AIRize: Content summarize with AI Security & Risk Analysis
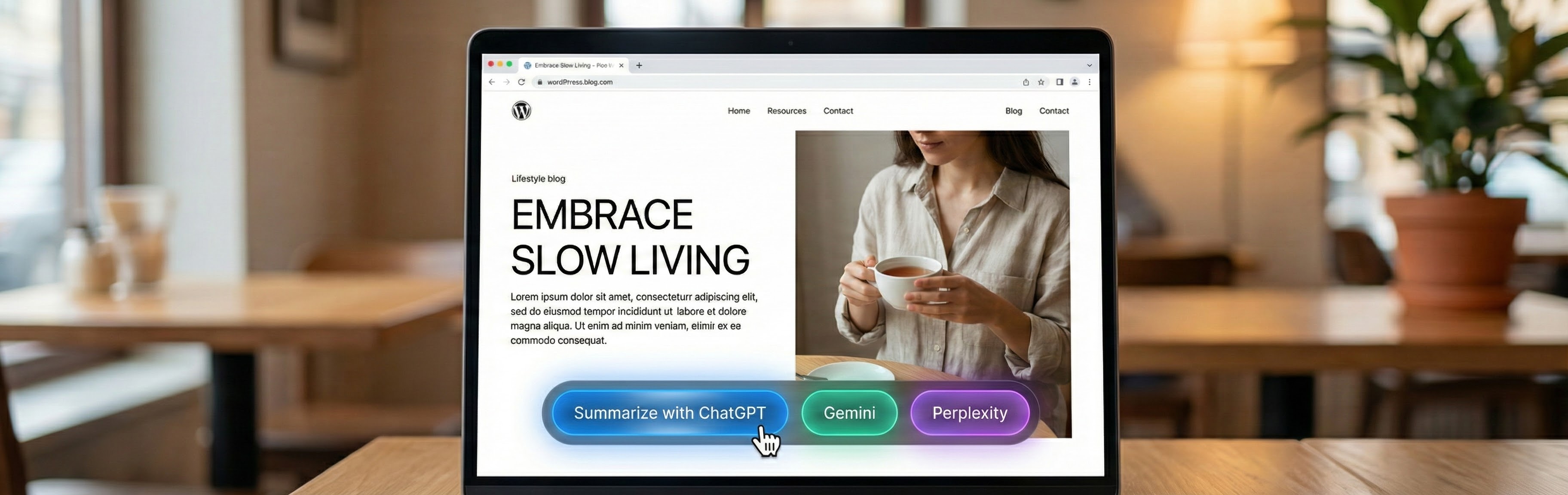
wordpress.org/plugins/airizeAdds AI summary buttons that open ChatGPT, Gemini, Perplexity, or Grok to summarize the current page.
Is AIRize: Content summarize with AI Safe to Use in 2026?
Generally Safe
Score 100/100AIRize: Content summarize with AI has no known CVEs and is actively maintained. It's a solid choice for most WordPress installations.
The "airize" v1.0.0 plugin exhibits a generally good security posture, with no known vulnerabilities in its history and strong adherence to secure coding practices. The static analysis reveals a minimal attack surface, with only one AJAX handler and no shortcodes, cron events, or REST API routes. Crucially, this single AJAX handler, along with two other points in the code, includes capability checks, and a nonce check is present. SQL queries are all prepared, and there are no file operations or external HTTP requests, which significantly reduces risk.
However, a minor concern arises from the output escaping. While 70% of the 71 outputs are properly escaped, this means that approximately 21 output points might be vulnerable to cross-site scripting (XSS) if they handle user-supplied data without further sanitization. The taint analysis, showing zero flows with unsanitized paths, is positive but doesn't negate the potential risk from unescaped output, as taint analysis might not cover all possible injection vectors for XSS.
Overall, the plugin demonstrates a commitment to security by implementing capability and nonce checks, avoiding dangerous functions, and using prepared statements. The absence of any historical vulnerabilities further reinforces this. The primary area for improvement lies in ensuring 100% of output is properly escaped to mitigate potential XSS vulnerabilities.
Key Concerns
- Unescaped output detected
AIRize: Content summarize with AI Security Vulnerabilities
AIRize: Content summarize with AI Release Timeline
AIRize: Content summarize with AI Code Analysis
Output Escaping
AIRize: Content summarize with AI Attack Surface
AJAX Handlers 1
WordPress Hooks 5
Maintenance & Trust
AIRize: Content summarize with AI Maintenance & Trust
Maintenance Signals
Community Trust
AIRize: Content summarize with AI Alternatives
Blog AI summarize
blog-ai-summarize
Add AI summarization links block to single posts with customizable options.
ultraDevs AI Summarizer Block
ultradevs-ai-summarizer-block
Gutenberg block to summarize your post content using various AI platforms like ChatGPT, Gemini, Claude, Perplexity, and Grok.
AI Bud – AI Content Generator, AI Chatbot, ChatGPT, Gemini, GPT-4o
aibuddy-openai-chatgpt
AI Bud an AI Content & Image Generation, AI ChatBot, ChatGPT, OpenAI, Perplexity, Gemini, GPT-4o, LLAMA, Mistral
AI Share & Summarize
ai-share-summarize
Share on social media and generate summaries with citations from leading AIs (Claude, ChatGPT, Gemini, Grok, Perplexity, DeepSeek, Copilot, Qwen)
AxiaChat AI – Free AI Chatbot (Answers Customers Automatically)
axiachat-ai
The best AI Chatbot for WordPress. Like having ChatGPT trained on your content — turn your site into a 24/7 sales & support machine.
AIRize: Content summarize with AI Developer Profile
4 plugins · 2K total installs
How We Detect AIRize: Content summarize with AI
Patterns used to identify this plugin on WordPress sites during automated security audits and web crawling.
Asset Fingerprints
/wp-content/plugins/airize/assets/style.css/wp-content/plugins/airize/assets/admin.js/wp-content/plugins/airize/assets/admin.jsairize-style?ver=airize-admin?ver=HTML / DOM Fingerprints
airize-button-containerairize-buttonairize-settings-sectionairize-provider-settingsairize-color-picker-wrapdata-airize-provider-iddata-airize-button-textairizeAdmin