabilities
BanglaPress – bKash, & Mobile Payment with Order Tracking & Invoice & Shipping Label Printing for WooCommerce Release Timeline
BanglaPress – bKash, & Mobile Payment with Order Tracking & Invoice & Shipping Label Printing for WooCommerce Code Analysis
Output Escaping
Data Flow Analysis
BanglaPress – bKash, & Mobile Payment with Order Tracking & Invoice & Shipping Label Printing for WooCommerce Attack Surface
AJAX Handlers 2
Shortcodes 1
WordPress Hooks 17
Maintenance & Trust
BanglaPress – bKash, & Mobile Payment with Order Tracking & Invoice & Shipping Label Printing for WooCommerce Maintenance & Trust
Maintenance Signals
Community Trust
BanglaPress – bKash, & Mobile Payment with Order Tracking & Invoice & Shipping Label Printing for WooCommerce Alternatives
Flying Pay
flying-pay-gateway
A seamless and secure payment gateway integration for WooCommerce featuring Mobile Banking, 4 Major Banks, and Crypto support with an interactive UI.
Deshi Pay bKash, Rocket, Nagad
deshi-pay
A professional and modern manual payment gateway for WooCommerce supporting bKash, Nagad, and Rocket with a sleek UI and easy copy features.
SoftTech-IT bKash, Rocket, Nagad
bkash
Easy to use bKash , Rocket and Nagad Payment Gateway for Woocommerce
Bangladeshi Payments Mobile – QR Code & Transaction Reports
bangladeshi-payments-mobile
Accept Mobile Payments in Bangladesh – WooCommerce Gateway for bKash, Nagad, Rocket & Upay with QR Code & Transaction Reports.
UddoktaPay
uddoktapay-gateway
UddoktaPay Plugin for WooCommerce.
BanglaPress – bKash, & Mobile Payment with Order Tracking & Invoice & Shipping Label Printing for WooCommerce Developer Profile
9 plugins · 540 total installs
How We Detect BanglaPress – bKash, & Mobile Payment with Order Tracking & Invoice & Shipping Label Printing for WooCommerce
Patterns used to identify this plugin on WordPress sites during automated security audits and web crawling.
Asset Fingerprints
/wp-content/plugins/bangla-press/assets/bkash-admin-style.css/wp-content/plugins/bangla-press/assets/js/admin-scripts.js/wp-content/plugins/bangla-press/assets/bkash-style.css/wp-content/plugins/bangla-press/assets/mobile-banking.css/wp-content/plugins/bangla-press/assets/js/admin-scripts.jsbangla-press/assets/bkash-style.css?ver=bangla-press/assets/js/admin-scripts.js?ver=HTML / DOM Fingerprints
bkash-payment-buttonbkash-modalbkash-modal-contentclose-modalbkash-error-messagebkash-success-messagebkash-processing-messagedata-product-iddata-product-pricedata-min-attributesdata-bkash-iddata-bkash-amountdata-bkash-product-idbkash_payment_globalbkash_noncebkash_ajax_url/wp-json/bangla-press/v1/process-payment<div class="error">Please set a product ID!</div><button class="bkash-payment-button"