Attrace Security & Risk Analysis
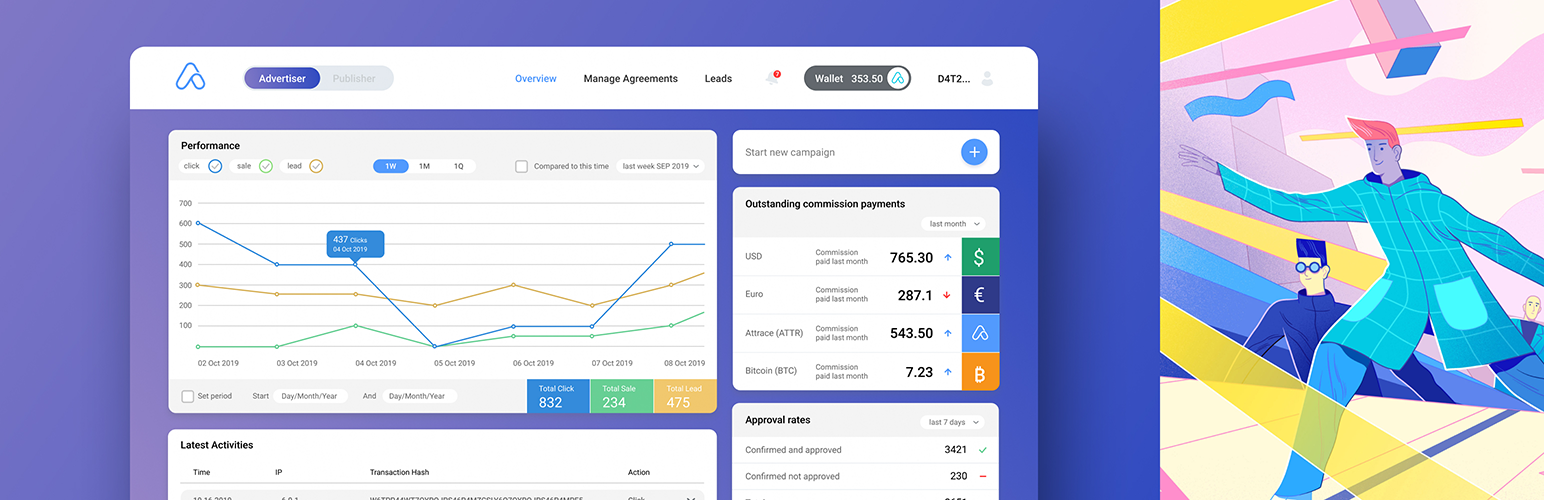
wordpress.org/plugins/attraceCustom made dedicated blockchain capable of registering and auditing any advertisement click on chain (sale or no-sale). This concept enables anybody …
Is Attrace Safe to Use in 2026?
Generally Safe
Score 85/100Attrace has no known CVEs and is actively maintained. It's a solid choice for most WordPress installations.
The attrace plugin v2.0.21 presents a generally positive security posture based on the provided static analysis. The absence of known CVEs and a clean vulnerability history are strong indicators of a well-maintained and secure plugin. The code analysis shows a good adoption of prepared statements for SQL queries and a reasonable rate of output escaping, suggesting developers are mindful of common web vulnerabilities. The limited attack surface, consisting solely of shortcodes, is also a positive sign, especially with no immediately obvious unprotected entry points.
However, there are areas for improvement. The complete lack of nonce checks is a significant concern, particularly as it applies to potentially sensitive operations that might be triggered via shortcodes, even if no AJAX or REST API endpoints are directly exposed without authentication. While the taint analysis found no critical or high-severity issues, this doesn't fully negate the risk associated with missing nonces, as they are a fundamental layer of defense against CSRF attacks. The limited capability checks also suggest a potential for privilege escalation if an attacker can manipulate shortcode behavior.
In conclusion, attrace v2.0.21 appears to be a relatively secure plugin, largely due to its clean vulnerability history and proactive use of prepared statements. The primary weakness lies in the absence of nonce checks, which introduces a notable risk for Cross-Site Request Forgery (CSRF) attacks, and the limited number of capability checks. Addressing these specific points would significantly strengthen the plugin's overall security.
Key Concerns
- Missing nonce checks on entry points
- Insufficient capability checks for entry points
- Less than 70% of output escaping is proper
Attrace Security Vulnerabilities
Attrace Release Timeline
Attrace Code Analysis
SQL Query Safety
Output Escaping
Attrace Attack Surface
Shortcodes 4
WordPress Hooks 16
Maintenance & Trust
Attrace Maintenance & Trust
Maintenance Signals
Community Trust
Attrace Alternatives
PrettyLinks – Affiliate Links, Link Branding, Link Tracking, Marketing and Stripe Payments Plugin
pretty-link
🌠 The best WordPress link management, branding, tracking, sharing and payments plugin. Easily make pretty & trackable shortlinks. 🔗
ThirstyAffiliates – Affiliate Links, Link Branding, Link Tracking & Marketing Plugin
thirstyaffiliates
🔗 Affiliate link management & cloaker tool. Easily manage, shrink and track your affiliate links in WordPress. 🔥
Affiliate Sales in Google Analytics and other tools
wecantrack
Integrate all your affiliate sales in Google Analytics, Google Ads, Facebook, Data Studio and more!
AffiliateWP – Affiliate Info
affiliatewp-affiliate-info
Display information based on the affiliate's referral URL.
Sovrn
viglink
Maximize your affiliate revenue with Sovrn Commerce - link optimization, price comparisons, and unified reporting.
Attrace Developer Profile
1 plugin · 10 total installs
How We Detect Attrace
Patterns used to identify this plugin on WordPress sites during automated security audits and web crawling.
Asset Fingerprints
/wp-content/plugins/attrace/app/lib/attrace-connector-php/src/connector.js/wp-content/plugins/attrace/app/lib/attrace-connector-php/src/connector.jsattrace/style.css?ver=attrace/script.js?ver=HTML / DOM Fingerprints
attrace-admin-wrappername="attrace-site-verification"attrace_data<a href="/<a href="/<a href="/<a href="/