Alister Security & Risk Analysis
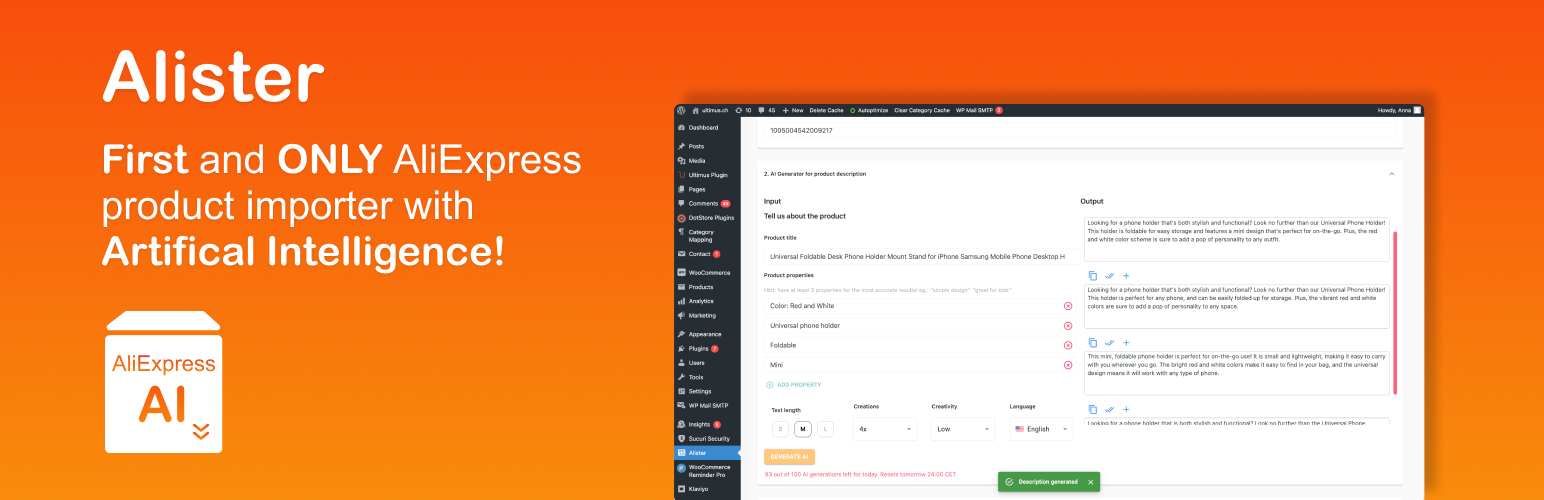
wordpress.org/plugins/alisterA tool that helps woocommerce based stores import aliexpress products.
Is Alister Safe to Use in 2026?
Generally Safe
Score 85/100Alister has no known CVEs and is actively maintained. It's a solid choice for most WordPress installations.
The "alister" plugin version 0.9.2 exhibits a significantly concerning security posture primarily due to its vast unprotected attack surface. With 25 AJAX handlers, all lacking authentication checks, the plugin presents a wide entry point for potential attackers. The presence of the `unserialize` function, a known vulnerability vector when handling untrusted input, further exacerbates this risk. While taint analysis did not reveal critical or high severity issues, the fact that all analyzed flows had unsanitized paths is a red flag, suggesting potential for future exploitation if input validation is not rigorously applied. The plugin's history of zero known CVEs is a positive indicator, but it cannot compensate for the evident weaknesses in its current implementation, especially the lack of nonces and limited capability checks.
Key Concerns
- 25 unprotected AJAX handlers
- Use of unserialize function
- 0 Nonce checks for AJAX
- SQL queries not always prepared
- Output not always escaped
- Limited capability checks (2)
- All taint flows have unsanitized paths
Alister Security Vulnerabilities
Alister Release Timeline
Alister Code Analysis
Dangerous Functions Found
SQL Query Safety
Output Escaping
Data Flow Analysis
Alister Attack Surface
AJAX Handlers 25
WordPress Hooks 8
Maintenance & Trust
Alister Maintenance & Trust
Maintenance Signals
Community Trust
Alister Alternatives
ALD – Dropshipping and Fulfillment for AliExpress and WooCommerce
woo-alidropship
Transfer data from AliExpress products to WooCommerce effortlessly and fulfill WooCommerce orders to AliExpress automatically.
AliExpress Dropshipping Plugin for WooCommerce & WordPress
ali2woo-lite
Use the WooCommerce Dropshipping Plugin for AliExpress to import products, reviews, set flexible pricing rules, and automate order fulfillment.
Importify – AI Dropshipping for WooCommerce
importify
Importify is a dropshipping app that allows you to find products from a variety of wholesalers, add them to your WooCommerce store, and sell them onli …
EPROLO-Dropshipping
eprolo-dropshipping
EPROLO dropshipping allows to import products from Aliexpress or EPROLO to wordpress, woocommerce in one click.
Sharkdropship & affiliate for AliExpress
wooshark-aliexpress-importer
Transform your WooCommerce store into a profitable AliExpress dropshipping or affiliate business with ease!
Alister Developer Profile
1 plugin · 20 total installs
How We Detect Alister
Patterns used to identify this plugin on WordPress sites during automated security audits and web crawling.
Asset Fingerprints
/wp-content/plugins/alister/app/build/index.css/wp-content/plugins/alister/app/build/index.js/wp-content/plugins/alister/app/build/index.jsalister-stylealister-scriptHTML / DOM Fingerprints
options_groupid="alisterApp"alisterData/wp-json/alister-elephantfishing/v1/add-product/wp-json/alister-elephantfishing/v1/get-product-data/wp-json/alister-elephantfishing/v1/get-existing-product/wp-json/alister-elephantfishing/v1/get-description/wp-json/alister-elephantfishing/v1/get-product-categories/wp-json/alister-elephantfishing/v1/get-product-tags/wp-json/alister-elephantfishing/v1/update-product-price/wp-json/alister-elephantfishing/v1/get-remaining-requests