Advance User Post CRUD Security & Risk Analysis
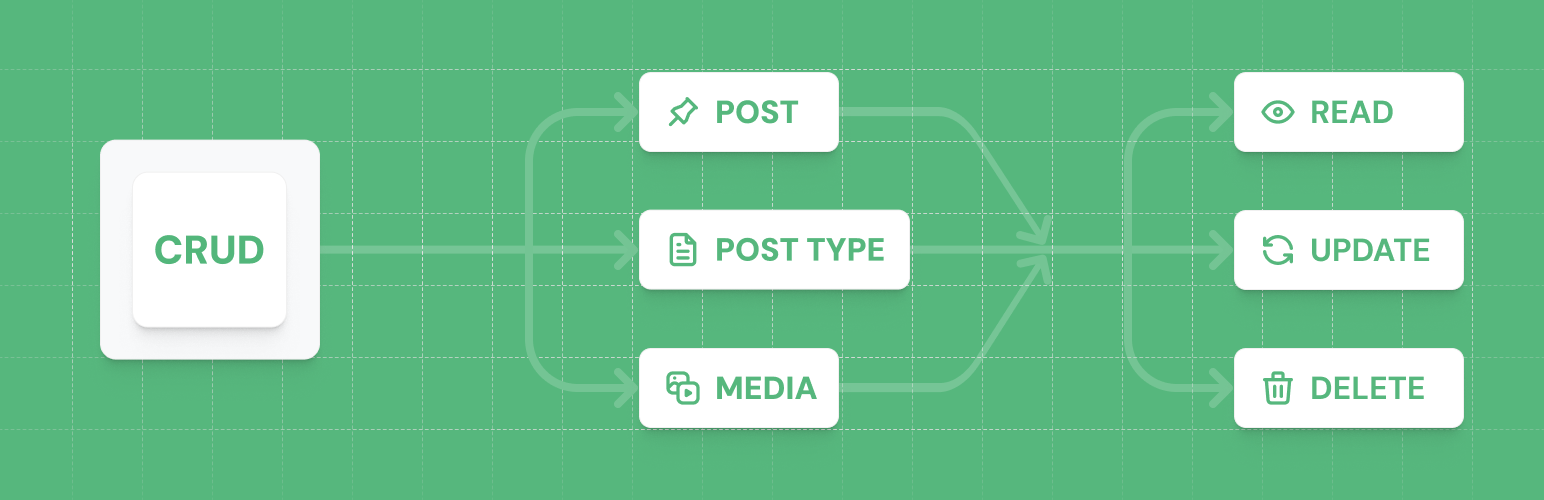
wordpress.org/plugins/advance-user-post-crudAdvance User CRUD lets you see different posts, pages and attachments created by a user. And lets you manage the user generated posts.
Is Advance User Post CRUD Safe to Use in 2026?
Generally Safe
Score 100/100Advance User Post CRUD has no known CVEs and is actively maintained. It's a solid choice for most WordPress installations.
The "advance-user-post-crud" plugin v1.3 exhibits a strong security posture based on the provided static analysis. The absence of any detected AJAX handlers, REST API routes, shortcodes, or cron events without proper authentication or permission checks significantly limits the attack surface. Furthermore, the code shows good practices with all SQL queries utilizing prepared statements and a high percentage of output escaping, along with the presence of nonce and capability checks. The vulnerability history being completely clean further bolsters confidence in its security. However, the limited number of analyzed taint flows (2) means there might be undetected vulnerabilities in areas not covered by the analysis. While the current analysis indicates a secure plugin, ongoing vigilance and comprehensive testing are always recommended.
Advance User Post CRUD Security Vulnerabilities
Advance User Post CRUD Release Timeline
Advance User Post CRUD Code Analysis
SQL Query Safety
Output Escaping
Data Flow Analysis
Advance User Post CRUD Attack Surface
WordPress Hooks 7
Maintenance & Trust
Advance User Post CRUD Maintenance & Trust
Maintenance Signals
Community Trust
Advance User Post CRUD Alternatives
Easy Post Views Count
easy-post-views-count
Add an easy post views count plugin into your site and get count views of your posts and custom post types posts like articles, news, movies etc.
Post Views for Jetpack
post-views-for-jetpack
Display the number of views for each one of your posts, as recorded by Jetpack Stats.
Post views Stats
post-views-stats
This plugins will count each post/page views by visitor.
Easy Post View Counter
easy-post-view-counter
With this plugin you can see how many views a single post has.
User Stats
user-stats
User Stats provides an easy way to see at a glance stats about your users, including: post count, post views, article costs, costs per 1000 views and …
Advance User Post CRUD Developer Profile
14 plugins · 17K total installs
How We Detect Advance User Post CRUD
Patterns used to identify this plugin on WordPress sites during automated security audits and web crawling.
Asset Fingerprints
/wp-content/plugins/advance-user-post-crud/assets/css/style.css/wp-content/plugins/advance-user-post-crud/assets/js/setting.js/wp-content/plugins/advance-user-post-crud/assets/js/setting.jsadvance-user-post-crud/assets/css/style.css?ver=advance-user-post-crud/assets/js/setting.js?ver=HTML / DOM Fingerprints
view_frontend_profile